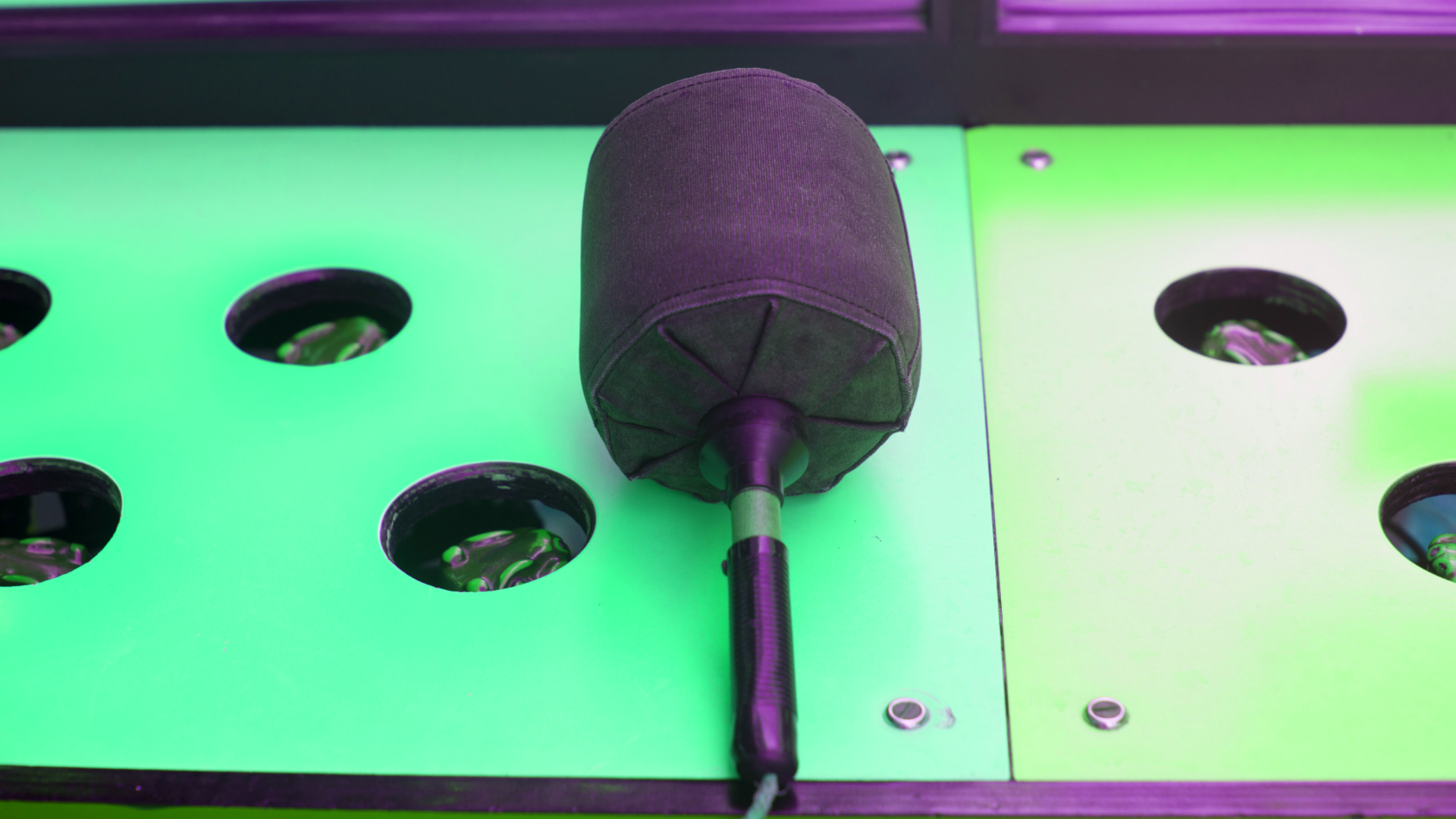
The “Whac-A-Mole” Game Between Cybercriminals and Security Teams
Written by: Black Kite
By Bob Maley, CSO, Black Kite
Another data breach, and another “wakeup call” for risk officers. Yet in the past five years alone, Equifax lost over $4 billion from one incident, Marriott was left accountable for 500 million stolen consumer records, and hackers gained access to over 100 billion social media accounts… making it clear that cybercrime history suggests otherwise.
That’s not to mention the past year alone. Just when we thought we couldn’t catch a break after the SolarWinds, Accellion and Microsoft Exchange security incidents, the Pulse VPN attack came to light. Instead of getting ahead of cybercriminals, we’re caught in a “Whac-a-Mole”-type situation with them and unfortunately, we’re falling behind.
Why Cybercrime Has Become Such a Major Problem in the First Place
I can’t say it enough: ignorance quickly becomes negligence, especially when it comes to cybersecurity. Despite the steady increase in attack frequency, 56% of Americans are unsure of what to do in the event of a breach. What’s even more alarming is that 77% of organizations do not have an incident response plan in place.
The unfortunate reality is that although digitization has rapidly accelerated throughout the past decade, cybersecurity has taken a back seat. While the recent major data breaches have finally started to shift the conversation, the Pulse VPN breach that immediately followed this month’s DNSA’s statement around prioritizing cybersecurity is proof that we need to act faster.
Is the ‘Right-of-Bang’ Approach Steering Us in the Wrong Direction?
As risk professionals, we know we should always prepare for the worst. However, consider this: it takes an average of 207 days to identify a breach and from there, 280 days to contain it. This means that by the time we come to understand the full magnitude of one incident, we’re knee deep in another.
In the same period it takes us to execute the observe—orient—decide—act (OODA) loop once, threat actors have completed the cycle several times. The key is agility, and cybercriminals are using it to their full advantage. Although their attacks are becoming more strategic, it’s time that we borrow a page from their playbook.
Signals Are Your Secret Weapon
Cybercriminals know what to look for. Victims of cybercrime all have one thing in common: something was missing in their cyber risk management framework. Too many times, this happens because even organizations that have made sound investments in their risk management strategy neglect to address their entire ecosystem including suppliers, partners and third parties.
Like “Whac-a-Mole”, cyber attacks will continue to pop up, no matter how many times you try to get rid of them. Unlike the game however, there are signals that we can leverage to help detect something is coming much sooner, to then take the steps necessary to stay left-of-bang.
In fact, impacted organizations were flooded with signals that preceded the Pulse Secure VPN attack, some of which dated back to 2019. Just as was the case with SolarWinds, these all could (and very well should) have raised a red flag for organizations to address, had they been doing their third-party due diligence properly.
The ultimate goal for security teams should be to have such a good cyber risk assessment and associated management framework in place, that an incident response plan is no longer even necessary. To do that, however, we have to become better at understanding the signals. Signals are always present, it’s our duty to detect and mitigate them.
The best way to detect signals is to look at them from a hacker’s perspective. Get started today with Black Kite.