Focus Friday: TPRM Insights on Microsoft Exchange, SAP NetWeaver, and Gogs Critical Vulnerabilities
Introduction
Welcome to this week’s edition of Focus Friday, our series dedicated to providing third-party risk management professionals with the intelligence needed to handle high-profile security incidents. This week, we are looking at a trio of significant vulnerabilities impacting core business infrastructure: a spoofing flaw in Microsoft Exchange Server, an authorization bypass in SAP NetWeaver, and a series of critical vulnerabilities in the Gogs self-hosted Git service. Each of these incidents presents unique challenges for supply chain security, ranging from the risk of Business Email Compromise (BEC) to the potential exfiltration of proprietary source code. By utilizing Black Kite’s FocusTags®, organizations can move beyond manual, broad-spectrum vendor surveys and instead apply a data-driven approach to identify and mitigate these specific risks within their vendor ecosystem.
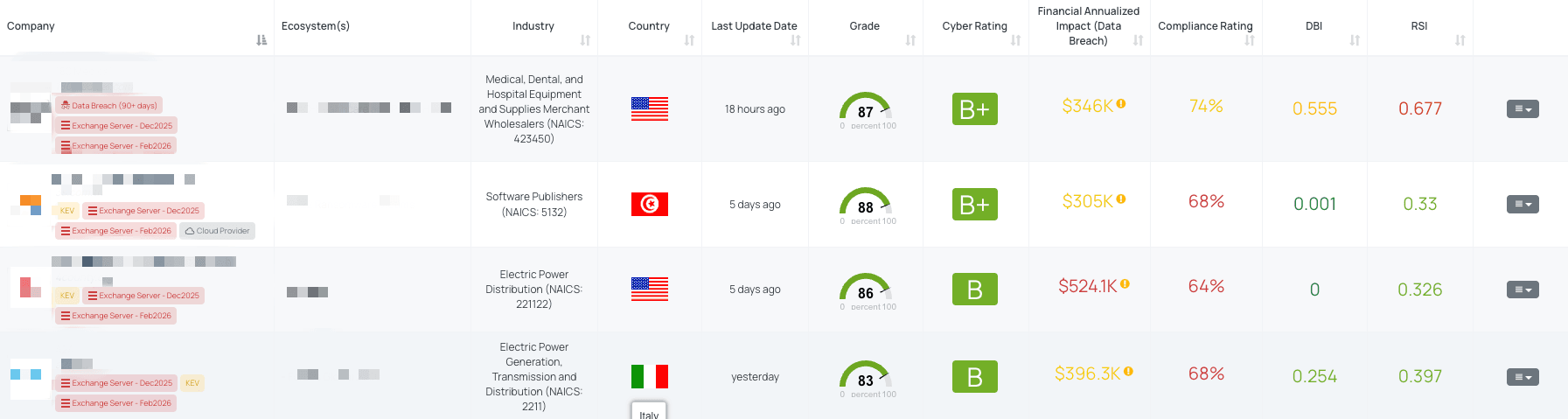
Filtered view of companies with Exchange Server - Feb2026 FocusTag® on the Black Kite platform.
Exchange Server - Feb2026 (CVE-2026-21527)
What is the Microsoft Exchange Server Spoofing Vulnerability?
CVE-2026-21527 is a spoofing vulnerability affecting Microsoft Exchange Server, characterized by the user interface (UI) misrepresenting critical system information. Published on February 10, 2026, as part of Microsoft’s February Patch Tuesday, the flaw allows a remote, unauthenticated attacker to deceive users by displaying misleading UI elements over a network. This lack of data authenticity verification can lead users or automated systems into accepting falsified information, potentially resulting in unauthorized actions or further compromise.
The vulnerability has a CVSSv3.1 base score of 6.5 (Medium) and an EPSS score of 0.03%. It impacts multiple versions, including Exchange Server Subscription Edition RTM, Exchange Server 2019 (CU14 and CU15), and Exchange Server 2016 (CU23). While Microsoft addressed six actively exploited zero-days in the same release cycle, CVE-2026-21527 is not currently known to be exploited in the wild and has not been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. No public Proof-of-Concept (PoC) exploits have been reported at this time.
