Focus Friday: TPRM Insights on Critical Vulnerabilities in BeyondTrust, Zimbra, and PostgreSQL
Introduction
Welcome to this week's edition of Focus Friday, where we analyze the latest high-profile cybersecurity incidents through the lens of Third-Party Risk Management (TPRM). In a hyper-connected digital ecosystem, a vulnerability in a single software component often cascades into a broader supply chain risk. This week, we examine three distinct but equally critical threats: an actively exploited Remote Code Execution (RCE) flaw in BeyondTrust’s privileged access tools, a resurfaced Server-Side Request Forgery (SSRF) vulnerability in Zimbra Collaboration Suite, and a cluster of high-severity code execution issues in PostgreSQL databases.
These technologies—spanning privileged access management, enterprise communication, and data storage—form the backbone of many vendor operations. When compromised, they do not merely cause service disruptions; they provide attackers with deep footholds into internal networks and sensitive data repositories. In this post, we break down the technical details of these threats, their implications for your vendor ecosystem, and how you can leverage Black Kite’s intelligence to drive precise, effective remediation.
By utilizing Black Kite’s FocusTags®, organizations can move beyond manual, broad-spectrum vendor surveys and instead apply a data-driven approach to identify and mitigate these specific risks within their vendor ecosystem.
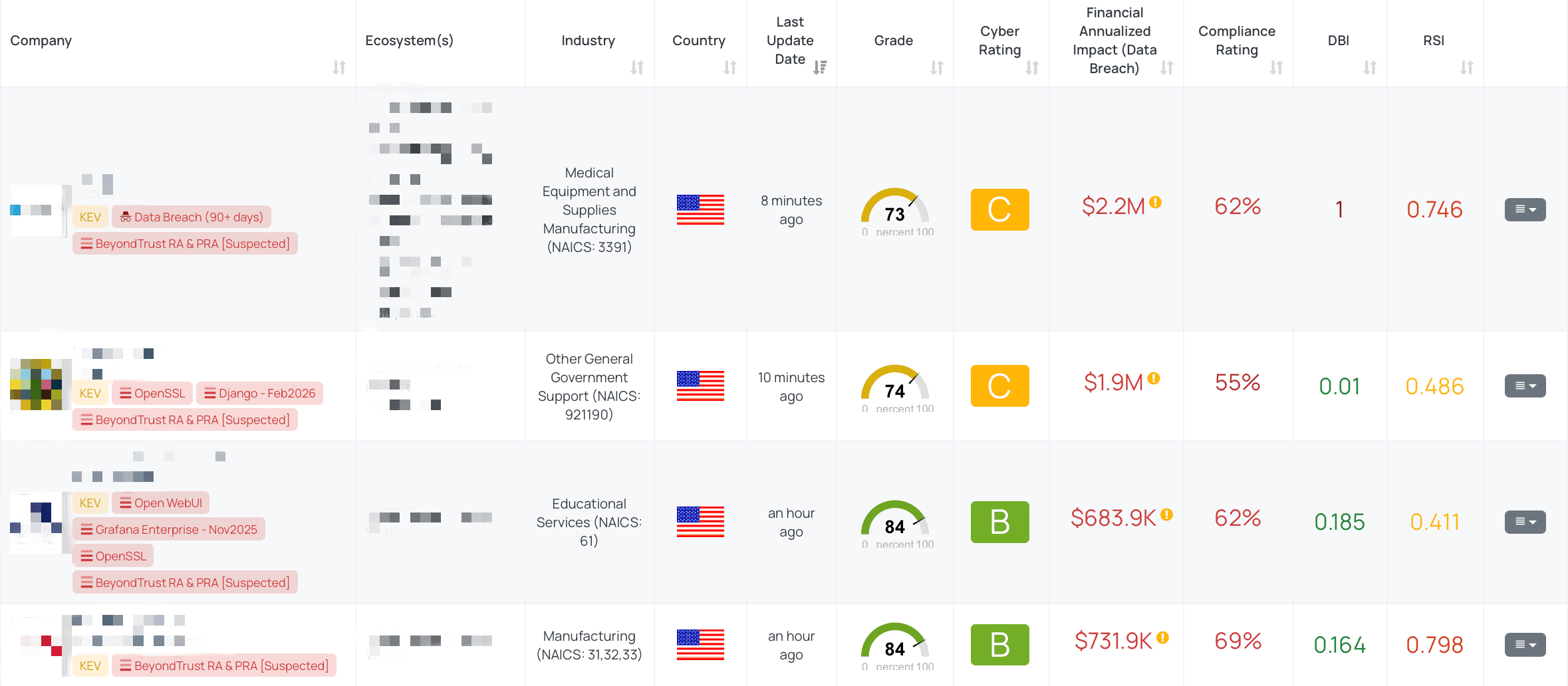
Filtered view of companies with BeyondTrust RA & PRA FocusTag® on the Black Kite platform.
