Your company accounts may be breached. Find out with Free Account Breach Search.
Written by: Black Kite
Employees may use their same credentials (e-mail/username/password) used in their company accounts to register third-party services. If the third-party service is hacked, the company accounts will be exposed and your company may suffer a significant major attack.
For instance, the email addresses and unencrypted passwords of 10,000 public sector healthcare workers are exposed when an online-training service company, Embrace Learning, was hacked in 2016, a data breach that may lead a massive historical breach of millions of sensitive patient information, if some of those healthcare workers use their NHS credentials to register Embrace Learning .
Millions of stolen credentials are out there!
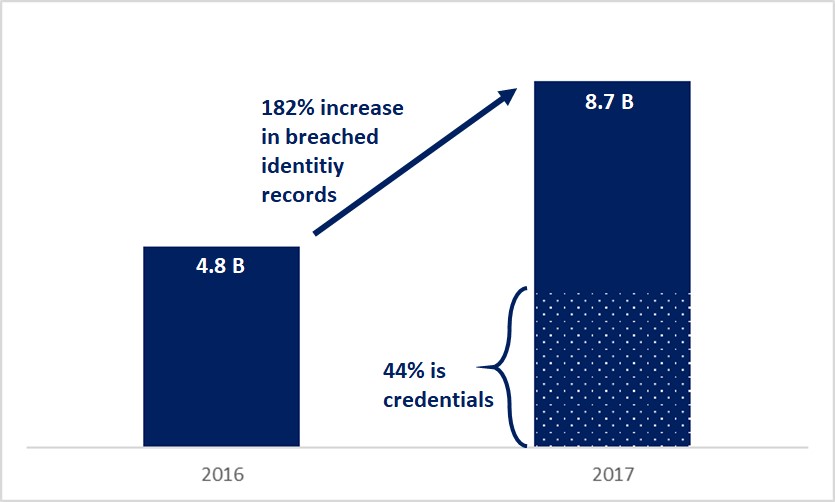
According to the 4iQ Identity Breach Report , 8.7 billion (detected and verified) raw identity-record data are on the surface, deep, and dark web in 2017, that is 182% increase compared to previous year. 44% of this data (around 3.8 billion) are usernames, passwords, and other credential information.
You may hack through credential stuffing
Credential stuffing is a method that hackers use to infiltrate a company’s system by automated injection of breached username/password pairs. We can see credential stuffing in 2017 – OWASP Top 10 critical web application security risks report under the second most critical risk: Broken Authentication.
Hackers use credentials to bypass anti-spam and firewall devices and access users’ accounts. Once inside the company network, they can send phishing emails or compromise company systems/data. Note that attackers just need to gain access to only a few account, or just one admin account to compromise the system. According to OWASP report, hackers do money laundering, social security fraud, and identity theft, or disclose legally protected highly sensitive information.
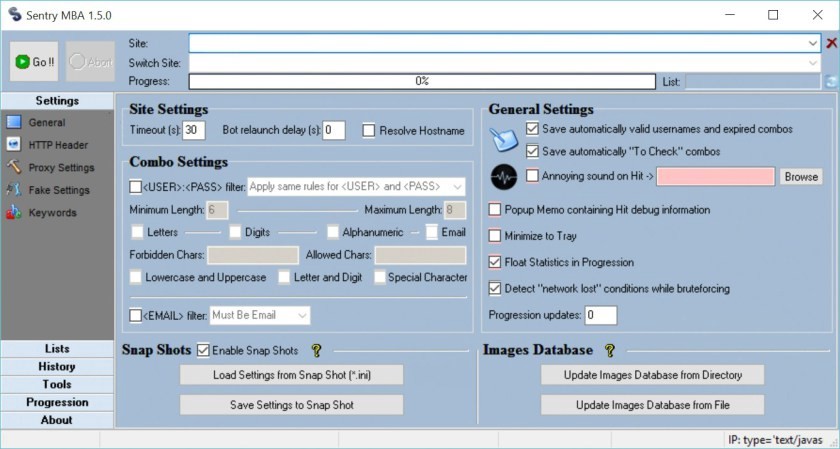
There are even some popular tools to ease credential stuffing. For instance, Sentry MBA can repeatedly try username/password list for a targeted website. It uses an IP address list to route the traffic through so that the source of login attempts vary. It even has built-in OCR capabilities for bypassing CAPTCHA-like counter-measures.
Most people use same username/password combination on multiple login sites (cross credential use). If a breach list of a site is acquired, the attackers can use the same list for another site by credential stuffing tools like Sentry MBA. The research shows that 1% to 2% success rate on cross credential use.
How bad is the situation?
