The Conti Playbook Leak: Your Questions, Answered
Written by: ceren
Written by Gokcen Tapkan
Additional Contributor Yavuz Han
Edited by Haley Williams
The Conti ransomware gang is one of the most ruthless and greediest ransomware groups of all time, with its ransomware demands surging as high as $25 million. It certainly hasn’t discriminated against its 400+ targets, either, as attacks linked to the group are connected to hospitals, government organizations and law enforcement agencies.
Not only has the recent compromise of the Conti playbook sparked interest across the cybersecurity community, it has confirmed suspicions regarding the indicators of compromise (IOCs). Still, many questions remain: Who exactly is Conti? Who is responsible for leaking the group’s strategy and tactics? What did we learn from the playbook?
Q1: Which recent attacks is the Conti ransomware gang notorious for?
1. Ireland’s Health Service Executive
Ireland’s Health Service Executive (HSE) was hit by a ransomware attack on May 14 , 2021. The information systems that regulate all local and national health services were affected, despite precautionary measures taken to shut down systems. The Conti Ransomware group claimed responsibility for the attack and, according to the media, hackers demanded $20 million.
2. The City of Tulsa
The City of Tulsa, Oklahoma was hit by a Conti ransomware attack in early May. As a precautionary measure, they shut down all networks. Still, the cyber attack disrupted Tulsa’s online bill payment systems, utility billing, and email, as well as the websites for the City of Tulsa, the Tulsa City Council, Tulsa Police, and the Tulsa 311.
3. Broward County Public Schools (BCPS)
The Conti Ransomware group was also behind the attack against Broward County Public Schools in early March. According to the media, hackers demanded $44 million from BCPS. After negotiations failed, the threat actors published alleged screenshots of the ransom negotiation. As a result of the negotiations, the ransom fee was reduced to $10 million.
Q2: How was Conti’s playbook compromised?
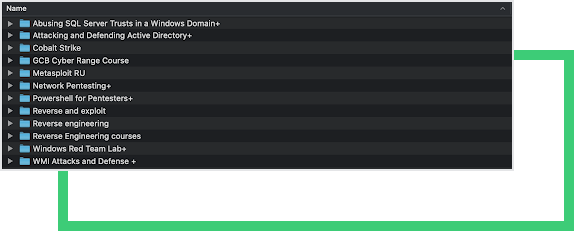
Recently, a vengeful, underpaid affiliate of Conti leaked the group’s playbook on a Russian hacking forum, XSS. The documents included training materials, tools leveraged in lateral movement and IP addresses of the Command & Control (C2) servers. A larger file archive from Conti also recently surfaced on Pastebin, which featured training videos, hacking manuals, and more tools.
Q3: What do we now know about Conti’s attack structure?
The playbook details a typical ransomware attack. Conti’s Ransomware as a Service (RaaS) model consists of the threat actors gaining initial access to the target, and then farming out the post-exploitation phase to its affiliates. The process initiates with a possible spear-phishing attack that loads a Cobalt Strike beacon.
The majority of the playbook is devoted to gaining network privileges, which is accomplished by hunting down administrators. Using the sharefinder tool, the enhanced reconnaissance stage enumerates domains, and finds domains shares.
Information around finance, accounting, clients and projects is prioritized, and the goal is to gain as much knowledge around the PII database as possible. Here, the malicious actors look for both read and write permissions. In the case it is a read-only permission, affiliates can pull the data off and sell on the darkweb.
There is also a long section devoted to extracting hashes and plain passwords. Kerberos attack leverages Kerberoast tool for extracting hashes and later on sending it for brute-forcing. Another effort for extracting passwords is the use of the Mimikatz tool. With Mimikatz, once you are elevated, you can dump the password or hashes from memory.
Depending on where you land, you can dump all the passwords (cleartext, password hashes, etc.) that are logged onto the server. If you are an administrator of the host, you may also take the memory and dump it. Once the domain controller passwords are obtained, the affiliate is instructed to install Anydesk on all abandoned hosts, and Atera on the rest.
Anydesk is installed in the silent mode not to display any error messages. Affiliates are also instructed to identify network-attached storage (NAS) and other backup directories. This increases the chances of getting the ransomware payment. The playbook also recommends opening a MEGA.io account to house and store exfiltrated material.