BeyondTrust RA & PRA (CVE-2026-1731)
What is the BeyondTrust RCE Vulnerability?
CVE-2026-1731 is a critical unauthenticated Remote Code Execution (RCE) vulnerability affecting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA). The flaw stems from an OS command injection weakness involving unsafe Bash arithmetic evaluation. It allows remote attackers to inject and execute arbitrary operating system commands by sending specially crafted requests to the appliance, specifically targeting the /nw WebSocket endpoint.
This vulnerability is rated CRITICAL with a CVSS score of 9.9. The EPSS score is 61.38%, indicating a very high probability of exploitation in the near term.
The vulnerability was privately reported on January 31, 2026, and publicly disclosed by BeyondTrust on February 6, 2026. Active exploitation in the wild was observed shortly thereafter, starting around February 10, 2026. Security researchers at WatchTowr and GreyNoise have confirmed active campaigns where attackers perform reconnaissance by abusing the get_portal_info API to extract the x-ns-company value before establishing a WebSocket channel to trigger the exploit. In some observed cases, attackers have deployed the SimpleHelp Remote Monitoring and Management (RMM) tool (renamed as remote access.exe) to maintain persistence and have successfully escalated privileges to Domain Admin.
Recognizing the severity and active abuse, CISA added CVE-2026-1731 to its Known Exploited Vulnerabilities (KEV) Catalog on February 13, 2026, mandating federal agencies to patch by February 16, 2026.
Why TPRM Professionals Should Care About CVE-2026-1731
BeyondTrust RS and PRA are designed to manage and secure privileged access, meaning they often hold the "keys to the kingdom" for an organization’s most sensitive environments. If a vendor’s instance is compromised, attackers can bypass authentication entirely, gain entry as the site user, and potentially pivot to internal networks with high-level privileges.
From a TPRM perspective, this poses a severe supply chain risk. If your vendors use these tools to support your environment or manage their own infrastructure, a compromise could lead to data exfiltration, unauthorized access to your systems, or a full ransomware event within the vendor’s network. The fact that attackers are already using this flaw to deploy persistence tools and escalate to Domain Admin status makes unpatched vendors a critical liability.
What questions should TPRM professionals ask vendors about CVE-2026-1731?
To assess the risk posed by this vulnerability, TPRM professionals should ask the following targeted questions:
- Have you identified and inventoried all instances of BeyondTrust Remote Support and Privileged Remote Access within your network, and can you confirm if any of these are running on the vulnerable versions v21.3 through v25.3.1 for Remote Support and v22.1 through v24.X for Privileged Remote Access?
- Have you applied the official security updates BT26-02-RS for Remote Support and BT26-02-PRA for Privileged Remote Access provided by BeyondTrust to mitigate the risk of CVE-2026-1731?
- Are you monitoring for exploitation attempts specifically targeting the extraction of the `x-ns-company` value or the establishment of WebSocket channels from suspicious sources, as these are known exploitation patterns for CVE-2026-1731?
- Given the active exploitation of the `get_portal_info` to extract the `x-ns-company` value, have you implemented any additional security measures to prevent unauthorized access, data exfiltration, and service disruption?
Remediation Recommendations for Vendors subject to this risk
Vendors identified as potentially vulnerable should take the following immediate actions:
- Patch Immediately: Apply the official BT26-02 security update provided by BeyondTrust. This fixes the OS command injection flaw.
- Verify Integrity: Run a thorough forensic check on the appliance for unauthorized files. Look specifically for files in the ProgramData directory that may be renamed versions of the SimpleHelp remote access client.
- Network Hardening: Restrict the attack surface by ensuring the administrative and support portals are not directly exposed to the open internet. Use a VPN or strict IP allowlisting to limit access to trusted sources only.
- Enhance Monitoring: Configure alerts for any processes spawning from the BeyondTrust service account (bomgar) that invoke shell commands or attempt to establish outbound connections to unknown IPs.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite enables TPRM teams to quickly identify which vendors are exposing vulnerable BeyondTrust assets. The BeyondTrust RA & PRA [Suspected] FocusTags®, published on February 16, 2026, flags vendors that appear to be running the affected versions of Remote Support and Privileged Remote Access.
By operationalizing this tag, TPRM professionals can bypass the time-consuming process of surveying every vendor. Instead, they can focus their outreach on the specific subset of vendors where Black Kite has detected the relevant product signature. A key differentiator of Black Kite’s approach is the provision of asset-level data—such as the specific IP addresses or subdomains hosting the vulnerable appliance—allowing risk teams to present vendors with concrete evidence of their exposure and drive faster remediation.
