Black Kite Third-Party Breach Report 2026
Managing Risk Concentration in the Era of Cascading Failures
by the Black Kite Research Group™
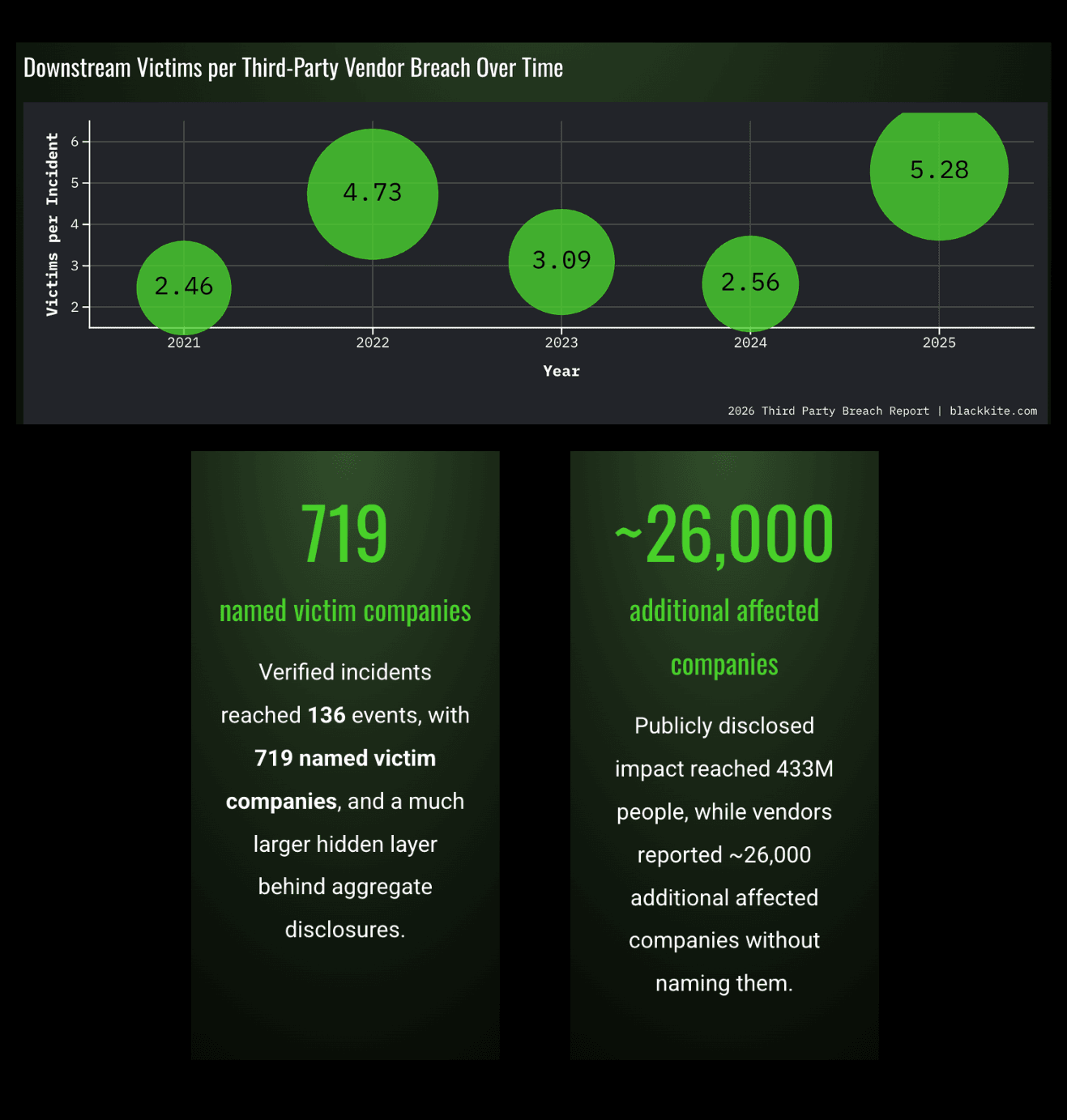
In 2025, the "blast radius" of a third-party breach reached a record-breaking threshold. Our research verified that for every single vendor breached, an average of 5.28 downstream companies were publicly compromised—the highest level observed to date. This shift proves that the modern supply chain no longer breaks at its weakest link. It breaks at its most connected one.
