

Ransomware Threat Intelligence for Your Vendor Ecosystem
Generic Threat Feeds Don't Tell You Which of Your Vendors Is Susceptible to Ransomware.
Black Kite connects ransomware threat intelligence directly to your third-party risk program through the Ransomware Susceptibility Index® (RSI™), the world's first and only ransomware indicator tool built to predict which vendors are most likely to be hit, so you can move from global threat awareness to vendor-specific ransomware visibility — before an incident occurs.

What Ransomware Threat Intelligence Actually Requires
Ransomware doesn't just threaten your internal systems. It travels through your vendor ecosystem, hitting a supplier or software provider and cascading downstream until it reaches your operations.
Many cyber threat intelligence programs are heavily retrospective, as they rely on observed and reported attacks, known Indicators of Compromise (IOCs), and documented Tools, Techniques and Procedure (TTPs). While this enables action based on confirmed or ongoing activity, it remains focused on what has already happened or is currently unfolding.
However, when it comes to ransomware, a proactive approach is critical. Organizations need to identify risks early and map this intelligence to their specific vendor ecosystem to understand which vendors are most susceptible right now. This allows teams to engage vendors before an attack occurs, close security gaps, and implement mitigations that prevent disruption.
Predict Vendor Ransomware Susceptibility
How the Ransomware Susceptibility Index® Works
Black Kite’s Ransomware Susceptibility Index® (RSI™) analyzes real attack patterns from thousands of confirmed ransomware victims, correlates them against environmental indicators in each vendor's current digital footprint (exposed vulnerabilities, misconfigured systems, leaked credentials, exploitable software versions) and surfaces predictive ransomware susceptibility indicators specific to that vendor.
It reflects the ransomware mindset: how ransomware operators weigh ease of access, profitability, geopolitical factors, and media visibility when selecting targets. And it is continuously updated as the ransomware landscape shifts. Not a static rating, but a live signal.
Black Kite’s RSI™ is a battle-tested predictor our customers rely on. Black Kite's 2025 Ransomware Report found that 47.3% of companies with an RSI above 0.8 experienced a ransomware attack, compared to just 0.5% of companies with an RSI below 0.2, making high-RSI companies 96 times more likely to be attacked. RSI acts as an early warning, since scores often rise within six months before an attack.