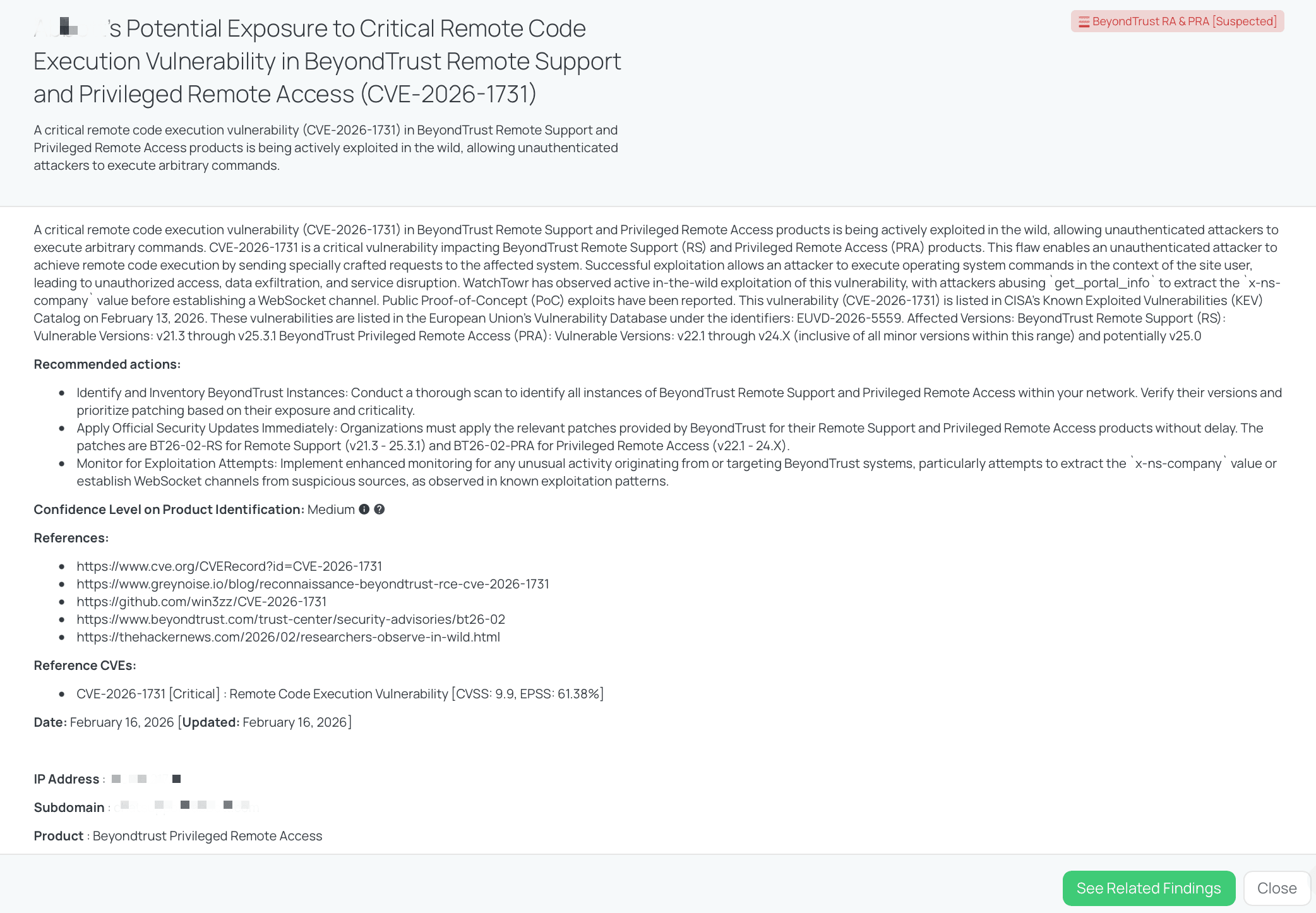
Black Kite's BeyondTrust RA & PRA FocusTag® details critical insights on the event for TPRM professionals.
Zimbra - Feb2026 (CVE-2020-7796)
What is the Zimbra WebEx Zimlet SSRF Vulnerability?
CVE-2020-7796 is a critical Server-Side Request Forgery (SSRF) vulnerability in the Zimbra Collaboration Suite (ZCS). The flaw exists within the WebEx Zimlet (com_zimbra_webex) when the zimlet’s JSP functionality is enabled. It allows an unauthenticated remote attacker to manipulate the server into sending HTTP requests to arbitrary domains chosen by the attacker. This can be used to bypass firewalls, access internal services that should be restricted, or leak sensitive information.
This vulnerability is rated CRITICAL with a CVSS score of 9.8. The EPSS score is 90.6%, indicating an extremely high probability of exploitation.