Why should TPRM Professionals care about this Exchange Server vulnerability?
Microsoft Exchange Server is a cornerstone of corporate communication and identity management. For TPRM professionals, a spoofing vulnerability in a vendor’s email infrastructure is a high-priority concern because it undermines the integrity of official communications. If a vendor’s Exchange Server is susceptible to UI misrepresentation, attackers can craft deceptive prompts or internal notifications that appear legitimate to the vendor’s employees.
This can be used as a stepping stone for Business Email Compromise (BEC) or internal phishing campaigns. From a third-party perspective, if a vendor's system is tricked into performing unauthorized actions due to spoofed information, the sensitive data they handle for your organization could be at risk. Furthermore, because the attack can be executed by a remote, unauthenticated actor, the barrier to entry for a threat actor is significantly lower than vulnerabilities requiring high privileges.
What questions should TPRM professionals ask vendors about CVE-2026-21527?
To assess the risk posed by this vulnerability, TPRM professionals should move beyond general patching queries and ask the following specific questions:
- Have you applied the February 2026 security updates to all your Microsoft Exchange Server deployments, including Subscription Edition RTM, Exchange Server 2019 (CU14 and CU15), and Exchange Server 2016 (CU23), to mitigate the risk of CVE-2026-21527?
- Can you confirm that you have verified the build numbers of your Exchange servers to ensure they are running the patched versions (Exchange 2016 CU23, Exchange 2019 CU14/CU15, or Subscription Edition RTM with the latest update) that address CVE-2026-21527?
- Have you implemented monitoring measures to detect suspicious spoofing or phishing-style activity targeting Exchange users and administrators, specifically related to potential exploitation of the UI misrepresentation vulnerability (CVE-2026-21527)?
- Have you followed Microsoft’s customer action requirements and update guidance to ensure full remediation steps are completed to address the spoofing vulnerability in Microsoft Exchange Server (CVE-2026-21527)?
Remediation Recommendations for Vendors subject to this risk
Vendors should take the following technical steps to secure their Exchange environments against this spoofing risk:
- Apply Security Updates: Immediately install the February 2026 security updates provided by Microsoft for all affected versions (Subscription Edition, 2019, and 2016).
- Enable Extended Protection: Ensure that Extended Protection is active on all Exchange-based servers. This is a critical prerequisite for mitigating many modern Exchange vulnerabilities.
- Run Health Checker: Use the official Microsoft Exchange Server Health Checker tool to confirm that the environment is fully patched and that no configuration gaps exist.
- Migrate if Necessary: Organizations using versions that have reached the end of support and are not in the ESU program should prioritize migration to Exchange Server Subscription Edition (SE).
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite enables TPRM professionals to bypass the slow process of manual outreach by providing immediate visibility into vendor exposure. Black Kite published the "Exchange Server - Feb2026" FocusTag® on February 11, 2026, just one day after the vulnerability was disclosed.
By using this tag, professionals can instantly identify which vendors in their ecosystem are running vulnerable versions of Microsoft Exchange. Crucially, Black Kite provides the specific asset information—including IP addresses and subdomains—where the vulnerable product is hosted. This allows risk teams to provide vendors with actionable intelligence rather than generic warnings, significantly accelerating the remediation timeline and reducing the window of opportunity for potential attackers.