From Ransomware Risk Intelligence to Action
RSI™ translates susceptibility indicators into prioritized risk decisions, informing:
- Which vendors need an immediate remediation conversation
- Which require ongoing monitoring
- Which represent acceptable exposure given your program's risk tolerance.
RSI™ gives risk teams a clear, evidence-backed, prioritized list of vendors that require attention. This is especially valuable for organizations with vendors in high-risk industries like manufacturing, financial services, and healthcare. Teams use RSI™ to focus resources across hundreds or thousands of vendor relationships, with confidence that the prioritization reflects real-world ransomware targeting patterns.
Predict Vendor Ransomware Susceptibility
The gap between when an incident occurs in your third-party ecosystem and when it is officially disclosed can be months. That Silent Window is a massive transfer of risk to every downstream organization in a vendor's ecosystem. FocusTags® eliminate that lag.
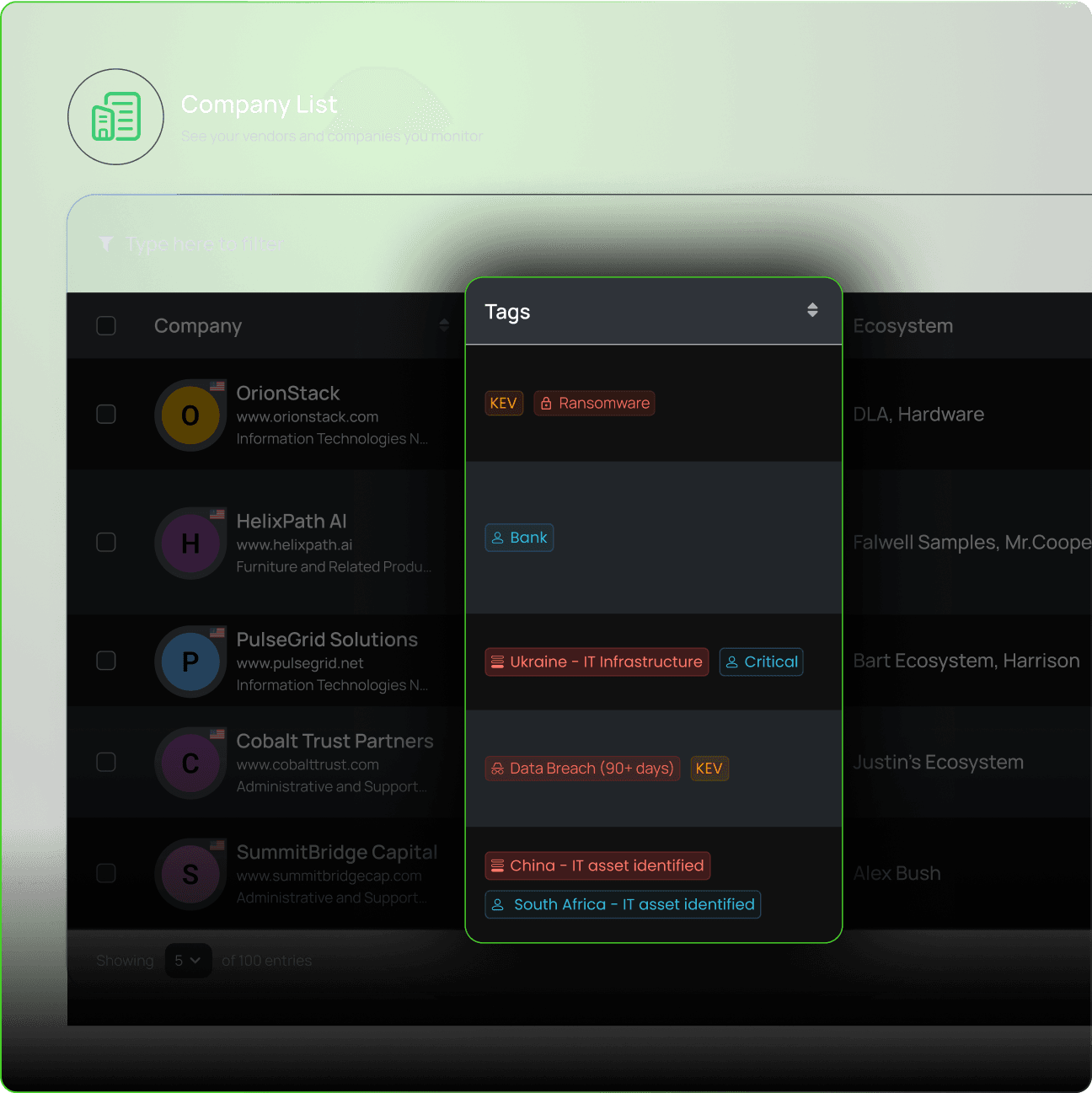
Get alerted
When a major breach, ransomware attack, or active exploitation of a vulnerability occurs, Black Kite FocusTags® are automatically applied to any affected vendors in your portfolio, giving your team immediate threat detection and visibility where risk lies so they can take timely action.
When the Blue Yonder ransomware incident surfaced in November 2024, Black Kite issued a FocusTag® just two days later — before most organizations had mapped their indirect exposure. When the Cleo file transfer vulnerability (CVE-2024-50623) emerged weeks later, Black Kite identified over 2,000 assets running vulnerable software versions and issued a FocusTag® with asset-level specificity, helping a Fortune 40 retailer initiate a critical vulnerability campaign before the issue gained wider attention. When time is of the essence, FocusTags® enable teams to quickly understand exposure and take action.
Track the Adversaries Targeting Your Vendors
Knowing which threat actors are most likely to target your vendors is essential for managing risk.
Black Kite's dark web ransomware threat monitoring continuously tracks what ransomware operators and threat actors are discussing, planning, and claiming across leak sites, Telegram channels, and dark web forums. The Black Kite Research Group™ monitored over 150 ransomware groups in the most recent Ransomware Report, with 96 meeting the threshold of active status. The collapse of dominant syndicates like LockBit and AlphV and the emergence of dozens of smaller less predictable groups (each deploying distinct ransomware variants), makes adversary intelligence more critical than ever. A more fragmented threat landscape and the pace of emerging threats leads to less predictable targeting and makes risk harder to anticipate.
Black Kite’s Adversary Susceptibility Index™ (ASI™) takes adversary intelligence one step further: it identifies which threat actors are most likely to target specific organizations, giving TPRM teams actionable intelligence to guide vendor outreach and mitigation.

Ransomware Visibility Beyond Your Direct Vendors
A ransomware attack at a fourth or fifth party can cascade through interconnected supply chain layers and impact your operations. These silent breaches are especially difficult to manage because they originate entirely outside your direct vendor relationships.
Black Kite maps Nth-party dependencies so that concentration risk (multiple critical vendors sharing a common underlying infrastructure, software library, or geographic region) doesn't become a single point of failure. Black Kite's 2025 Ransomware Report documented a significant rise in exactly this pattern: supply chain warfare, where a single compromised provider disrupted dozens to hundreds of downstream organizations. The ransomware operators behind these campaigns aren't attacking indiscriminately, they're deliberately targeting vendors whose compromise creates the greatest cascading impact. Black Kite gives you visibility into Nth party relationships so you can manage risk across the extended supply chain.

FAQs About Ransomware Threat Intelligence
Ransomware Intelligence Resources
See which vendors need your attention for ransomware susceptibility.
Knowing a ransomware group is active tells you something. Knowing that three of your tier-one vendors show susceptibility indicators trending upward, which historically happens in the weeks leading up to an attack, tells you something you can act on.