Although the vulnerability was originally identified in 2020, it has recently resurfaced with significant activity. CISA added CVE-2020-7796 to its Known Exploited Vulnerabilities (KEV) Catalog on February 17, 2026, following reports of active exploitation in the wild. Attackers are leveraging this flaw to map internal networks and potentially chain it with other exploits to gain deeper access.
Why TPRM Professionals Should Care About CVE-2020-7796
Zimbra Collaboration Suite is a widely used email and collaboration platform, often serving as the central hub for an organization's internal and external communications. A compromise here is not just an email issue; it is a gateway into the vendor's internal infrastructure.
From a TPRM perspective, an unpatched Zimbra instance represents a direct path for attackers to pivot into a vendor’s private network. Because SSRF allows the server to make requests as if they originated from inside the trusted network, attackers can use a compromised Zimbra server to scan for other vulnerable internal assets, access cloud metadata services (like AWS Instance Metadata), or exfiltrate sensitive data. If your vendor uses this platform to handle your sensitive data or communications, the integrity and confidentiality of that information are at immediate risk.
What questions should TPRM professionals ask vendors about CVE-2020-7796?
To accurately assess the risk, TPRM professionals should ask the following specific questions:
- Have you upgraded to Zimbra Collaboration 8.8.15 Patch 7 to mitigate the risk of the Server-Side Request Forgery (SSRF) vulnerability (CVE-2020-7796)?
- If the WebEx zimlet is installed in your system, have you ensured that the zimlet JSP functionality is not enabled unless absolutely necessary and that it is securely configured?
- Have you been monitoring for any unusual network traffic patterns or attempts to access internal resources from the Zimbra server, especially if the WebEx zimlet is in use?
- If you were upgrading from an older version of Zimbra to Zimbra 8.8 Production Ready, did you review "Things to Know Before Upgrading" and "First Steps with the Zimbra NG Modules “for critical information before proceeding with the upgrade?
Remediation Recommendations for Vendors subject to this risk
Vendors running affected versions should implement the following steps immediately:
- Apply the Official Patch: Upgrade Zimbra Collaboration 8.8.15 to Patch 7 (8.8.15p7) or a later version immediately. This is the primary fix provided by the vendor.
- Disable Unused Components: If the WebEx Zimlet is not actively used, uninstall it entirely. If it is required, ensure the vulnerable JSP functionality is disabled unless absolutely necessary for business operations.
- Network Segmentation: Configure firewall rules to restrict the Zimbra server’s ability to initiate outbound connections to internal network segments or sensitive cloud metadata endpoints.
- Audit Access: Review mailbox.log and access.log for any historical evidence of unauthorized requests to internal resources.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite allows TPRM teams to instantly identify vendors with potential exposure to this resurfaced threat. The Zimbra - Feb2026 FocusTags® published on February 18, 2026, flags vendors that appear to be hosting vulnerable Zimbra Collaboration instances.
