Beyond Ransomware: The (Non-Ransom) Effects of Ransomware
Written by: Black Kite
This month, the White House released its National Cybersecurity Strategy. The 39-page document details a five-pillar strategy to “better secure cyberspace and ensure the United States is in the strongest possible position to realize all the benefits and potential of our digital future.” One of the biggest takeaways from the strategy? Ransomware is now classified as a national security threat.
The cybersecurity industry has been raising the flag about ransomware for years. But now that ransomware is classified as a national security threat, hopefully it will get the attention it deserves. Organizations should consider this development as a signal to narrow their focus on preventing and remediating the effects of ransomware.
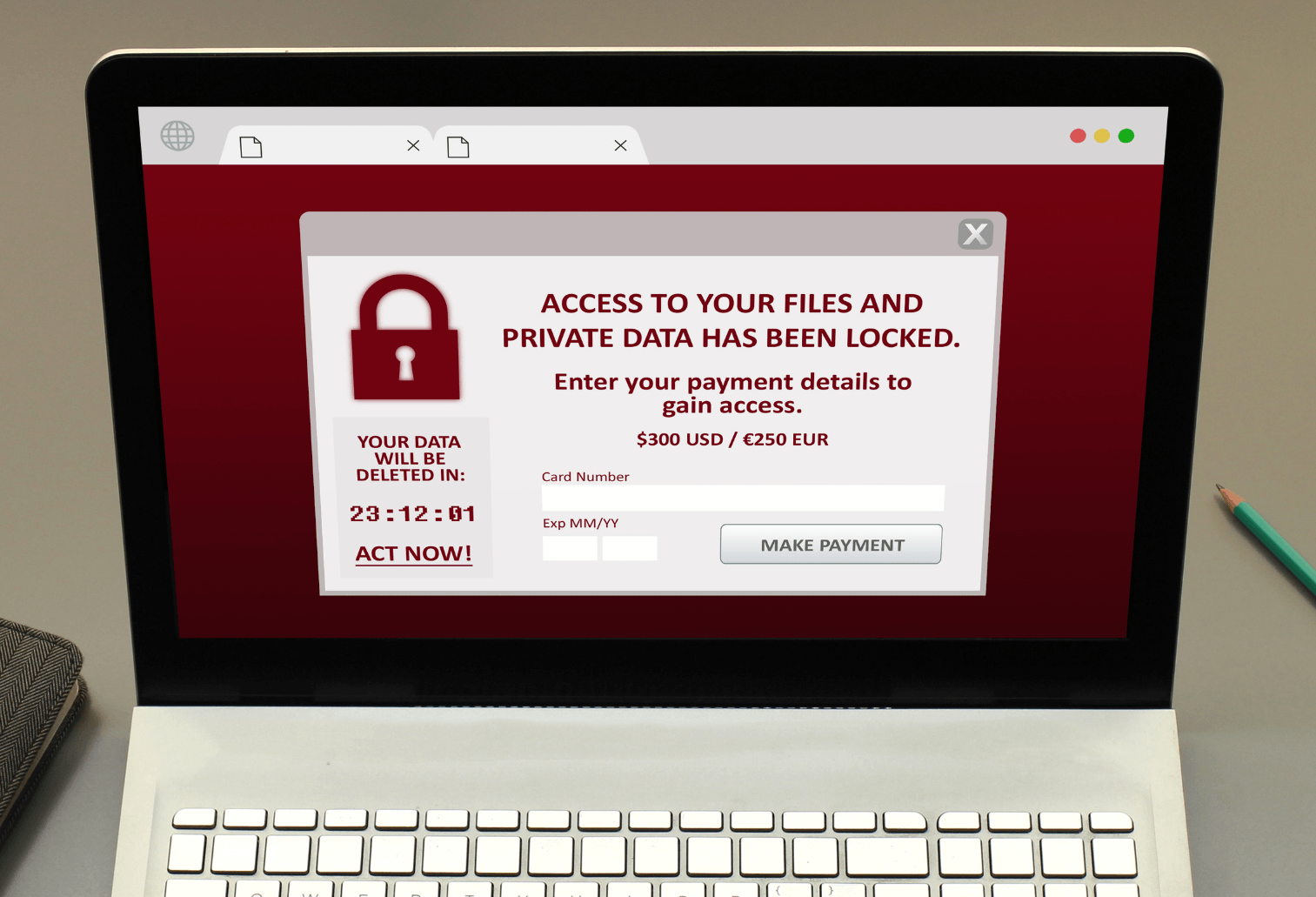
When people think about ransomware, there’s a tendency to focus on the ransom. Not only is “ransom” in the name, but the ransom is also one of the more publicized effects of this particular type of malware.
