Third-Party Risk Management from COBIT’s perspective
Written by: Black Kite
Since its release in 2012, COBIT 5 has become a good-practice framework for IT management and governance for enterprises. By following certain checkpoints in the framework, a company can create a good IT risk management. It’s not surprising that COBIT emphasize third party risk management considering major cause of recent data breaches are third parties. They have become the weakest link in the system.
What is COBIT?
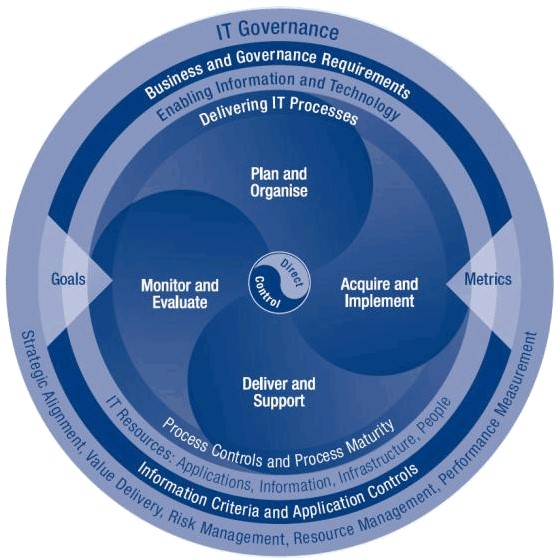
COBIT (Control Objectives for Information and Related Technologies) created by ISACA is an integrator framework many IT standards such as ISO 27001, COSO, ITIL, etc. It summarizes the key objectives of these guidance materials. Since the first version released in 1996, COBIT is well-accepted by an international material for enterprise IT management and governance with framework, process descriptions, control objectives, management guidelines, and maturity models provided.
What is 3rd-party cyber risk?
A recent survey conducted by Ponemon Institute reveals that 56% of companies have experienced a 3rd-party breach in 2017, which is an increase of 7% compared to previous year. Data breaches caused by third parties cost millions of dollars to large companies.
Third-parties include broad range of companies a company directly worked with such as data management companies, law firms, e-mail providers, web hosting companies, subsidiaries, vendors, sub-contractors, basically any company whose employees or systems have access to your systems or your data. However, third-party cyber risk is not limited to these companies. Any external software or hardware that you use for your business also poses a cyber risk. For instance, very recently UK-based TicketMaster experienced a data breach of potentially 40 thousand customer information because of a chatbot software. For more info on third-party cyber risk, check out our 2018 third-party cyber risk report here.
What COBIT’s view on third-party risk?
One of the main section in COBIT checkpoints is Delivery and Support (DS) where the second subsection (DS2) is all about how to manage third-party services. Here, third parties are defined as suppliers, vendors and partners. COBIT claims that control over the IT process of managing third parties can be achieved by:
- Identifying and categorising supplier services
- Identifying and mitigating supplier risk
- Monitoring and measuring supplier performance
and measured by;
- Number of user complaints due to contracted services
- Percent of major suppliers meeting clearly defined requirements and service levels
- Percent of major suppliers subject to monitoring
COBIT explains details how to manage third party relationships in DS section under four categories:
- Identification of all supplier relationships
- Supplier relationship management
- Supplier risk management
- Supplier performance monitoring
Steps to check COBIT-compliance
- Establish agreements with third parties. Agreements should be written clearly and should have references to COBIT.
- Check COBIT control points and determine which one of those should be met by the third party.