By using this tag, TPRM professionals can operationalize the intelligence immediately—filtering their vendor ecosystem to find those specifically at risk of CVE-2020-7796. A critical advantage of Black Kite is the ability to provide asset-level details, such as the specific IP addresses or subdomains running the vulnerable Zimbra versions. This enables risk managers to provide vendors with actionable evidence, cutting through generic assurances and driving faster, verified remediation.
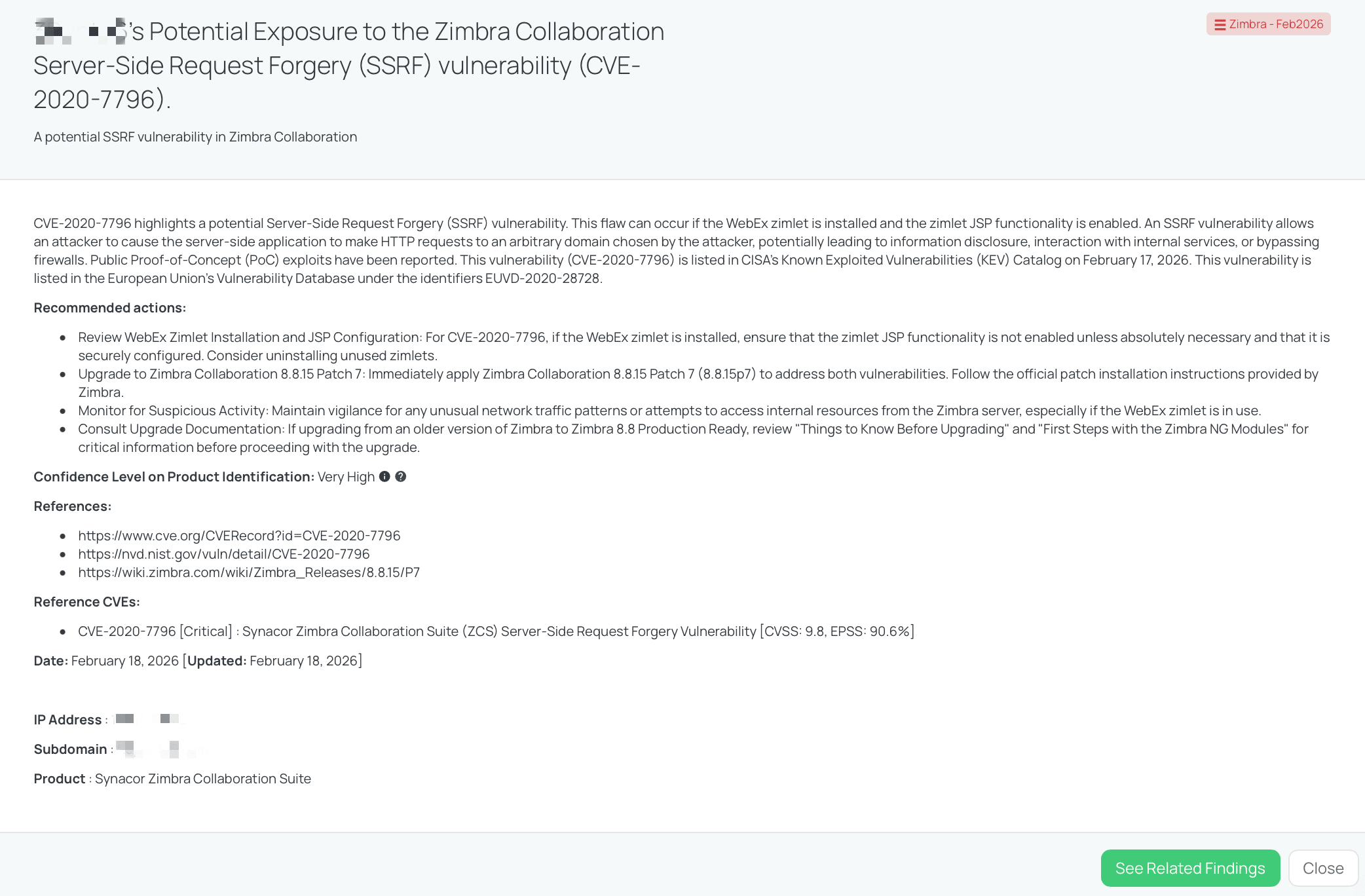
Black Kite's Zimbra - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
PostgreSQL - Feb2026 (CVE-2026-2003, CVE-2026-2004, CVE-2026-2005, CVE-2026-2006, CVE-2026-2007)
What are the PostgreSQL Vulnerabilities?
This FocusTags® covers a cluster of five vulnerabilities affecting PostgreSQL, ranging from Medium to High severity. The most critical among them (CVE-2026-2004, CVE-2026-2005, CVE-2026-2006) are rated High with a CVSS score of 8.8. These vulnerabilities enable Arbitrary Code Execution (ACE) and Privilege Escalation through various vectors:
- CVE-2026-2004: A missing input validation in the intarray extension allowing object creators to execute arbitrary code.
- CVE-2026-2005: A heap-based buffer overflow in the pgcrypto extension.
- CVE-2026-2006: A buffer overflow triggered by crafted queries involving multibyte characters.
- CVE-2026-2007: A heap-based buffer overflow in the pg_trgm extension (CVSS 8.2).
- CVE-2026-2003: A Medium severity (CVSS 4.3) improper input validation flaw allowing limited memory disclosure.
The EPSS scores remain low, ranging from 0.04% to 0.1%, indicating that widespread automated exploitation is not currently predicted. These vulnerabilities were highlighted in the FocusTags® on February 18, 2026. Currently, there are no public Proof-of-Concept (PoC) exploits available, and no active exploitation in the wild has been reported. Consequently, none of these CVEs were listed in CISA's Known Exploited Vulnerabilities (KEV) Catalog as of February 18, 2026, nor has CISA published a specific advisory regarding this cluster.
Why TPRM Professionals Should Care About These PostgreSQL Vulnerabilities
PostgreSQL is a cornerstone of modern infrastructure, frequently housing an organization's most critical data—customer records, transaction logs, and intellectual property. From a TPRM perspective, these vulnerabilities are particularly concerning because they allow Arbitrary Code Execution (ACE). If a vendor's database is compromised, an attacker can bypass database-level controls to run commands as the operating system user.
This level of access often serves as a launchpad for ransomware attacks or data exfiltration. The specific vectors—popular extensions like pgcrypto (used for encryption) and intarray—are widely deployed, increasing the likelihood that a vendor is exposed. If your data resides in a vendor's unpatched PostgreSQL instance, the confidentiality and integrity of that data are directly threatened.
What questions should TPRM professionals ask vendors about these vulnerabilities?