This definitive report by the Black Kite Research Group analyzes 136 verified breach events to reveal a new reality: impact is now cascading faster than disclosure. While attacks are detected in a median of 10 days, the public is often left in the dark for an average of 117 days, creating a "Silent Window" where thousands of unnamed victims remain exposed.
The catalyst behind this systemic fragility is Risk Concentration. To understand why these cascades are so destructive, we audited the "Elite 50," the top vendors most shared by the Forbes Global 2000. The findings are a wake-up call: 70% of these critical hubs carry unpatched, known exploits (KEVs), and 62% show corporate credentials already circulating in stealer logs.
This report is your blueprint for understanding cascading and concentrated risk—and how to protect your business from their impact.
(No download required)
2026 Third-Party Risk Statistics: Key Findings
Cascading Velocity: The 5.28x Multiplier
The story of 2025 is the unprecedented surge in the "blast radius" created by third-party incidents.
Third-Party Breach Impact Metrics
- The 5.28 Multiplier: Every single vendor breach now claims an average of 5.28 downstream victims, the highest level ever recorded.
- 719 Named Victim Companies: This represents only the "visible" portion of the impact layer identified through official public filings.
Understanding Breach Disclosure Requirements
A company is usually only "named" if the breach involves specific types of Protected Health Information (PHI) or Personally Identifiable Information (PII) that trigger mandatory disclosure laws. If a vendor breach leaks a company’s intellectual property or internal strategies but no "private" consumer data, that company might never be legally required to publicly name itself as a victim.
The Hidden Impact of Supply Chain Attacks
- The Shadow Layer: We identified an estimated 26,000 "Shadow Victims" who were impacted by these cascades but never officially named in disclosures.
Often, a breached vendor will release a statement saying:
"We have notified our 5,000 affected customers." In this scenario, the vendor has disclosed the event, but the 5,000 customers remain anonymous to the public. These are the "Shadow Victims,” because their names aren't on a public list.
Human Impact of Third-Party Breaches
- 433 Million People Impacted: The total publicly disclosed human impact reached a population roughly equivalent to the entire European Union.
Key Stats: Blast Radius
Global Vendor Security Assessment
Third-Party Risk Management Ecosystem Overview
The Vendor Ecosystem represents the expansive web of third parties analyzed in this report, comprising the security telemetry of approximately 200,000 organizations monitored on the Black Kite platform. The objective is not to analyze breached entities, but to understand the steady state security condition of the global supply chain as it exists today.
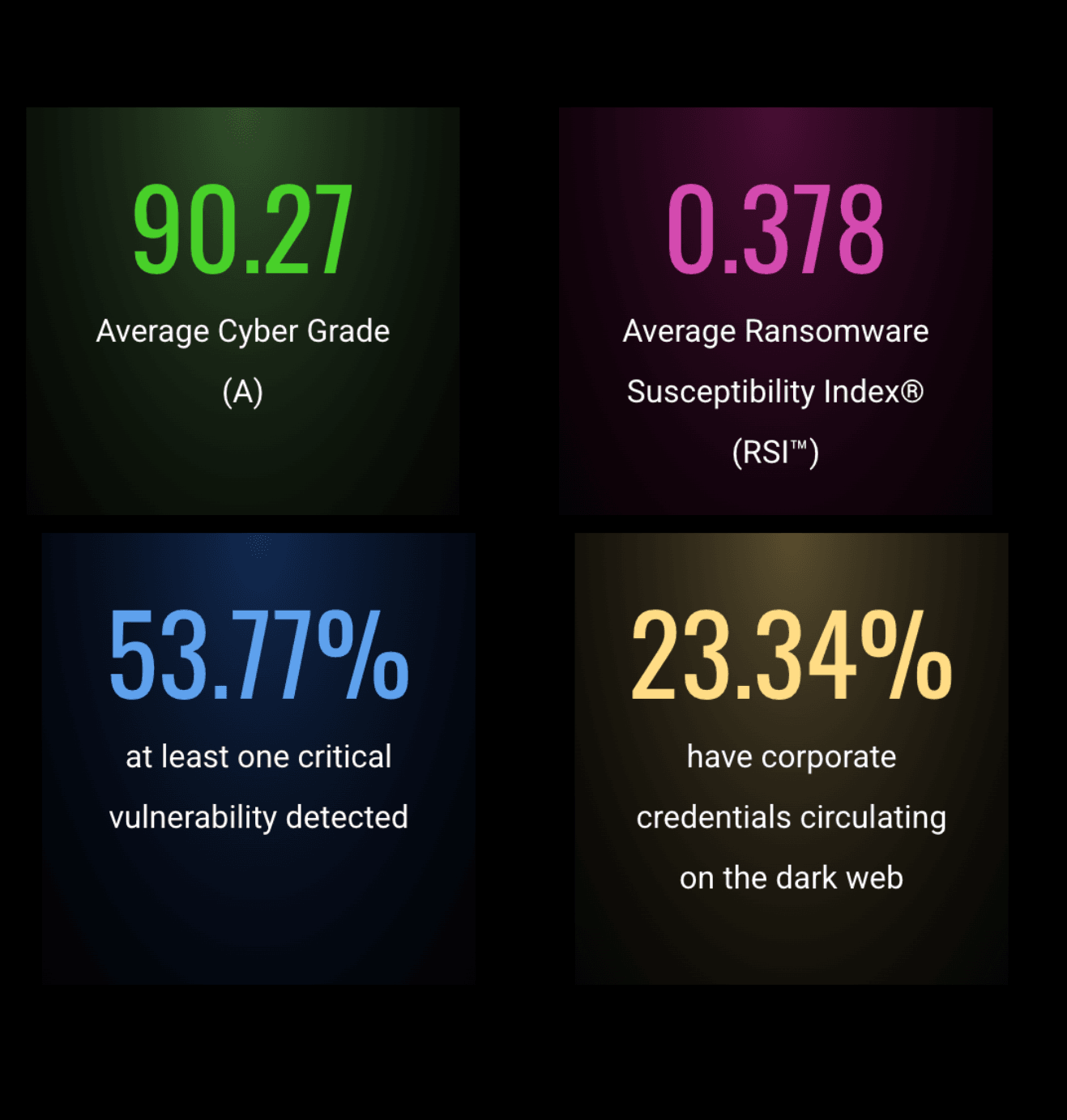
Cyber Risk Rating vs. Real Vulnerability
- 90.27 (A) Average Cyber Grade: Across the ~200,000 organizations monitored, the ecosystem maintains a high "A" average, suggesting strong baseline hygiene on paper.
- 0.378 Average RSI™: Despite the high letter grades, the ecosystem’s average Ransomware Susceptibility Index® (RSI™) sits at 0.378, teetering on the edge of the high-risk 0.4 threshold where attack probability jumps significantly.
Critical Vulnerability Management Failures
- 53.77% Patch Management Failure: Despite these high grades, over half of the organizations analyzed show at least one critical vulnerability detected, leaving known doors open for automated, opportunistic exploits that require zero manual effort from an attacker.
- 23.34% Credential Exposure: Nearly a quarter of the global ecosystem has corporate credentials currently circulating on the dark web via stealer logs, rendering traditional perimeter defenses moot.
Industry-Specific Risk Concentrations
- Industry Pressure Zones: Risk is not distributed equally across the ecosystem. Manufacturing and Education are identified as critical "Pressure Zones," where high Ransomware Susceptibility intersects with persistent gaps in operational security hygiene.
