Supply Chain Cyber Risk Management
Cyber Risk Doesn't Stop at Your Direct Suppliers.
A breach at a tier-3 supplier doesn’t stay isolated. It can ripple through interconnected supply chains and impact your operations. Black Kite maps the cyber risk posture of entire supplier ecosystems, including the Nth-party relationships many organizations lack visibility into.

The Problem With Compliance-First C-SCRM
Most supply chain risk management processes are built around frameworks and periodic assessments. That's a starting point, not a finish line. For organizations that have traditionally measured supply chain risk in physical terms, cyber risk is often the last thing to receive rigorous attention. Yet suppliers represent a direct source of cyber risk to an organization’s operations.
Here's what compliance-first C-SCRM programs consistently get wrong.
Frameworks Define Process, Not Posture
NIST SP 800-161 establishes a rigorous supply chain risk management process. But a framework tells you what controls should be in place, not what's actually happening inside your supplier ecosystem right now. Documented compliance and real cyber visibility are not the same thing.
Assessments Give You a Snapshot
Questionnaires and periodic reviews capture a moment in time. Suppliers are patching (or not patching), credentials are leaking, and ransomware groups are actively targeting industrial and logistics sectors. None of that waits for your next assessment cycle.
Checking the Box Isn't Enough
Completing a C-SCRM framework checklist doesn't mean you have full visibility into your supply chain's true cyber risk posture. The gap between documented compliance and real-world exposure visibility is where risk often goes unnoticed, and it’s a gap many SCRM programs struggle to close.
The Risks Hiding in Plain Sight
Cascading and concentration risk exist in supplier dependencies, and are often overlooked by compliance-driven programs. Understanding how cascading and concentration risk impact your digital supply chain is key to gaining a more complete view.
Two Threats Most C-SCRM Programs Miss
The most damaging supply chain cyber events don't originate from a single weak supplier. They spread through connections. The impact of concentration and cascading risk is real, and these are threats most programs aren't built to see.
Cascading Risk
Cascading risk occurs when a cyber event at one supplier ripples outward: into your systems, your customers' systems, and the systems of every other organization that depends on the same underlying provider. This cascading cyber risk doesn't respect organizational boundaries. A compromised software supplier or shared cloud platform doesn't just affect one company. It affects everyone connected to it.
According to Black Kite's research, every single supplier breach now claims an average of 5.28 downstream victim organizations, the highest multiplier ever recorded.
Concentration Risk
Concentration risk occurs when too many suppliers in your chain depend on the same underlying technology, infrastructure, or Nth-party provider, creating a single point of failure. It's not about how many suppliers you have. It's about how many of them share the same hidden dependencies.
Black Kite's 2026 research found that 70% of top 50 vendors shared by the Global 2000 carry at least one unpatched vulnerability from the CISA KEV catalog and 62% of them have leaked credentials on the dark web. When concentration is high, a single compromise doesn't just break one link. It breaks the whole chain at once.
Get Nth-Party Visibility Beyond Your Suppliers
Most supply chain risk management processes stop at direct suppliers. But risk extends further, into fourth-party providers, shared infrastructure, and common technology platforms that your suppliers depend on.
Black Kite's Supply Chain module automatically maps fourth-, fifth-, and Nth-party relationships, surfacing hidden dependencies and concentration points to deliver deep intelligence across the entire supply chain. This gives teams a clearer view of risk across the supply chain and the ability to move beyond framework compliance toward more informed, continuous supply chain risk management.