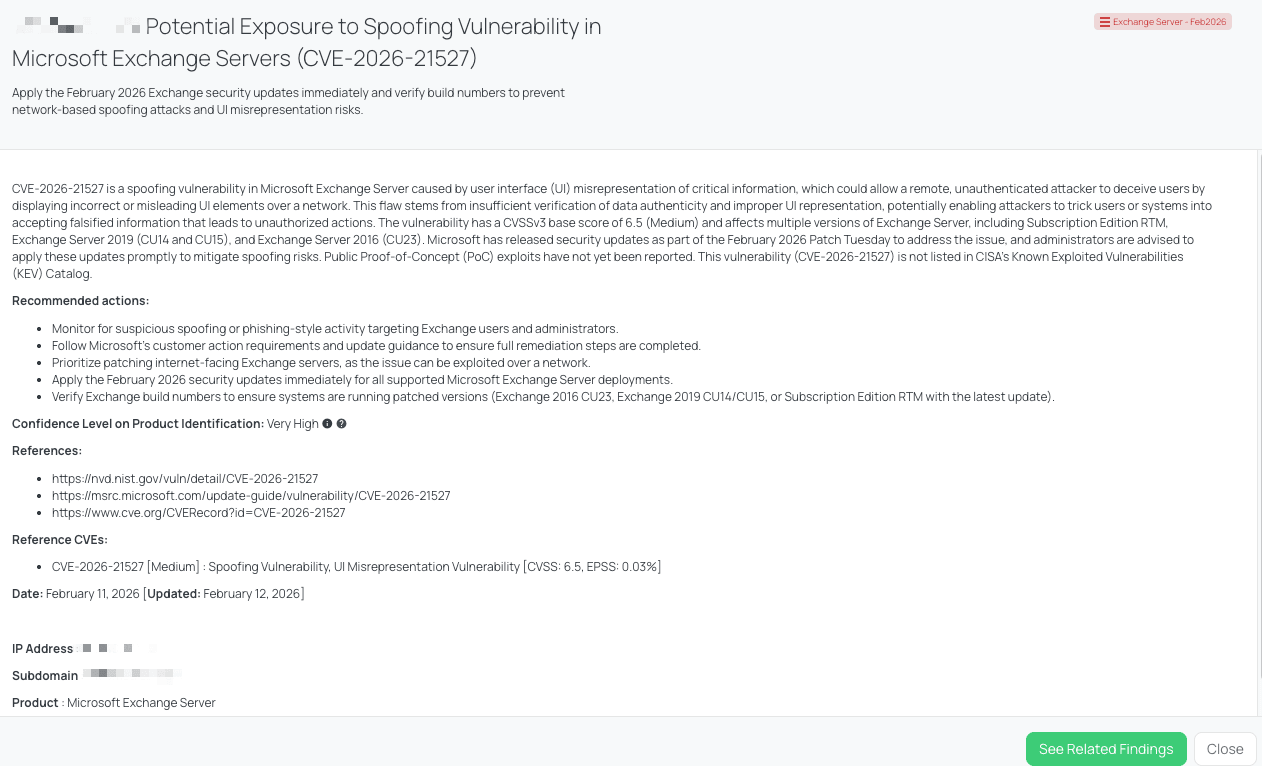
Black Kite's Exchange Server - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
SAP NetWeaver AS ABAP (CVE-2026-0509)
What is the SAP NetWeaver Missing Authorization Vulnerability?
CVE-2026-0509 is a critical vulnerability within the SAP NetWeaver Application Server (AS) ABAP and ABAP Platform. Disclosed by SAP on February 10, 2026, as part of their monthly Security Patch Day, this flaw is categorized as a Missing Authorization vulnerability. It enables an authenticated, low-privileged user to execute background Remote Function Calls (RFC) even when they do not possess the required S_RFC authorization.
The vulnerability carries a CVSS score of 9.6 (Critical) and an EPSS score of 0.04%. The severity is amplified by its "Scope: Changed" (S:C) impact, meaning an attacker can affect components beyond the initial security scope of the ABAP platform. This specific logic failure impacts a wide range of SAP Kernel versions, including 7.22, 7.53, 7.54, 7.77,7.89, 7.93, 9.16, 9.18, and 9.19. Currently, there are no reports of this vulnerability being exploited in the wild, and it has not been added to CISA's Known Exploited Vulnerabilities (KEV) catalog.
Why should TPRM Professionals care about this SAP NetWeaver vulnerability?
SAP NetWeaver is the backbone of many large organizations' business logic, housing critical functions such as finance,human resources, and supply chain management. For a TPRM professional, a critical vulnerability in this platform signifies a high-risk exposure point for any vendor providing business-critical services. Since the flaw allows low-privileged users to bypass authorization checks, an insider threat or a compromised employee account at a vendor could lead to unauthorized system-wide actions.
Because this vulnerability impacts system integrity and availability, successful exploitation could allow an attacker to disrupt the vendor's operations or manipulate critical data. If a vendor manages your organization's sensitive data through an SAP-based portal or service, a breach of their NetWeaver environment could result in unauthorized data modification or a total denial of service, impacting your own downstream business continuity and data reliability.