It’s time to take a more expansive view of ransomware. A ransomware attack is akin to tossing a stone into a pond — you’ll see ripples that go far beyond the ransom itself. Let’s look deeper into what organizations need to understand about ransomware as it becomes a bigger conversation.
The evolution of ransomware
In the first half of 2022, there were over 200 million ransomware attacks around the world. With such a large number, it’s also no surprise that ransomware was the second most common cause of third-party breaches in 2022.
It’s also clear that ransomware actors are growing bolder. In our 2023 Third-Party Breach Report, we found that ransomware actors were the most likely of any type of threat actor to publicly lay claim to an attack. Part of the notoriety comes from their willingness to target government agencies, healthcare organizations, the education sector, and corporations. Last year, the Cybersecurity and Infrastructure Security Agency reported that all but two of the U.S.’s 16 critical infrastructure sectors were attacked by ransomware actors.
We’re also seeing that ransomware actors are increasing the sophistication of their attacks, which means that the individual effect of each breach is much higher. In fact, we found that between 2021 and 2022, the average number of companies affected by a single breach nearly doubled, jumping from 2.46 companies to 4.73.
The ubiquity of attacks and the wide range of industries affected makes this a top-of-mind issue for most organizations, private and public. There’s also the ransom. Spoiler alert: ransomware groups are demanding more.
Ransomware comes with a…ransom
We know, it’s in the title, but when you really consider the money extorted as a result of ransomware, the figures are sobering:
- In 2022, attackers extorted over $400 million from victims.
- Last year, the average extorted amount in business sector ransomware attacks rose from $8.4 million in 2021 to $13.2 million.
- In 2021, a Russia-based hacking group targeted the Colonial Pipeline in the U.S. and extorted a ransom of $4.4 million dollars from the U.S. government.
As ransomware averages increase, we also see record-breaking ransoms. Last year, the ransomware group LockBit targeted automotive parts company, Continental, and demanded a ransom of $50 million – the largest ransom then. However, LockBit topped that figure earlier this year with a ransom demand of $80 million dollars in the Royal Mail ransomware attack. While ransoms are probably the most publicized effect of ransomware, the impact of ransomware is wide-ranging and long-lasting after the ransom itself has been paid.
What are the other effects of ransomware attacks?
Ransomware is a type of malware that targets the files of a system, encrypting them so that they’re unusable until the individual/organization pays a ransom for the decryption key. As we know, the ransom figures themselves are nothing to sneeze at. But there’s an old saying, “when it rains, it pours.” Read on for some of the other effects of ransomware attacks.
Business disruption
Inaccessible files due to a ransomware attack can negatively impact an organization’s ability to function across departments and slow their capacity to move in the market. What this looks like is different across industries:
- Business disruption in healthcare: An inability to access patient files, pharmacy records, or even insurance information can delay surgeries and prevent patients from receiving life-saving medications and proper care in a timely manner.
- Business disruption in manufacturing: Encrypted client order files, inventory records, and even production processes can prevent a business from fulfilling orders, sending proper invoices, and making monthly production quotas. When the manufacturer produces medical devices, this can potentially affect the lives of many.
- Business disruption in financial services: Encrypted client financial files can prevent clients from accessing their money. Organizations may be unable to trade, acquire other companies, or perform several actions, putting them in a precarious financial position.
Reputation damage
Many ransomware attacks go unreported. For some organizations, it’s easier to quietly pay the ransom, retrieve their files, and continue operating normally. Their clients, partners, and sometimes even employees outside of certain departments never know that the company’s information has been compromised.
Why would companies hide a ransomware attack? Often, they fear that the risk to their reputation is too great. Companies that fall victim to ransomware might be viewed by their clients as unreliable. This is especially true of financial services organizations or companies whose reputations are closely tied to building client trust.