As soon as the data is uploaded, specific keywords are searched for to gain leverage in the ransomware negotiations. This includes cyber, policy, insurance, endorsement, supplementary, underwriting, terms, bank and statements.
Afterwards, the content is downloaded to a dedicated server and file systems are locked. the file system. The affiliate is instructed to execute the encrypter, killing all the processes that interfere with the opening of files, shutting down all virtual machines.
Q3: What tools do ransomware groups leverage, according to the Conti playbook?
The playbook can be thought of as a manual for Cobalt Strike, a proprietary product used for read-teaming-operations. Of course, cracked versions are also out there. The attacker initially deploys an agent named “beacon” to the victim machine. The beacon is fileless, meaning it does not create any file on the disk and relies solely on memory.
That way, it can then execute shell commands. Because it is well-written, robust and and easily adaptable, the beacon implant has proven popular among targeted attackers and criminal users. It’s often delivered through spear-phishing emails. Besides CobaltStrike, many open source tools are also found in the playbook, including sharefinder, powershell , kerberoast, etc.
Q4: What are the IoCs and commonly exploited vulnerabilities found in the playbook?
Ransomware is the most common among the most harmful security threats facing today’s organizations. Having an accurate, up-to-date feed of IoCs is an integral component of any organization, as gangs are leveraging a combination of old and new vulnerabilities. Some of the leaked CC addresses include: 162.244.80.0/22, 85.93.80.0/20, 185.141.61.0/24, 185.141.62.0/23 and 82.118.20.0/22.
IoCs have been long studied by organizations including exploitations of vulnerable versions of FortiNet ( 5.6.3 build 1547(GA)). Known exploits for this vulnerable firmware include one critically rated vulnerability (CVE-2018-13379) and one highly rated vulnerability (CVE-2018-13374).
Zerologon
The Zerologon vulnerability begins with downloading a file so that a remote attacker can gain privileged credential material, or become a domain admin, from an unpatched Windows Domain Controller with just one click. A mimikatz addition is also referenced in the playbook.
PrintNightMare
The PrintNightMare vulnerability gives an authenticated attacker a way to gain system level access on vulnerable systems, which includes core domain controllers and active directory administrative servers. The vulnerability with the CVE -2021-34527 code allows anyone to create a local administrator, as long as an agent has initially the rights of a simple user.
Ms17_010
The Ms17_010 vulnerability is exploited on Windows Vista, Windows 7, Windows 8.1, Windows 10, Windows Server 2008, Windows Server 2012, Windows Server 2016, and Windows XP. Through this, an attacker can exploit and possibly take full control of a computer. In the playbook, the vulnerability is exploited to do various actions such as obtain a meterpreter session to run commands with admin rights.
Q5: What can we learn from the attack?
Conti is not the only ransomware group that is continuously revamping their training materials and using new exploits. It’s critical that today’s organizations follow suit. An outdated defense strategy predicated on the assumption that your firm has been breached or could be breached easily by a dedicated attacker.
An assume-a-breach approach concentrates on the aftermath of an attack and tries to limit the damage. A prepare-for-breach approach, on the other hand, focuses on the utmost prevention techniques, from phishing to patch management, to multi-factor authentication and hidden backups. Think proactively about your risk management approach, rather than reactively.
Put Yourself in the Mind of a Cyber Criminal
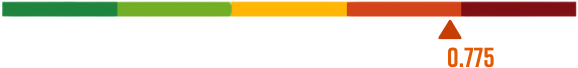
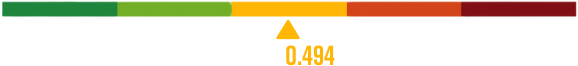
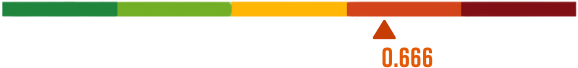
As observed earlier in the blog, recent ransomware attacks made by Conti yielded significant RSI™ ratings. Built from a hacker’s perspective, Black Kite’s RSI™ collects data from various open source intelligence (OSINT) sources including internet-wide scanners, hacker forums, the deep/dark web, and more to determine how susceptible a company and its third parties are to a ransomware attack.
Get a Free RSITM Rating