What questions should TPRM professionals ask vendors about CVE-2026-0509?
To verify that a vendor has adequately addressed this risk, TPRM teams should pose the following specific questions:
- Have you applied the SAP Security Note 3674774 to address the Missing Authorization vulnerability (CVE-2026-0509) in SAP NetWeaver AS ABAP and ABAP Platform?
- Can you confirm if all your SAP Kernel components have been upgraded to the specific patch levels identified in the SAP Support Portal for your specific release, especially for the versions KRNL64NUC: 7.22, 7.22EXT, KRNL64UC: 7.22, 7.22EXT, 7.53, and SAP KERNEL: 7.22, 7.53, 7.54, 7.77, 7.89, 7.93, 9.16, 9.18, 9.19?
- Have you conducted an audit of existing S_RFC authorizations to ensure the principle of least privilege is maintained, as recommended in the advisory?
- Given the "Scope: Changed" (S:C) impact of the vulnerability, have you assessed and addressed potential effects on components beyond the initial security scope?
Remediation Recommendations for Vendors subject to this risk
Vendors should take immediate action to secure their SAP landscapes by following these technical recommendations:
- Prioritize Security Note 3674774: This is the primary fix for the missing authorization check. Application of this note should be treated as a critical priority.
- Upgrade SAP Kernel: Ensure that the SAP Kernel is updated to the latest available patch level for the specific version in use, particularly for those on versions 7.22 through 9.19.
- Restrict RFC Access: Implement granular RFC security policies. Use the Unified Connectivity (UCON) framework to limit the number of RFC function modules that can be called from outside the system.
- Continuous Monitoring: Monitor system logs for unusual background RFC activity, especially calls coming from accounts that typically do not perform administrative or high-volume tasks.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite allows TPRM professionals to identify which vendors are potentially exposed to this SAP vulnerability without the need for manual, time-consuming outreach. On February 12, 2026, Black Kite published the SAP NetWeaver - Feb2026 FocusTag®, providing instant visibility into vendor environments.
By using this tag, Black Kite customers can pinpoint exactly which vendors are running vulnerable SAP Kernel versions.A key differentiator of the platform is its ability to provide specific asset information—such as the IP addresses and subdomains of the vendor's SAP infrastructure—that are at risk. This enables TPRM teams to move away from generic inquiries and instead offer vendors actionable intelligence, accelerating the remediation process and securing the third-party ecosystem more effectively.
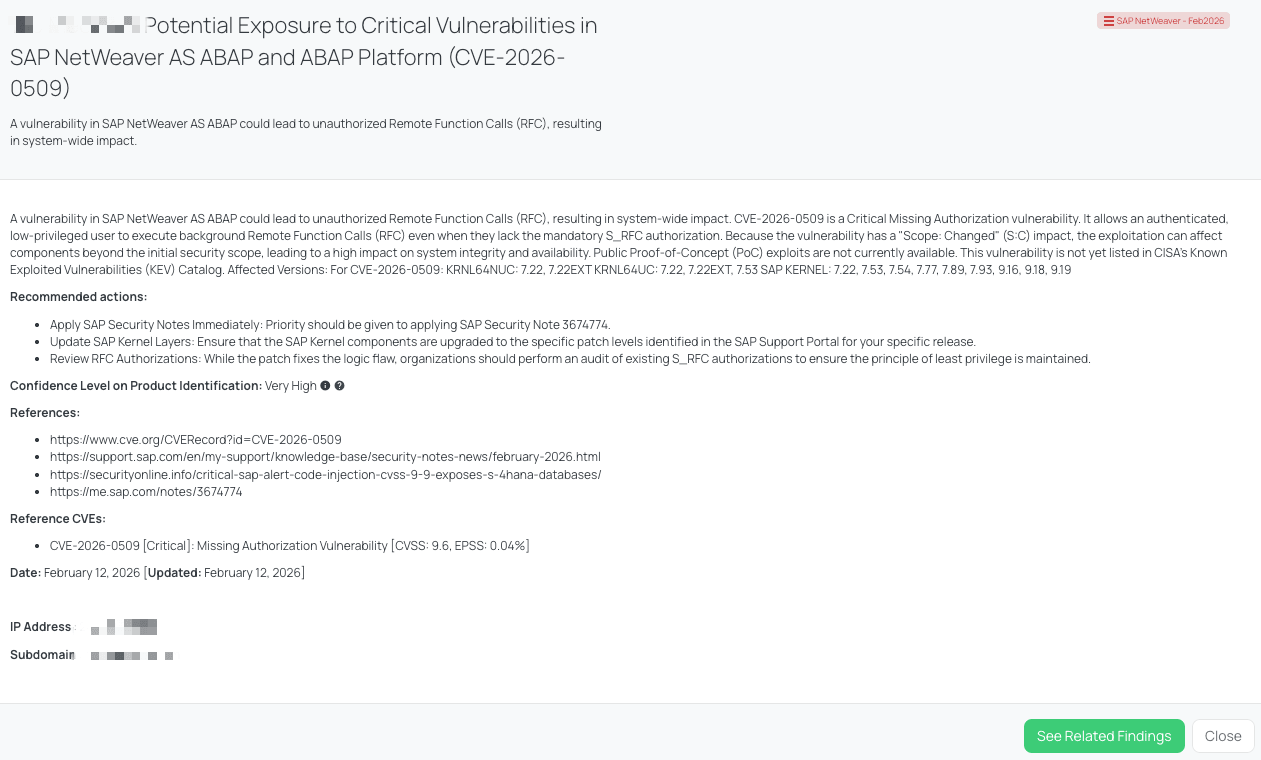
Black Kite's SAP NetWeaver - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
