
RANSOMWARE SUSCEPTIBILITY INDEX®
Identify Ransomware Risk in Your Third-Party Ecosystem
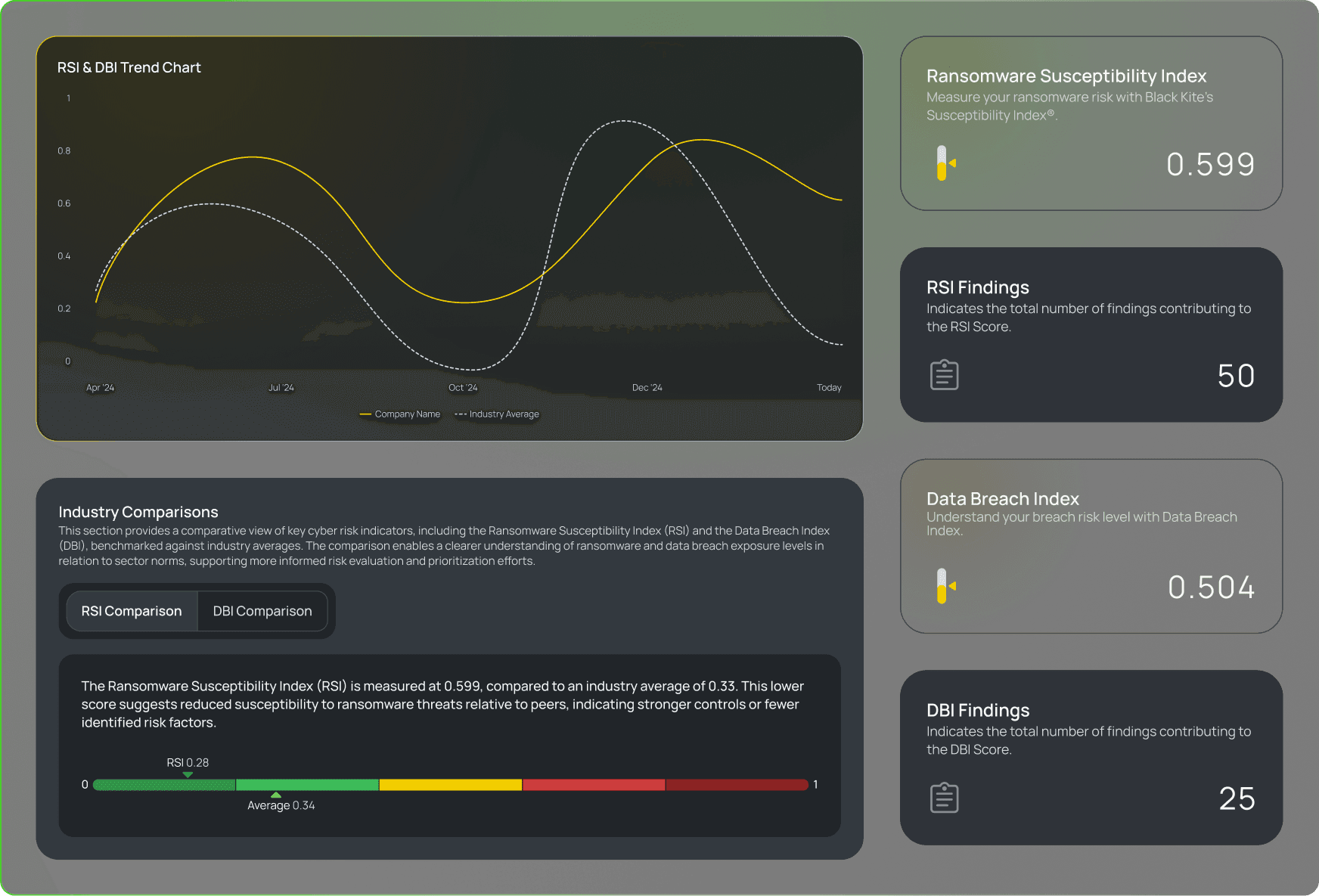
Black Kite’s Ransomware Susceptibility Index® (RSI™) measures the likelihood of which vendors are most likely to be hit next, using real-time signals to spotlight risk before attackers make a move.
Ransomware groups are after your supply chain.
Ransomware is rising, with a 123% increase in victims over two years. Attackers know the easiest way in isn’t always the front door. They are increasingly targeting vendors in your supply chain with thinner defenses, lower risks of retaliation, and higher chances of disruption.
2025 Ransomware Report: How Ransomware Wars Threaten Third-Party Cyber Ecosystems

Know the Likelihood of a Ransomware Attack in Minutes.
Ransomware groups don't pick victims randomly. The Ransomware Susceptibility Index® reflects the evolving patterns of threat actors’ tactics, techniques, and procedures (TTPs). This isn't theoretical; it's real-world probability based on data from thousands of confirmed ransomware victims each year.
With RSI, you can:
Companies with an RSI between 0.8 and 1.0 are 96x more likely to experience a ransomware attack than companies with an RSI value below 0.2.

Don’t Leave Ransomware to Chance
Black Kite’s RSI™ tracks common ransomware indicators to discover the likelihood that an organization will experience an attack.
Ransomware Common Indicators:
- Vulnerabilities with remote code execution
- Open critical ports
- Phishing or fraudulent domains
- Leaked credentials
- Company size
- Company industry
- Stealer logs
- Endpoint security
- Email security
- Geolocation

Spot Ransomware Risk Months in Advance. Before It Strikes Your Vendors and You.
The average ransomware victim doesn't just have a high Ransomware Susceptibility Index; they often show a clear pattern of increasing risk leading up to an attack. By tracking RSI fluctuations, TPRM teams can spot early signs of a vendor's vulnerability months in advance.