Anticipate Ransomware Risk Across Your Supply Chain
Ransomware can significantly disrupt the supply chain.
Black Kite's Ransomware Susceptibility Index® (RSI™) analyzes the technical and behavioral indicators that make a supplier susceptible to a ransomware attack, giving teams the intelligence they need to prioritize risk before an attack disrupts operations.
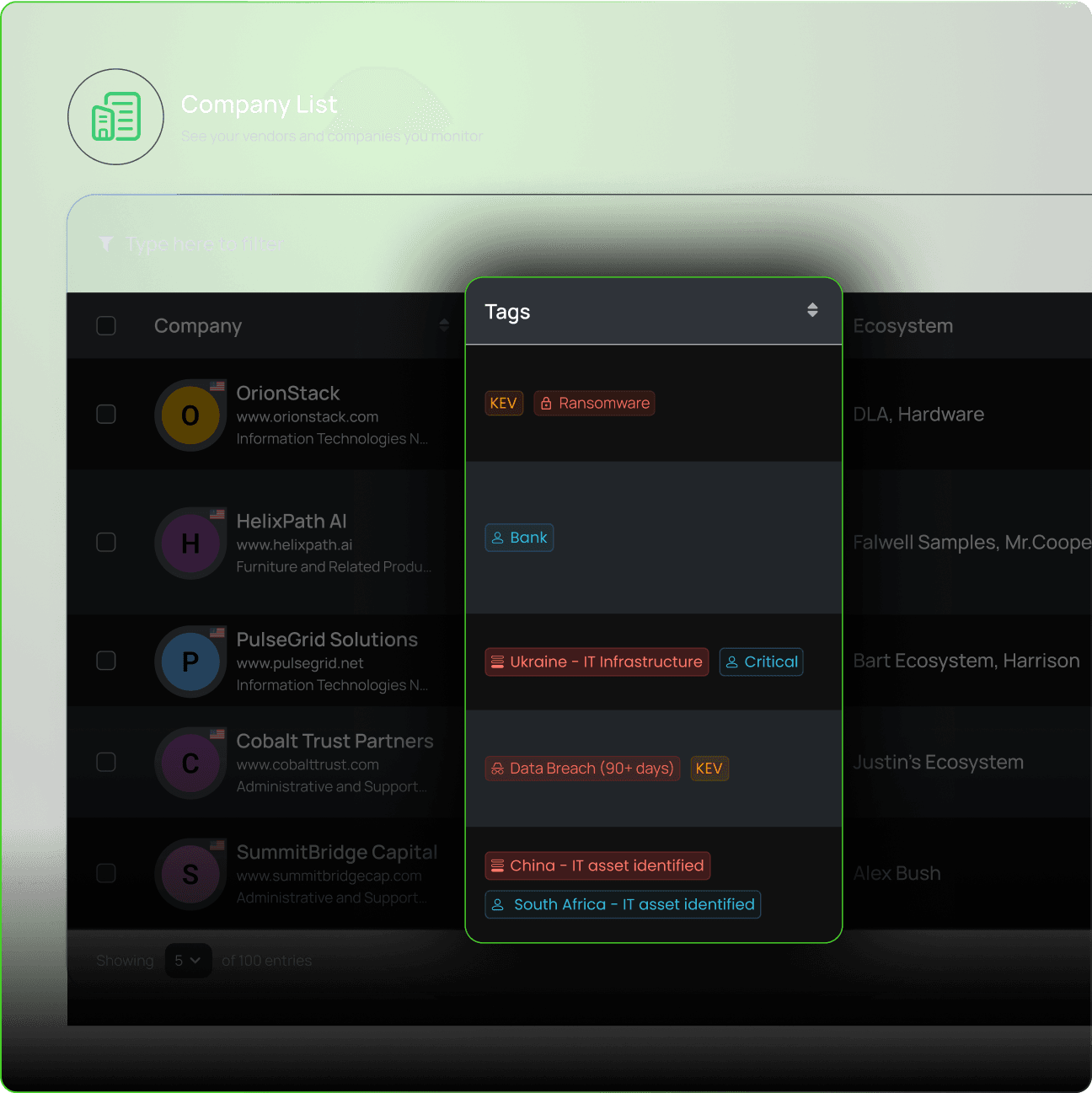
Get Real-Time Supply Chain Risk Intelligence With FocusTags®
When a real-world cyber event (an active exploit, a critical vulnerability, a known threat actor campaign) hits your supplier ecosystem, you need to know immediately – you can’t wait until the next assessment cycle.
Black Kite’s FocusTags® flag supply chain events the moment they emerge, tying contextual, actionable supply chain threat intelligence directly to the suppliers in your ecosystem. When MOVEit was being exploited, when CrowdStrike went down, Black Kite customers knew which of their suppliers were exposed in real time so they could promptly act.
Explore cyber risk intelligence for a deeper look at FocusTags® →

Extend Visibility Across Your Entire Supplier Ecosystem
For organizations that need full supply chain cyber risk management at enterprise scale, Black Kite Extend delivers the complete picture. Nth-party mapping, geopolitical monitoring, threat actor tracking, and product-level risk analysis, all in one package.
Whether you're managing a global manufacturing supply chain, a complex wholesale and retail network, or a public sector supplier portfolio with C-SCRM compliance obligations, Black Kite Extend gives teams the depth of visibility that modern SCRM requires.