1.2 Million Customer Records Leaked in GoDaddy Data Breach
Written by: Black Kite
Over one million customers’ accounts were compromised last week in a third-party data breach that targeted GoDaddy, a web host and domain registrar with over 20 million customers. Although many remediation steps have been taken by the organization, the leaked credentials and exposed WordPress website content is a major threat to many companies given the criticality of the vendor.
History tends to repeat itself when it comes to cyberattacks, and one incident can become a pivotal point for any company. Recent SolarWinds, Accellion and Kaseya supply chain cyber attacks are proof of how devastating a third-party breach can become. Not only that, this isn’t even the first time GoDaddy has experienced a security incident.
The Timeline: What led up to the GoDaddy breach?
In 2019, criminals created 15,000 subdomains using hundreds of hijacked GoDaddy accounts, seeking to imitate popular websites and redirecting potential victims to spam pages selling snake oil goods. In May of last year, GoDaddy warned some of its clients of an unauthorized party logging into their hosting account via SSH back in October. Most recently, GoDaddy was caught injecting JavaScript into the websites of US clients without their permission earlier this year.
Who was affected by the GoDaddy breach?
Last week, GoDaddy issued a statement to the Securities and Exchange Commission (SEC) indicating that an attacker gained access to approximately 1.2 million email addresses belonging to active and inactive managed WordPress users. Upon discovering suspicious activity on the Managed WordPress environment, the hosting company immediately started investigating and blocked the threat actor from its network.
The preliminary investigation has revealed the threat actor infiltrated GoDaddy’s systems in early September through a compromised account with provisioning rights. The privileged access enabled the attacker to possibly set up and automatically configure new sites. The attacker also had access to:
- WordPress admin passwords at the time of provisioning
- Database usernames and passwords for both active customers and inactive accounts
- SSH File Transfer Protocol (SFTP) usernames and passwords
- Private SSL keys for some customers: While a public SSL key is communicated to the client through an SSL certificate, a private SSL key is kept confidential and used to identify the server machine.
Looking Ahead: Which looming threats should affected customers be aware of?
As a critical third-party vendor, GoDaddy is now taking the steps to remediate the compromises listed above. The organization has started regenerating SSL certificates, resetting SFTP and WordPress administrative passwords, and more. Still, there are some threats that customers should remain extremely cognizant of.
Credential Stuffing
Credential stuffing is now an obvious threat to victims given the 1.2 million active and inactive username and password combinations that are in the hands of cyber criminals. New to the OWASP Top 10, credential stuffing a method hackers leverage to infiltrate a companys’ system through an automated injection of breached username/password pairs.
Although passwords have been reset since GoDaddy discovered the compromise, it is likely that an employee may use the pair elsewhere in the companys’ network. Hackers may use these credentials to bypass anti-spam/firewall devices and access users’ accounts.
Once inside the company network, hackers can send phishing emails or compromise company systems and/ or data. By gaining access to just one account, threat actors can then engage in money laundering, social security fraud, identity theft, or disclose legally protected highly sensitive information.
Phishing
If credential stuffing attacks go unsuccessful, hackers still have ways to infiltrate a companys’ network. These days, companies must be particularly vigilant against phishing attacks. In this case it is not a matter of unauthorized access, given that all the passwords have been reset. However, the data breached may open other doors to new attacks.
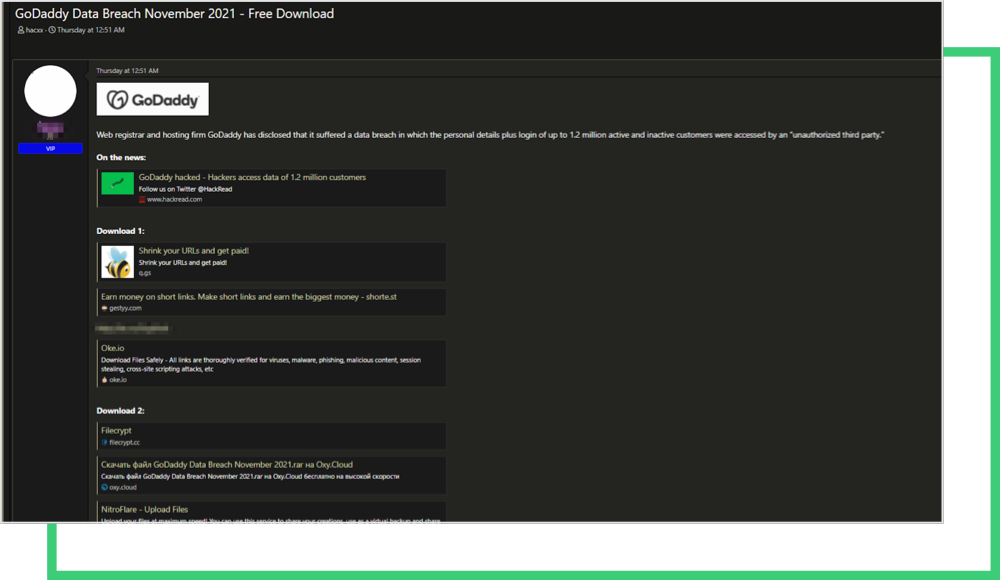
Black Kite Research found GoDaddy customer credentials have already been put for sale on dark markets.
Black Kite has one of the largest commercial databases of hacked credentials, which uncovers client exposure.
Malicious Code Placement into WordPress
Malicious code placement is another potential threat that could have been executed by the threat actors any time between the incident (September 6) and the date of discovery (November 17). If the compromised passwords were still in use, card skimmer code could have been placed into the WordPress sites either directly or through a third-party malicious javascript library. There is a high likelihood of success here, considering a significant percentage of the passwords weren’t changed after the first provisioning.
The British Airways breach is a good example for demonstrating how disastrous card skimmer malware could be. Hackers installed the malware on British Airways’ website in 2018 through a third-party javascript. Payments through the airlines’ website and mobile app were stolen over the course of three weeks.
As a result, British Airways was eventually fined £20 million by the UK’s data protection authority for failing to meet data security, which led to unauthorized access of personal and payment card information relating to more than 400,000 of its customers.
Misconfigured Servers
A simple misconfiguration of a page that transfers sensitive information could also put a website’s users’ data at risk. Through accessed WordPress code, an SSL-protected page could simply be configured to be without SSL, or a login form could be set as insecure, such as without bot detection, and so forth.
How can GoDaddy customers protect themselves?
- Even though GoDaddy is reaching out to its customers directly, an essential first step if the web host is one of your vendors.
- Reset GoDaddy-hosted admin passwords, and report any suspicious activity to the IT team.
- Take all necessary steps to avoid a phishing attempt by checking employees’ cybersecurity awareness and monitoring for credentials on breached platforms.
- Check the configurations on GoDaddy-hosted pages including SSL configurations (enabled/disables, cipher suites), and review your code from Application Security perspective.
- Keep an eye on third-party javascript libraries used on your web site, and confirm that legitimate Content Delivery Networks are used.
We know how painstaking vendor risk management can be. Let our 25 billion lines of global cyber data do the brunt work for you. Learn more with a free cyber risk assessment of any critical vendor within your cyber ecosystem.
Free Cyber Rating