TPRM professionals should prioritize the following technical inquiries to gauge vendor exposure:
- Have you upgraded all instances of PostgreSQL to the fixed releases (18.2, 17.8, 16.12, 15.16, or 14.21) to mitigate the risk of CVE-2026-2003, CVE-2026-2004, CVE-2026-2005, CVE-2026-2006, and CVE-2026-2007?
- Have you conducted a comprehensive inventory of your databases to identify the usage of intarray, pgcrypto, and pg_trgm extensions, which are specific vectors for the high-severity RCE vulnerabilities?
- Can you confirm if you have reviewed and restricted permissions for users capable of creating database objects to ensure the principle of least privilege is maintained until patches are applied, as recommended for CVE-2026-2004?
- For CVE-2026-2007, can you confirm if you have taken any specific measures to address the heap buffer overflow in the pg_trgm extension, considering it allows a database user to achieve unknown impacts via crafted input strings?
Remediation Recommendations for Vendors subject to this risk
Vendors identified as vulnerable should take the following immediate steps:
- Upgrade Immediately: The most effective remediation is to upgrade to the latest supported versions: 18.2, 17.8, 16.12, 15.16, or 14.21. This addresses all five CVEs.
- Inventory and Disable Extensions: Audit all database instances for the presence of intarray, pgcrypto, and pg_trgm. If these extensions are not critical to business operations, disable them to remove the primary attack surface.
- Restrict Object Creation: Apply the principle of least privilege by revoking object creation rights from non-administrative users until the patch is fully deployed.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite enables TPRM teams to cut through the noise and identify specific vendors exposing vulnerable PostgreSQL instances. The PostgreSQL - Feb2026 FocusTags®, published on February 18, 2026, automatically detects vendors running affected versions of the database software.
TPRM professionals can operationalize this tag to filter their vendor portfolio, isolating those that pose a genuine risk to their data supply chain. A key advantage of Black Kite is the provision of asset-level intelligence, such as the specific IP addresses or subdomains hosting the vulnerable database services. This granular data allows risk managers to present vendors with irrefutable evidence of exposure, facilitating a more focused and effective remediation dialogue.
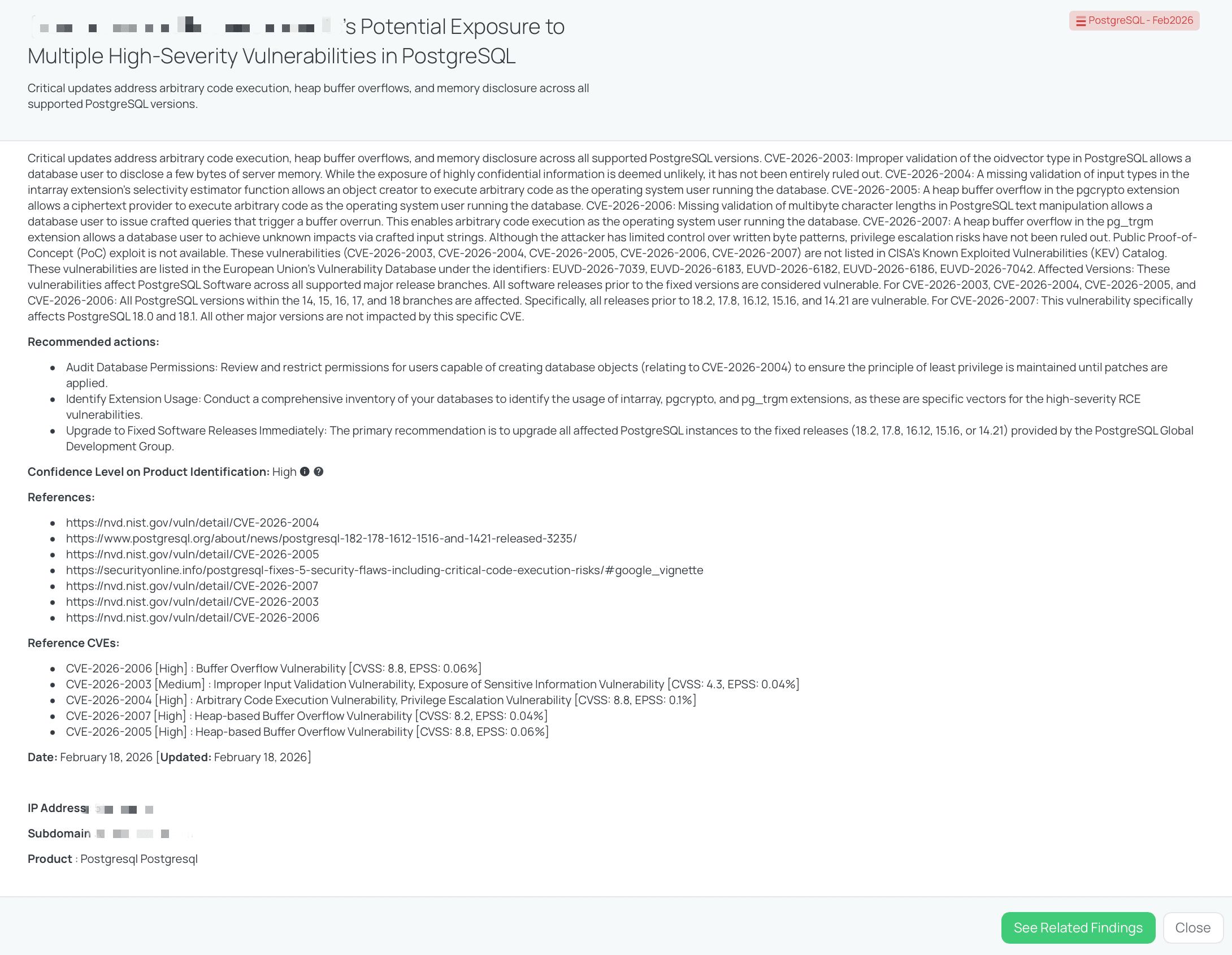
Black Kite's PostgreSQL - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
Strengthening TPRM Outcomes with Black Kite’s FocusTags®
Managing third-party risk requires more than just tracking headlines; it demands the ability to instantly correlate global threat data with your specific vendor ecosystem. This week’s vulnerabilities—ranging from BeyondTrust’s privileged access RCE to Zimbra’s communication risks and PostgreSQL’s database flaws—highlight the diversity of attack vectors that TPRM teams must monitor.