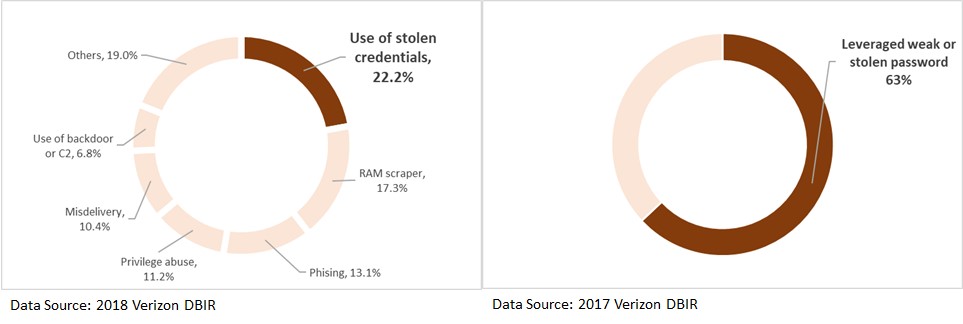
Use of stolen credentials is reported as #1 reason in 2018 Verizon Data Breach Investigations Report with being the cause of 22% of all breaches in 2017. 6 out of 10 confirmed data breaches in 2016 leveraged weak or stolen passwords.
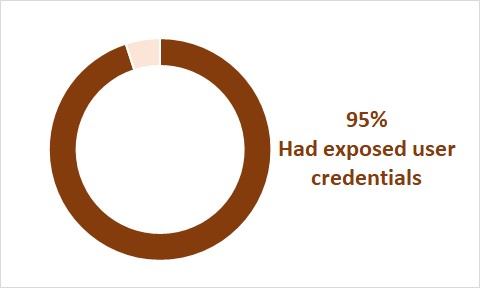
Black Kite conducted a survey, which reviews trends and insights from Cyber Risk Scorecard key data points that include detailed external security risk data from cyber risk scoring for 5,217 organizations across multiple industries and over one million active assets on the Internet, including web and network devices. Black Kite found a whopping 95% of respondents had exposed user credentials (for more information download Black Kite Cyber Security Risk Brief 2018).
Find out leaked credential with Black Kite’s Free Account Breach Search
Black Kite has one of the largest commercial databases of hacked credentials to uncover client exposure. One of the free services offered by Black Kite is Account Breach Search. It provides the statistics of the breached credentials of your company, the list of breached accounts and the source of the breach. Below is step-by-step usage of Account Breach Search Engine.
Step 1. Enter your company’s domain name and press Enter/Return and scroll down to see the results. Note that a single e-mail account can also be searched.
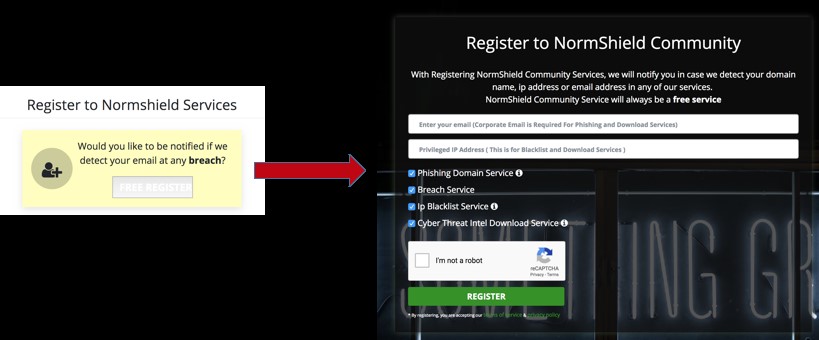
Step 2. If you would like to receive notification if one of your company account breached, click on Free Register button to join Black Kite Community and fill out the form (Note that you can see the results by simply scrolling down without registration). Black Kite only needs your corporate e-mail address, privileged IP address for IP Blacklist search (that will be shown automatically). Just check the free services about which you want to receive notification and click on Register button.
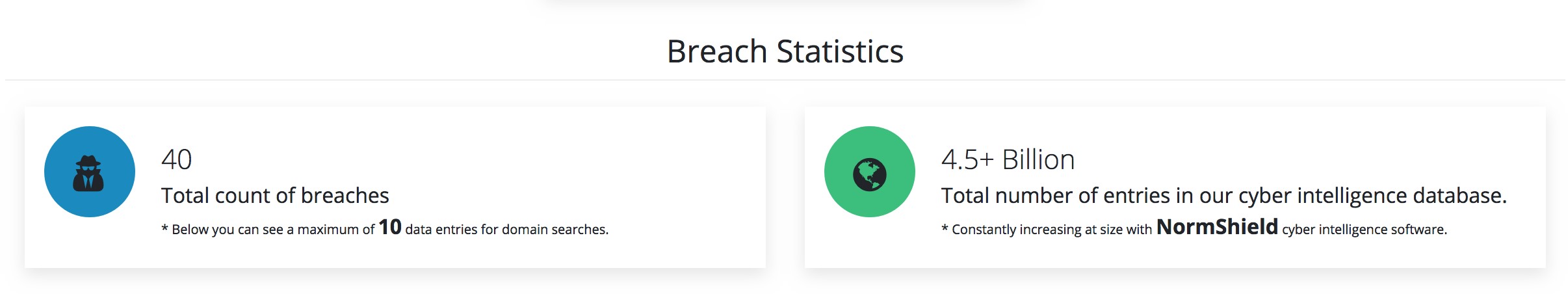
Step 3. Check your breach statistics. Breach statistics gives total number of breaches found. It also shows total number of entries in Black Kite’s cyber intelligence database.