Key Stats: Vendor Ecosystem
Concentration Crisis: "Elite 50" Vendor Risk Analysis
Auditing High-Risk Vendor Concentration
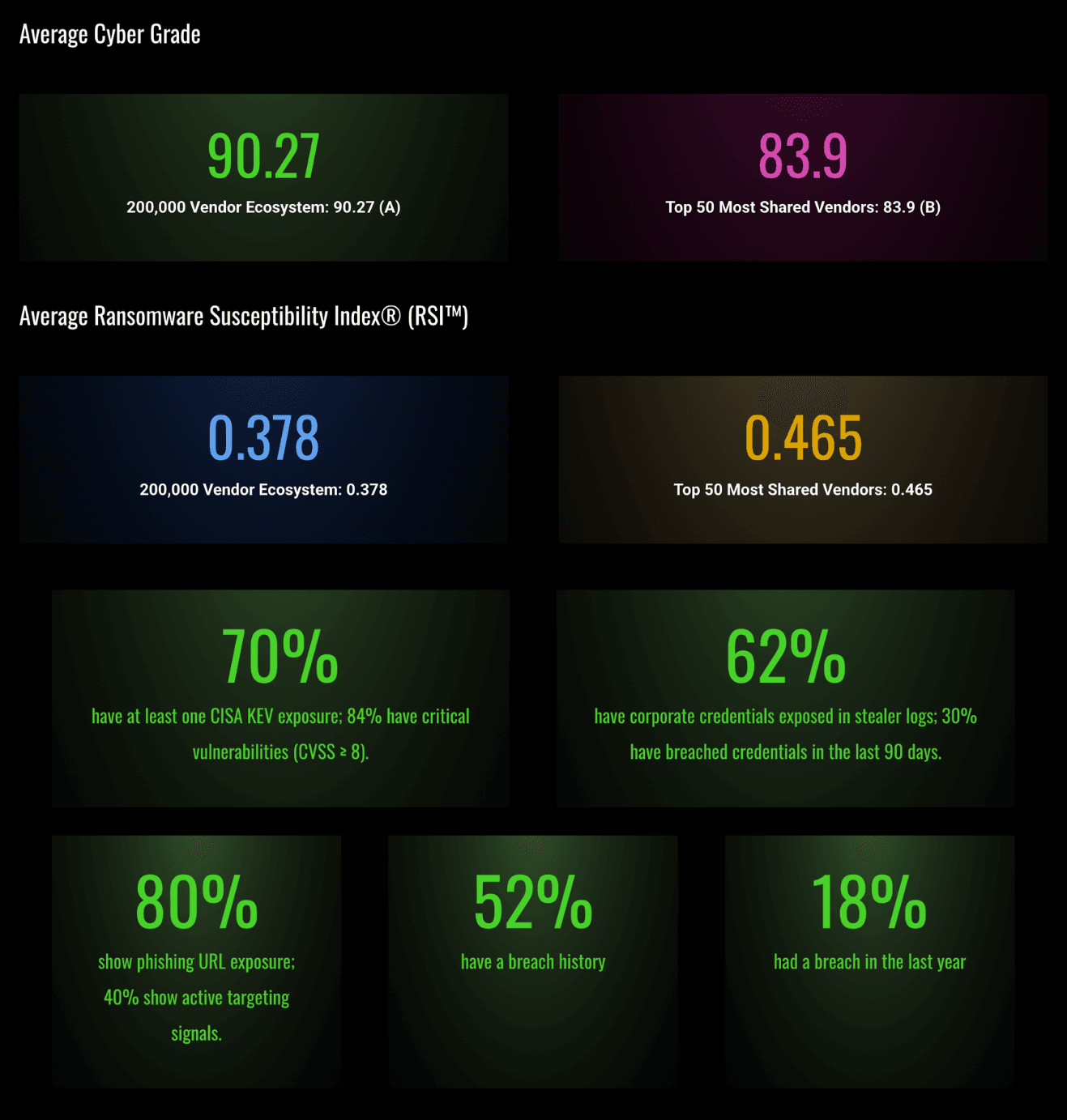
To understand the mechanics of cascading failure, the Black Kite Research Group conducted a structural audit of the "Elite 50," the top 50 third-party vendors most frequently shared by the Forbes Global 2000. These central pillars represent a massive concentration of risk. They are the cloud providers, software conglomerates, and financial gateways that the global economy relies upon.
The study reveals that these hubs are not the digital fortresses we assume them to be. Instead, they are stressed infrastructure where vulnerability at a single point can trigger a systemic collapse across thousands of downstream organizations.
Elite Vendor Security Posture Analysis
- 83.9 (B) Average Cyber Grade: Despite their scale and resources, the "Elite 50" maintain a lower average security posture than the general ecosystem, signaling that high-growth connectivity often outpaces security hardening.