Black Kite’s FocusTags® bridge the gap between raw vulnerability disclosure and strategic vendor management. Instead of relying on broad-spectrum questionnaires that burden vendors and delay insights, FocusTags® empower organizations to:
- Drive Precision with Asset-Level Data: Move beyond generic inquiries by utilizing Black Kite’s ability to pinpoint specific IP addresses and subdomains hosting vulnerable versions of BeyondTrust, Zimbra, or PostgreSQL. This allows for evidence-based conversations rather than hypothetical risk assessments.
- Accelerate Triage and Response: Instantly filter your vendor portfolio to identify those most at risk. By isolating vendors with "High" or "Critical" exposure to these specific CVEs, teams can allocate resources to the relationships that pose the greatest threat to business continuity and data confidentiality.
- Combat Questionnaire Fatigue: Replace repetitive, manual surveys with targeted, intelligence-led engagement. When you know exactly which vendors are running vulnerable software, you can ask specific, technical questions that drive faster remediation.
- Stay Ahead of Active Exploitation: With FocusTags® updating in near real-time—such as the rapid tagging of the actively exploited BeyondTrust flaw—organizations can proactively secure their supply chain before an advisory becomes a breach notification.
By integrating FocusTags® into your TPRM workflows, you transform reactive vulnerability news into a proactive defense mechanism, ensuring your organization remains resilient against the evolving threat landscape.
About Focus Friday
Every week, we delve into the realms of critical vulnerabilities and their implications from a Third-Party Risk Management (TPRM) perspective. This series is dedicated to shedding light on pressing cybersecurity threats, offering in-depth analyses, and providing actionable insights.
FocusTags® in the Last 30 Days:
- BeyondTrust RA & PRA : CVE-2026-1731, Remote Code Execution (RCE) vulnerability in BeyondTrust RA & PRA.
- Zimbra - Feb2026 : CVE-2020-7796, Critical Server-Side Request Forgery (SSRF) vulnerability in the Zimbra’s WebEx Zimlet.
- PostgreSQL - Feb2026 : CVE-2026-2004, CVE-2026-2005, CVE-2026-2006, Arbitrary Code Execution and Buffer Overflows Vulnerabilities in PostgreSQL.
- Exchange Server - Feb2026 : CVE-2026-21527, Spoofing vulnerability in Microsoft Exchange Server involving UI misrepresentation.
- SAP NetWeaver - Feb2026 : CVE-2026-0509, Critical Missing Authorization vulnerability in SAP NetWeaver AS ABAP allowing unauthorized RFC execution.
- Gogs - Feb2026 : CVE-2025-64111, CVE-2025-64175, CVE-2026-24135, Triple threat involving Critical RCE, 2FA Bypass, and Path Traversal in Gogs Git services.
- OpenClaw : CVE-2026-25253, Critical 1-Click Remote Code Execution and Token Exfiltration Vulnerability in OpenClaw (Moltbot).
- Ivanti EPMM - Jan2026 : CVE-2026-1281, CVE-2026-1340, Critical Unauthenticated Remote Code Execution and Code Injection Vulnerabilities in Ivanti Endpoint Manager Mobile.