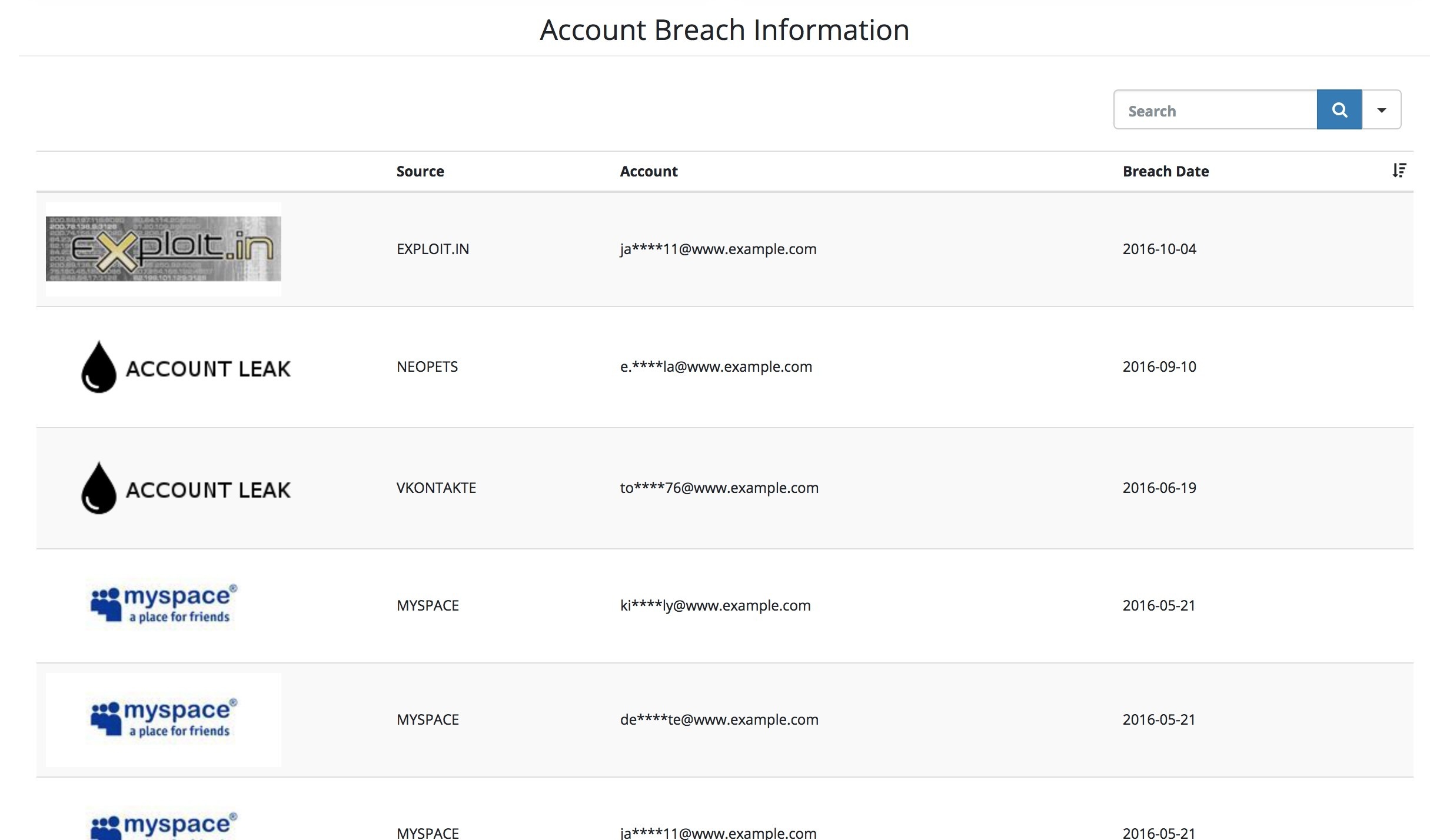
Step 4. See the sample set of breached accounts. For privacy, we only show a sample set of breached accounts in Account Breach Information section. It shows the source the breach is found, the breached account (partially masked for privacy) and the date of breach. You can filter the results with Search box and sort the results with respect to source, date, or account name.