Gogs - Feb2026 (CVE-2025-64111, CVE-2025-64175, and CVE-2026-24135)
What is the Gogs Triple Threat Vulnerability?
Gogs, a widely used self-hosted Git service, is currently affected by three significant security flaws that, when combined, offer attackers a variety of entry points. The most severe is CVE-2025-64111, a critical Remote Code Execution (RCE) vulnerability with a CVSS score of 9.3 and an EPSS of 0.09%. This flaw arises from an insufficient patch of a previous issue, allowing an unauthenticated attacker to tamper with a repository's .git configuration files via the API, ultimately leading to full system compromise.
The second flaw, CVE-2025-64175 (CVSS 7.7, EPSS 0.01%), is an authentication bypass that renders Two-Factor Authentication (2FA) ineffective. Because Gogs improperly scopes recovery codes, an attacker with a victim's password can use a recovery code from their own separate account to log in as the victim. Finally, CVE-2026-24135 (CVSS 7.2, EPSS 0.04%) is a path traversal vulnerability in the wiki feature that allows authenticated users to delete arbitrary files on the server. While these were disclosed in early February 2026 and public Proof-of-Concept (PoC) exploits have been reported, they are not currently listed in CISA’s KEV catalog.
Why should TPRM Professionals care about these Gogs vulnerabilities?
For TPRM professionals, these vulnerabilities are particularly concerning because Git services like Gogs house an organization's most sensitive intellectual property: its source code. If a vendor utilizes an unpatched Gogs instance, an attacker could achieve RCE to steal proprietary code, inject backdoors into software before it is delivered to you (a supply chain attack), or delete critical documentation and repositories entirely.
The 2FA bypass is especially dangerous for vendors who believe they are protected by multi-factor authentication. In a third-party risk context, a compromised developer account could allow an attacker to move laterally through the vendor's development environment, potentially gaining access to the credentials or keys used to manage your organization's data. Because Gogs is often self-hosted and "set and forget," many vendors may not be aware that their internal code-management tools require immediate patching.
What questions should TPRM professionals ask vendors about these Gogs vulnerabilities?
To determine if a vendor is managing this risk effectively, TPRM analysts should ask the following targeted questions:
- Have you upgraded all instances of Gogs to version 0.13.4 or 0.14.0+dev to mitigate the risk of CVE-2025-64111, CVE-2025-64175, and CVE-2026-24135?
- Can you confirm if you have implemented measures to monitor for unusual API calls, modifications to `.git/config` files, or unauthorized file deletions, which could indicate attempted exploitation of CVE-2025-64111?
