Evolving Compliance Frameworks Outpace Manual Tracking
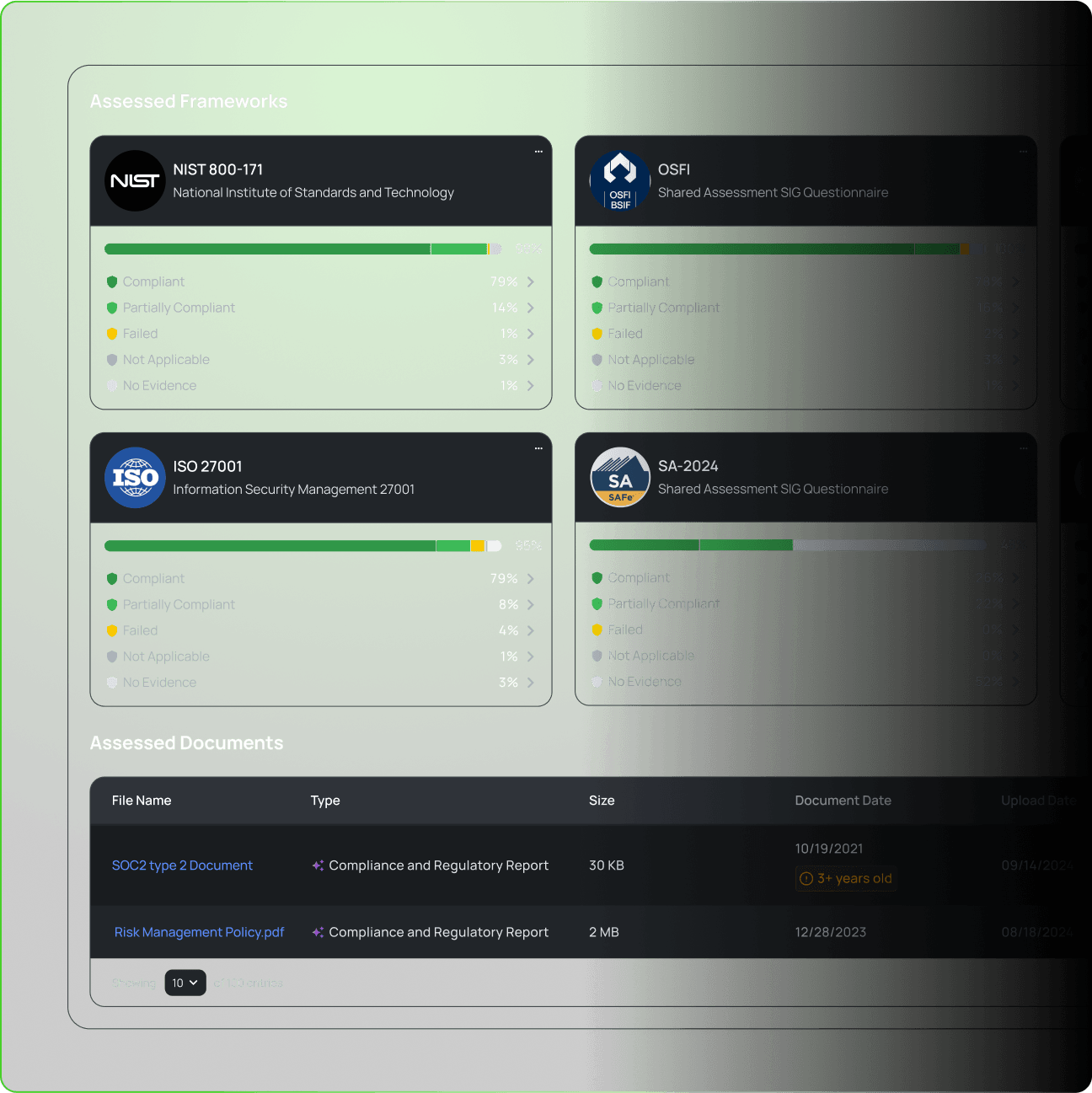
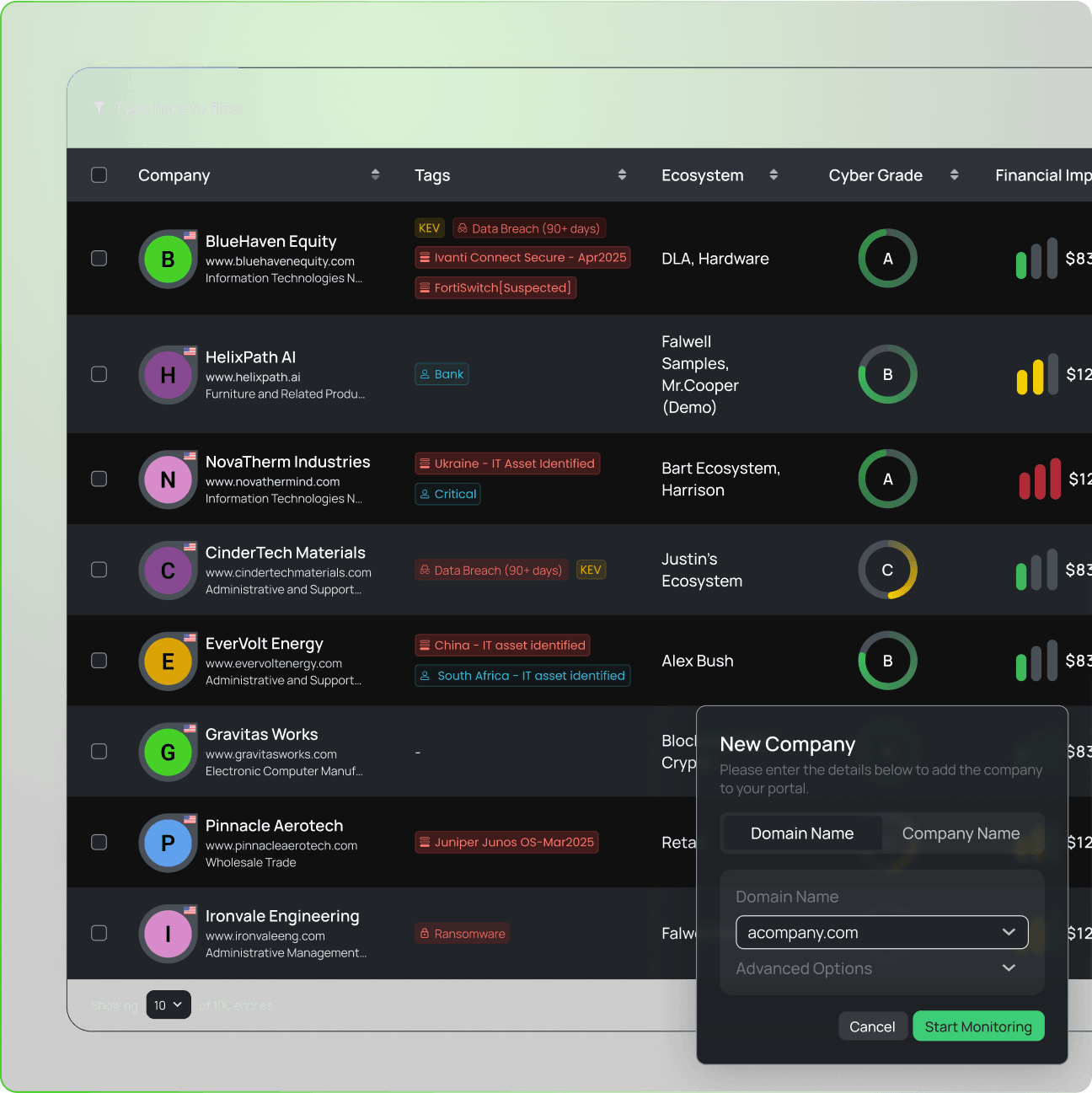
Compliance requirements span multiple evolving frameworks. NIST, GDPR, ISO 27001, SOC 2, DORA, and NIS2 each require different controls and evidence. Keeping pace with regulatory updates across hundreds of vendors demands continuous attention and deep expertise.
Manual tracking leads to compliance gaps as vendors fall out of alignment with new requirements. Organizations struggle to maintain a clear view of which controls apply to which vendors as frameworks evolve.