Other organizations consider the impact of server-side business disruption and how it can lead to reputational damage and business loss. For example, if a retail company is hit with ransomware and cannot fulfill customer orders for a few weeks, frustrated clients may cancel their orders or flood the retailer with poor customer service reviews. This can ultimately affect their ability to attract new clients.
Clean-up costs
When a ransomware attack occurs, companies can’t simply pay the ransom and return to business as usual. There can be significant remediation costs in addition to the ransom itself:
- Attorney fees and litigation costs: This could include lawsuits from clients who have had PII compromised, lawyer consultation fees, or even the cost of prosecuting threat actors.
- Insurance premiums: In 2020, cyber insurers experienced an influx of claims and raised rates accordingly. In the past two few years, organizations have seen premium rates increase 50 – 100%.
- Public relations fees: It can be expensive to hire a firm or individuals to communicate the appropriate background on the ransomware attack, its aftermath, and how a company will move forward. This can be a necessity to establish goodwill with affected clients, however.
- Device/software replacement costs: A compromised system may require significant security upgrades to prevent similar attacks from occurring in the future. This can include security patches or replacing outdated devices and software.
- Regulatory fines and fees: If a company fails to comply with regulatory bodies when a ransomware attack occurs, it could be subject to fines and fees in addition to other clean-up costs. In a recent case, the Securities and Exchange Commission (SEC) settled charges against Blackbaud, a cloud software provider. Blackbaud hid the impact of a 2020 ransomware attack and is now responsible for paying a $3 million civil penalty to the SEC and for settling the various consumer class action suits against it.
What’s next for ransomware
When ransomware attacks began, they usually targeted personal computers. As ransomware techniques grew in sophistication, however, attackers began targeting corporations capable of paying much larger, “big game” ransoms.
We’ve also seen an increase in the collateral damage ransomware can cause. Due to supply chains and business partnerships, ransomware doesn’t just affect the targeted company; attackers can often access third-party vendors’ data via their original target’s data and disrupt a secondary vendor’s supply chain by incapacitating their primary target. In general, the increasing interconnectedness of network infrastructures has made ransomware more potent. A single organization may find it difficult to limit an attacker’s access to data in the event of an attack.
Ransomware variants are also growing by leaps and bounds. Twice as many new variants were found in the first half of 2022 as in the latter half of 2021. The increase in variants is attributed to the growth of ransomware-as-a-service (RaaS), which allows ransomware operators to sell their ransomware to affiliates.
As new actors, technologies, and targets arrive on the scene, we’ll continue to see an evolution in ransomware and its effects.
How does Black Kite help with ransomware?
At Black Kite, we monitor the dark web to better understand how ransomware groups behave, their motivations, and their evolving techniques. We’ve leveraged our research and unique “attacker perspective” to develop a Ransomware Susceptibility Index (RSI), which tells you the likelihood of a vendor or organization experiencing a ransomware attack.
For our RSI ratings, we collect data from OSINT sources that are inspected, transformed, and modeled through machine learning and other data analysis techniques. We evaluate each company’s security posture against a control set of 1,000 companies with “good” security practices. Here’s a list of the common technical indicators of ransomware attacks that RSI checks when assessing a company:
- Industry
- Email security
- Company size
- Leaked credentials
- Endpoint security
- Vulnerabilities with remote code execution
- Phishing or fraudulent domains
- Open critical ports
- Stealer logs
Black Kite’s RSI ratings equip organizations with the intel they need to understand their vendors’ ransomware risk, and by extension, their own. Most importantly, our RSI computation methods are constantly evaluated and adapted to reflect emerging risk indicators.
Sophisticated ransomware requires sophisticated solutions
As ransomware changes and evolves, it’s growing in severity and impact. Organizations are often disadvantaged without the staff, security solutions, and intel to adequately protect themselves against ransomware attacks. Black Kite’s RSI provides the crucial data that organizations need to make fast, intelligent decisions that reduce their attack surface, improve their security posture, and avoid ransomware attacks and their effects.
Don’t let ransomware fly under the radar.
Get started with a free RSI rating today!