- Cisco TelePresence : CVE-2026-20119, High-Severity Denial of Service Vulnerability in Cisco TelePresence Collaboration Endpoint (CE) Software.
- Django - Feb2026 : CVE-2026-1207, CVE-2026-1287, CVE-2026-1312, CVE-2025-14550, CVE-2026-1285, CVE-2025-13473, Multiple SQL Injection, Denial of Service (DoS), and Username Enumeration Vulnerabilities in Django Web Framework.
- n8n - Feb2026 : CVE-2026-25049, CVE-2026-25056, CVE-2026-25053, Triple Threat of Critical Remote Code Execution Vulnerabilities in n8n Workflow Automation Platform.
- Fortinet - Jan2026 : CVE-2026-24858, Authentication Bypass Using an Alternate Path or Channel Vulnerability, Zero-Day Exploitation in Fortinet Products.
- GNU InetUtils telnetd : CVE-2026-24061, Authentication Bypass Vulnerability in GNU InetUtils.
- SolarWinds WHD - Jan2026 : CVE-2025-40551, CVE-2025-40552, CVE-2025-40553, CVE-2025-40554, CVE-2025-40536, CVE-2025-40537, Untrusted Data Deserialization, Authentication Bypass, and Hardcoded Credentials Vulnerabilities in SolarWinds Web Help Desk.
- OpenSSL : CVE-2025-15467, CVE-2025-11187, Remote Code Execution and Buffer Overflow Vulnerabilities in OpenSSL.
- SmarterMail - Jan2026 : CVE-2026-23760, Administrative Password Reset and Authentication Bypass Vulnerability in SmarterTools SmarterMail.
- n8n - Jan2026 (Latest) : CVE-2026-1470, CVE-2026-0863, Remote Code Execution, Arbitrary Code Injection, and Sandbox Escape Vulnerabilities in n8n.
- React Server Components : CVE-2026-23864, Denial of Service Vulnerabilities in React Server Components.
- TP-Link Archer MR600 : CVE-2025-14756, Authenticated Command Injection Vulnerability in TP-Link Archer MR600 Routers.
- Sitecore : CVE-2025-53690, Code Injection Vulnerability stemming from ASP.NET Machine Key Misconfiguration, Leading to ViewState Deserialization and Actively Exploited Remote Code Execution in Sitecore Products.
- MSSQL - Jan2026 : CVE-2026-20803, Elevation of Privilege and Missing Authentication for Critical Function Vulnerability Leading to Unauthorized Debugging and System Memory Dumping in Microsoft SQL Server.
- SharePoint - Jan2026 : CVE-2026-20959, CVE-2026-20958, CVE-2026-20951, CVE-2026-20963, CVE-2026-20947, Multiple Vulnerabilities including Deserialization of Untrusted Data, SQL Injection, and SSRF Leading to Remote Code Execution and Spoofing in Microsoft Office SharePoint.
- Cisco UCM : CVE-2026-20045, Improper Input Validation and Remote Code Execution Vulnerability Leading to Unauthenticated Root Access and Active Exploitation in Cisco Unified Communications Products and Webex Calling.
- SAP NetWeaver - Jan2026 : CVE-2026-0507, OS Command Injection and Remote Code Execution Vulnerability Leading to Full System Compromise in SAP Application Server for ABAP and SAP NetWeaver RFCSDK.
- Apache Solr : CVE-2026-22444, CVE-2026-22022, Multiple Vulnerabilities including Authorization Bypass and Improper Input Validation Leading to Sensitive Data Exposure and NTLM Hash Disclosure in Apache Solr.
References
https://nvd.nist.gov/vuln/detail/CVE-2026-1731
https://thehackernews.com/2026/02/researchers-observe-in-wild.html
https://www.greynoise.io/blog/reconnaissance-beyondtrust-rce-cve-2026-1731
https://www.cve.org/CVERecord?id=CVE-2026-1731
https://github.com/win3zz/CVE-2026-1731
https://www.beyondtrust.com/trust-center/security-advisories/bt26-02
https://nvd.nist.gov/vuln/detail/CVE-2020-7796
https://wiki.zimbra.com/wiki/Zimbra_Releases/8.8.15/P7
https://www.cve.org/CVERecord?id=CVE-2020-7796
https://nvd.nist.gov/vuln/detail/CVE-2026-2003
https://nvd.nist.gov/vuln/detail/CVE-2026-2004
https://nvd.nist.gov/vuln/detail/CVE-2026-2005
https://nvd.nist.gov/vuln/detail/CVE-2026-2006
https://nvd.nist.gov/vuln/detail/CVE-2026-2007
https://securityonline.info/postgresql-fixes-5-security-flaws-including-critical-code-execution-risks/#google_vignette
https://www.postgresql.org/about/news/postgresql-182-178-1612-1516-and-1421-released-3235/