- 0.465 Average RSI™: The "concentrated core" of the global supply chain isn't just flirting with risk. These vendors sit well within the high-danger zone, as companies with an RSI value above 0.4 are 11.6x more likely to experience a ransomware attack than those below 0.2.
Critical Exploitable Vulnerabilities in Top Vendors
- 70% KEV Exposure: Seven out of ten of these critical hubs have at least one unpatched vulnerability currently listed in the CISA KEV catalog. These are not "theoretical" risks; they are vulnerabilities known to be actively exploited by threat actors today.
- 62% Master Key Leakage: Over 60% of these central vendors have corporate credentials circulating in stealer logs. These act as "master keys," allowing attackers to bypass traditional perimeters and log directly into vendor environments as legitimate users.
Advanced Threat Exposure Metrics
- 80% Phishing URL Exposure: The vast majority of these critical vendors have active phishing URLs currently impersonating their brands, creating a massive identity-theft surface for their Global 2000 customers.
- 52% Data Breach History: More than half of these "Elite" shared vendors have already suffered at least one verified data breach, proving that even the most established names in tech have already been successfully breached.
- 18% Breached in the Last Year: Nearly one in five of these "Elite" shared vendors has suffered a verified breach in the last 12 months.
Key Stats: Top 50 Vendors
Breach Detection vs. Disclosure Timeline Analysis
The Widening "Silent Window" in Third-Party Risk
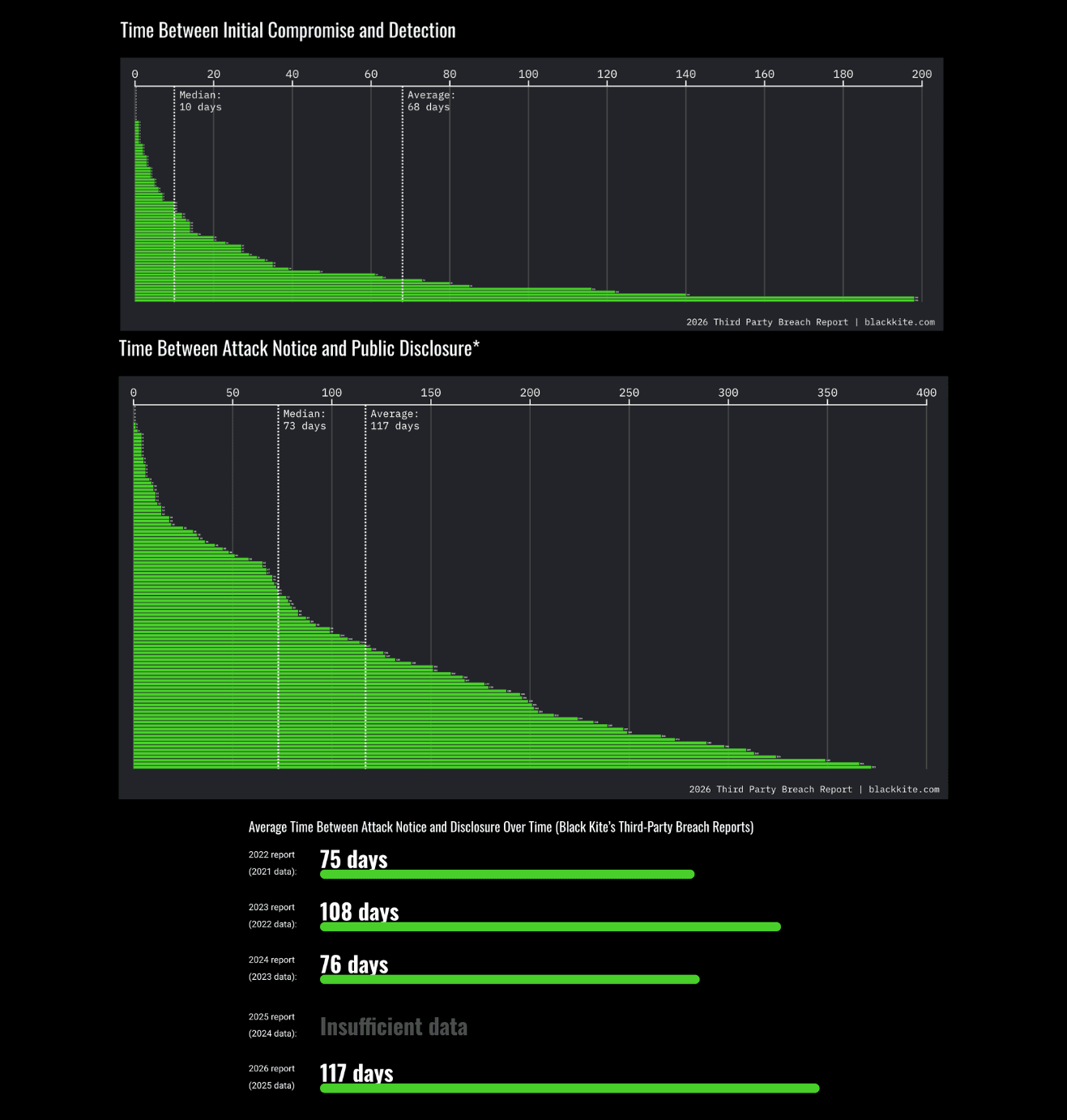
The final piece of the 2025 risk puzzle is the breakdown in transparency. Vendors are finding breaches faster, but they are taking significantly longer to inform the public. This proves that you cannot rely on official notifications to manage your real-time risk.
Breach Discovery and Communication Gaps
- 10-Day Median Detection: Most vendors identify a compromise within a relatively swift 10-day window.
- 117-Day Average Disclosure: It now takes an average of nearly four months for a breach to be publicly disclosed after discovery.
- 73-Day Median Delay: Even at the median level, risk remains undisclosed for over two months.
- The Information Gap: The disclosure window has worsened, regressing from an average of 76 days in 2024 to 117 days in 2025.
Key Stats: Compromise, Detection, and Disclosure Gaps
Advanced Third-Party Risk Management Strategies