- Have you reviewed and enforced strong authentication measures, including the use of strong, unique passwords and 2FA, to mitigate the risk of CVE-2025-64175, despite the vulnerability's ability to bypass 2FA?
- Can you confirm if you have taken steps to sanitize the `old_title` parameter using `ToWikiPageName` (or `path.Clean` and basename validation) before using it in file operations to mitigate the risk of CVE-2026-24135?
Remediation Recommendations for Vendors subject to this risk
Vendors should prioritize the following technical steps to secure their Gogs installations:
- Immediate Upgrade: Transition Gogs instances to version 0.13.4, 0.14.0+dev, or later. This is the only way to resolve the underlying logic flaws in the API and authentication modules.
- Harden API Access: Restrict access to the Gogs API to known, trusted IP addresses to prevent unauthenticated actors from attempting to tamper with repository configurations.
- Audit Recovery Codes: Following the patch, reset all user 2FA recovery codes to ensure that the previous cross-account bypass cannot be leveraged using cached or stolen codes.
- Implement File Integrity Monitoring: Monitor the .git directories and system-level files for unauthorized deletions or modifications, specifically watching for changes to the old_title parameter in wiki rename operations.
How TPRM professionals can leverage Black Kite for these vulnerabilities
Black Kite provides critical visibility into whether your vendors are running outdated and vulnerable versions of Gogs. On February 11, 2026, Black Kite published the "Gogs - Feb2026" FocusTag®, enabling customers to immediately identify exposure across their entire vendor ecosystem.
Rather than waiting for a vendor to respond to a manual questionnaire, Black Kite identifies the specific assets—including subdomains and IP addresses—that are hosting Gogs services. This asset-level intelligence allows TPRM teams to point vendors directly to the vulnerable instance, facilitating a much faster remediation process. For organizations managing hundreds of vendors, this automated identification is the most efficient way to prevent a compromise in the vendor's development environment from becoming a supply chain disaster for the client.
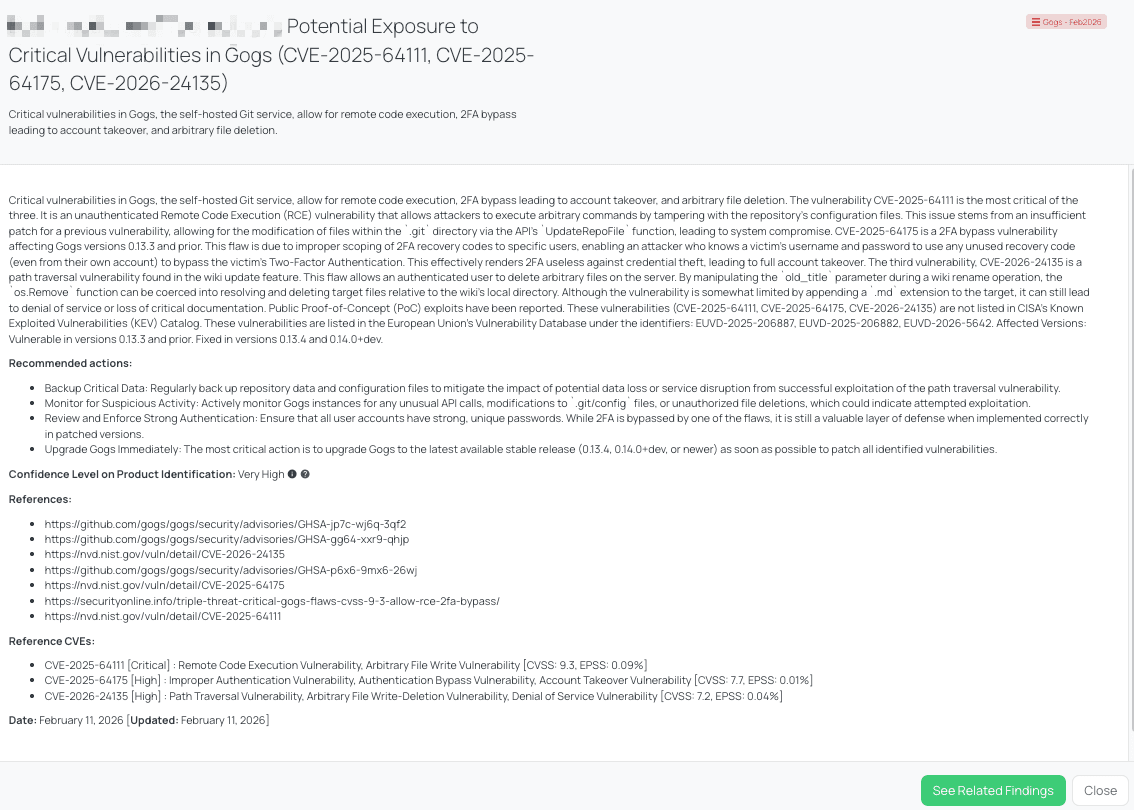
Black Kite's Gogs - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
Strengthening TPRM Outcomes with Black Kite’s FocusTags®
Black Kite’s FocusTags® play an indispensable role in refining Third-Party Risk Management (TPRM) approaches, especially in light of the high-velocity disclosures seen this week across Exchange Server - Feb2026, SAP NetWeaver - Feb2026, and Gogs - Feb2026. These tags provide:
- Precision Exposure Detection: Instantly isolate which vendors are running vulnerable versions of critical software, such as SAP Kernel or Gogs, without waiting weeks for questionnaire responses.
- Asset-Level Intelligence: Leverage specific evidence, including impacted IP addresses and subdomains, to provide vendors with actionable data that accelerates their internal remediation efforts.
- Response Orchestration: Prioritize outreach based on the technical severity of the vulnerability (such as the 9.6 CVSS score of the SAP flaw) and the business criticality of the affected vendor.
- Proactive Defense Posture: Gain a holistic view of emerging threats as they break, allowing risk leaders to brief stakeholders with confidence and data-backed insights.
Black Kite’s FocusTags® empower TPRM professionals to evolve from reactive responders into proactive risk managers. By converting vast amounts of vulnerability data into clear, actionable intelligence, we help you close the gap between threat discovery and vendor remediation.
About Focus Friday
Every week, we delve into the realms of critical vulnerabilities and their implications from a Third-Party Risk Management (TPRM) perspective. This series is dedicated to shedding light on pressing cybersecurity threats, offering in-depth analyses, and providing actionable insights.
FocusTags® in the Last 30 Days:
- Exchange Server - Feb2026 : CVE-2026-21527, Spoofing vulnerability in Microsoft Exchange Server involving UI misrepresentation.
- SAP NetWeaver - Feb2026 : CVE-2026-0509, Critical Missing Authorization vulnerability in SAP NetWeaver AS ABAP allowing unauthorized RFC execution.
- Gogs - Feb2026 : CVE-2025-64111, CVE-2025-64175, CVE-2026-24135, Triple threat involving Critical RCE, 2FA Bypass, and Path Traversal in Gogs Git services.
- OpenClaw : CVE-2026-25253, Critical 1-Click Remote Code Execution and Token Exfiltration Vulnerability in OpenClaw (Moltbot).
- Ivanti EPMM - Jan2026 : CVE-2026-1281, CVE-2026-1340, Critical Unauthenticated Remote Code Execution and Code Injection Vulnerabilities in Ivanti Endpoint Manager Mobile.
- Cisco TelePresence : CVE-2026-20119, High-Severity Denial of Service Vulnerability in Cisco TelePresence Collaboration Endpoint (CE) Software.
- Django - Feb2026 : CVE-2026-1207, CVE-2026-1287, CVE-2026-1312, CVE-2025-14550, CVE-2026-1285, CVE-2025-13473, Multiple SQL Injection, Denial of Service (DoS), and Username Enumeration Vulnerabilities in Django Web Framework.
- n8n - Feb2026 : CVE-2026-25049, CVE-2026-25056, CVE-2026-25053, Triple Threat of Critical Remote Code Execution Vulnerabilities in n8n Workflow Automation Platform.
- Fortinet - Jan2026 : CVE-2026-24858, Authentication Bypass Using an Alternate Path or Channel Vulnerability, Zero-Day Exploitation in Fortinet Products.
- GNU InetUtils telnetd : CVE-2026-24061, Authentication Bypass Vulnerability in GNU InetUtils.
- SolarWinds WHD - Jan2026 : CVE-2025-40551, CVE-2025-40552, CVE-2025-40553, CVE-2025-40554, CVE-2025-40536, CVE-2025-40537, Untrusted Data Deserialization, Authentication Bypass, and Hardcoded Credentials Vulnerabilities in SolarWinds Web Help Desk.
- OpenSSL : CVE-2025-15467, CVE-2025-11187, Remote Code Execution and Buffer Overflow Vulnerabilities in OpenSSL.
- SmarterMail - Jan2026 : CVE-2026-23760, Administrative Password Reset and Authentication Bypass Vulnerability in SmarterTools SmarterMail.
- n8n - Jan2026 (Latest) : CVE-2026-1470, CVE-2026-0863, Remote Code Execution, Arbitrary Code Injection, and Sandbox Escape Vulnerabilities in n8n.
- React Server Components : CVE-2026-23864, Denial of Service Vulnerabilities in React Server Components.
- TP-Link Archer MR600 : CVE-2025-14756, Authenticated Command Injection Vulnerability in TP-Link Archer MR600 Routers.
- Sitecore : CVE-2025-53690, Code Injection Vulnerability stemming from ASP.NET Machine Key Misconfiguration, Leading to ViewState Deserialization and Actively Exploited Remote Code Execution in Sitecore Products.
- MSSQL - Jan2026 : CVE-2026-20803, Elevation of Privilege and Missing Authentication for Critical Function Vulnerability Leading to Unauthorized Debugging and System Memory Dumping in Microsoft SQL Server.
- SharePoint - Jan2026 : CVE-2026-20959, CVE-2026-20958, CVE-2026-20951, CVE-2026-20963, CVE-2026-20947, Multiple Vulnerabilities including Deserialization of Untrusted Data, SQL Injection, and SSRF Leading to Remote Code Execution and Spoofing in Microsoft Office SharePoint.
- Cisco UCM : CVE-2026-20045, Improper Input Validation and Remote Code Execution Vulnerability Leading to Unauthenticated Root Access and Active Exploitation in Cisco Unified Communications Products and Webex Calling.
- SAP NetWeaver - Jan2026 : CVE-2026-0507, OS Command Injection and Remote Code Execution Vulnerability Leading to Full System Compromise in SAP Application Server for ABAP and SAP NetWeaver RFCSDK.
- Apache Solr : CVE-2026-22444, CVE-2026-22022, Multiple Vulnerabilities including Authorization Bypass and Improper Input Validation Leading to Sensitive Data Exposure and NTLM Hash Disclosure in Apache Solr.
- Appsmith : CVE-2026-22794 & CVE-2026-24042, Account Takeover and Critical Authorization Bypass (viewMode Confusion) Vulnerabilities Leading to Full Account Compromise in Appsmith.
- Ni8mare : CVE-2026-21858, Improper Input Validation, Arbitrary File Read, Authentication Bypass, and Unauthenticated Remote Code Execution Vulnerabilities Leading to Full Administrative Takeover in n8n Workflow Automation Platform.
See Black Kite’s full CVE Database and the critical TPRM vulnerabilities that have an applied FocusTags® at https://blackkite.com/cve-database.
References
https://www.cve.org/CVERecord?id=CVE-2026-21527
https://nvd.nist.gov/vuln/detail/CVE-2026-21527
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-21527
https://me.sap.com/notes/3674774
https://me.sap.com/notes/3697567
https://nvd.nist.gov/vuln/detail/CVE-2026-0509
https://nvd.nist.gov/vuln/detail/CVE-2026-23687
https://securityonline.info/triple-threat-critical-gogs-flaws-cvss-9-3-allow-rce-2fa-bypass/
https://github.com/gogs/gogs/security/advisories/GHSA-jp7c-wj6q-3qf2
https://github.com/gogs/gogs/security/advisories/GHSA-p6x6-9mx6-26wj
https://github.com/gogs/gogs/security/advisories/GHSA-gg64-xxr9-qhjp
https://nvd.nist.gov/vuln/detail/CVE-2026-24135