- Monitor compliance of the third-party
- Prior to work with a third party, complete a risk assessment
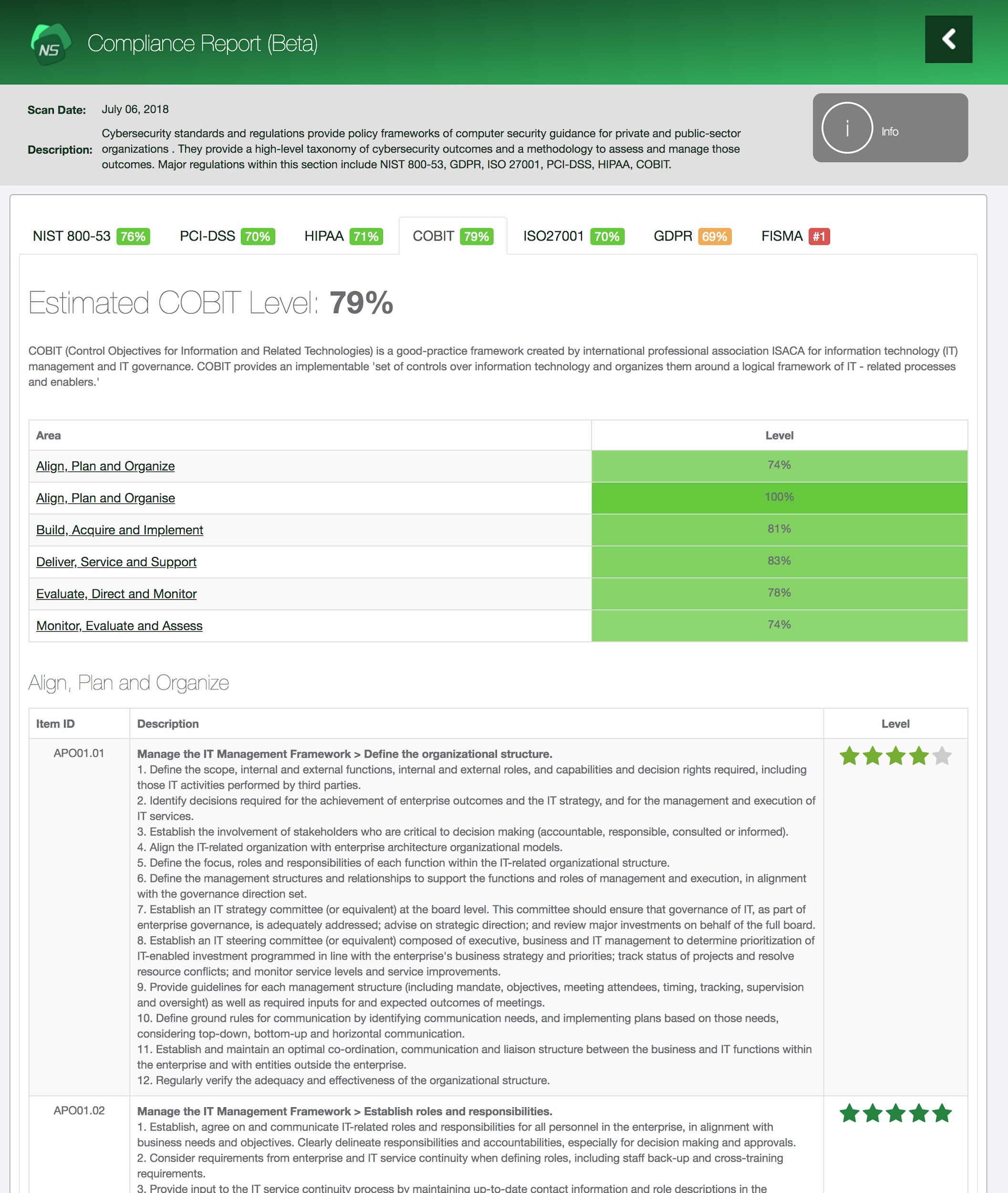
How to use Black Kite for third party COBIT-compliance
COBIT recommends to assess the risk of third-parties in DS. The risk assessment can be done in an old-school fashion questionnaire method. Unfortunately, some third-parties are not so eager to respond, questions might not cover all the risks, and the answers will be only depend on what the third-party knows about it IT structure.
Thus, Black Kite Cyber Risk Scorecard, with its benchmarking reports, provides risk scoring and ranking for companies and their third parties. Besides, it also check compliance to well-known cyber security frameworks including COBIT framework. Even prior to work with a third party, its COBIT-compliance can easily be checked with Black Kite Cyber Risk Scorecard. Act now and learn your company and related third parties here.