From Reactive Risk to Concentration-Aware Resilience
Protecting your business in 2026 requires a shift toward active intelligence and systemic awareness.
Strategic Risk Concentration Management
- Map Your "Fragile Core": Identify the central nodes in your supply chain that, if compromised, would trigger a cascading failure across your operation.
- Shrink the "Silent Window": Implement continuous monitoring via FocusTags® risk intelligence to gain real-time visibility into the "active threat layer" before a breach is disclosed.
- Prioritize "Pressure Zone" Remediation: Use the Ransomware Susceptibility Index® (RSI™) to prioritize outreach to vendors in high-risk zones, regardless of their letter grade.
- Assume Breach at the Core: Shift from compliance to operational resilience by modeling the financial and operational impact of a failure at your most concentrated points of dependency.
Third-Party Breach Report Methodology: Data Integrity and Verification
To ensure the highest level of accuracy, the 2026 report utilizes a multi-layered research framework:
Comprehensive Breach Analysis Framework
Verified Data Scope: Our research is based on the rigorous analysis of 136 verified third-party breach events and 719 publicly named victim companies. Unlike reports that rely on anecdotal evidence, every incident in this study has been substantiated through public disclosures, regulatory filings, and verified news reports.
Advanced Risk Intelligence Methodology
The Shadow Layer Analysis: We go beyond named victims by analyzing aggregate disclosures, cases where a vendor reports impact to their customer base without naming specific organizations. In 2025, this led to the identification of an estimated 26,000 additional "Shadow Victims" who remained in an undisclosed state of compromise.
Global Ecosystem Intelligence
Ecosystem Telemetry: The report leverages cybersecurity posture data from approximately 200,000 organizations worldwide. This allows our team to benchmark the "Elite 50" shared vendors against the general ecosystem using a standardized scoring methodology.
Proprietary Risk Assessment Integration
Proprietary Risk Indicators: We utilize the Ransomware Susceptibility Index® (RSI™) and FocusTags® to correlate observed technical failures, such as unpatched KEVs and exposed credentials in stealer logs, with the eventual outcome of a cascading breach.
Access the Complete 2026 Third-Party Breach Report Now
Previous editions:
