Strong Cybersecurity Talent: The Biggest Need for Companies in 2022
Written by: Black Kite
By Haley Williams, from the perspective of Jeffrey Wheatman, Cyber Risk Evangelist
Over the several years, the talk of the town in hiring has been “where can you find high quality cyber talent?” “Good quality hires are too hard to find.”
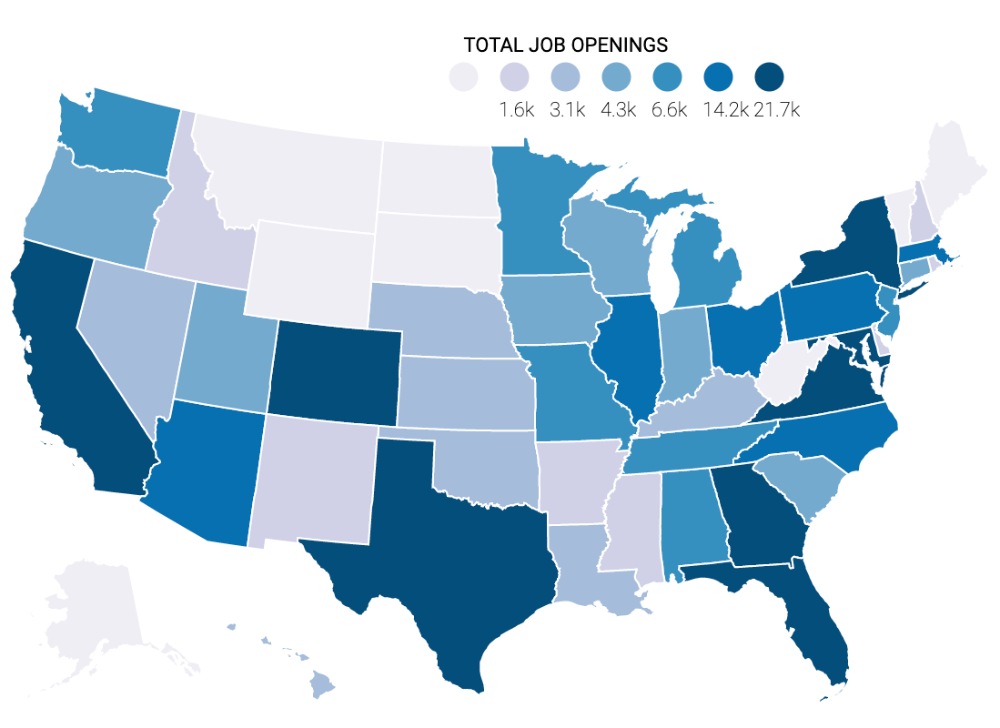
According to CyberSeek, there are currently 597,767 cyber security positions left unfilled across the United States, with the majority of the cybersecurity job openings concentrated in California, Texas, and Florida.
Looking in the for the Wrong People
And while there is truth to that statement, (we all know how difficult the job market for hiring has been lately), there are issues with the current approach. Companies may be looking for the wrong type of talent – seeking the proverbial purple squirrel. Organizations are looking for specific, traditional job titles and career histories, such as:
- Network Security
- Data Security
- Application Security
But with the current digital business models and architectures, we need people that are more generalists, and that can focus more on the full ecosystem rather than an extremely specific technology or tool.
For example, if you have a cloud application, you cannot focus on merely one of the technical platforms, because your risk, and therefore your response, needs to be spread across the cloud. A good metaphor for this approach is the parable The Blind Men and the Elephant, provided below.
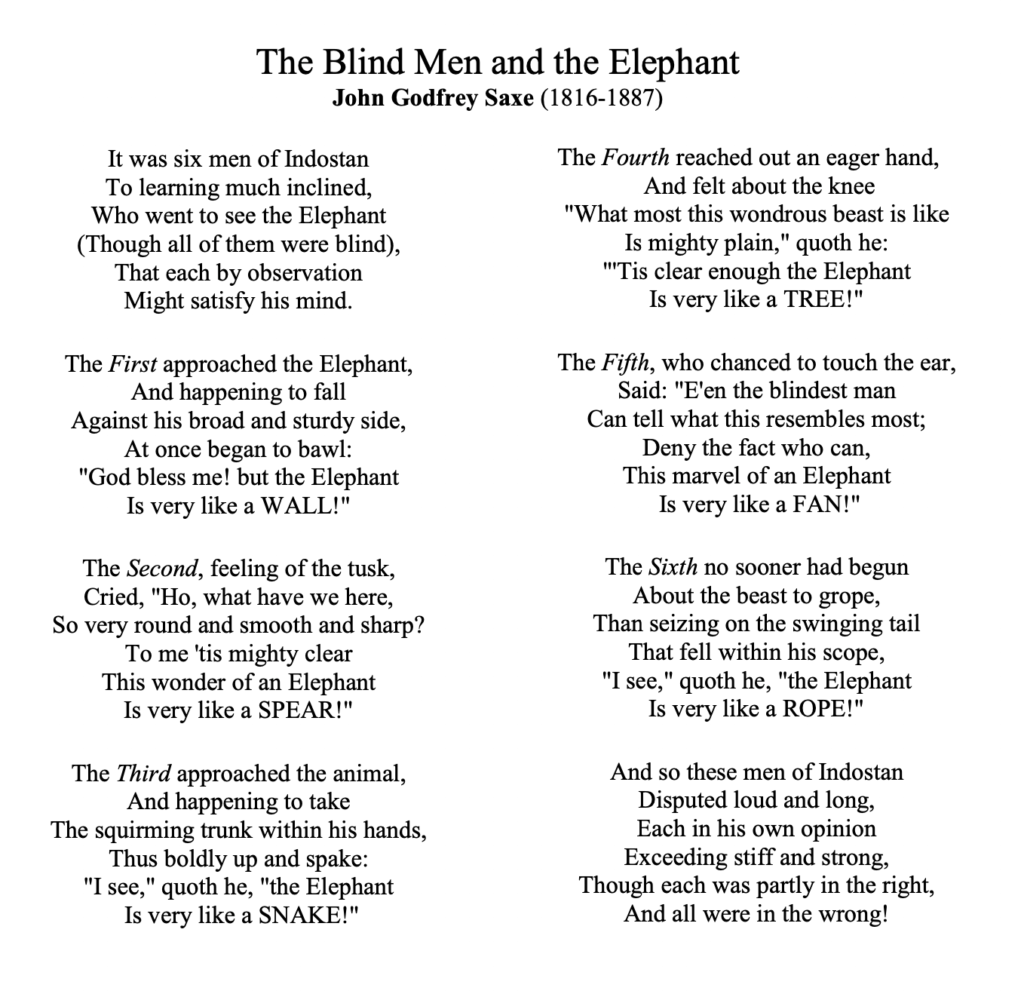
As seen in the parable, people need to step further away from the problem or subject at hand rather than staying so close, in order to see and understand the full picture. Focusing on the tiny, specific things allows your team to miss the larger story at hand. Hiring cyber professionals that can successfully monitor and hold jurisdiction over a variety of platforms and technologies allows for a stronger team overall.
Looking With the Wrong Methods
Another issue is that hiring managers, HR, and team leaders are often looking for candidates using outdated methods. Old-school recruiting keywords and techniques often exclude candidates that are aiming to be more solutions-focused and possess highly desired soft skills. Recruiters and hiring managers must establish new ways to structure job descriptions to better match the current job landscape of cyber.
Jeff Orloff of Security Week said it well, “Security leaders must approach staffing in broader and deeper ways. These days, it isn’t enough to rely only on those with degrees, certifications and past experience. By expanding the labor pool to those who are self-taught or have a knack for cybersecurity—and training them for specific roles—the universe of candidates expands exponentially.”
Looking in the Wrong Places
While there might be a gap in pure cyber security people specifically, there are other people that have strong risk management skill sets and capabilities out there looking for jobs. Not having a pure technical background should not be a deal breaker, and here’s why.
Financial backgrounds can come in and do financial risk management. Compliance and audit-based backgrounds can understand all of the regulations and requirements put in place for security measures. People that are strong communicators and have other strong soft skills can easily learn the technology versus the other way around. Of course, there will always be roles that require specific technical skill sets, but there is room to expand in hiring efforts nonetheless.
According to the (ISC) Cyber Security Workforce, the global cybersecurity workforce needs to grow 65% to effectively defend organizations’ critical assets.
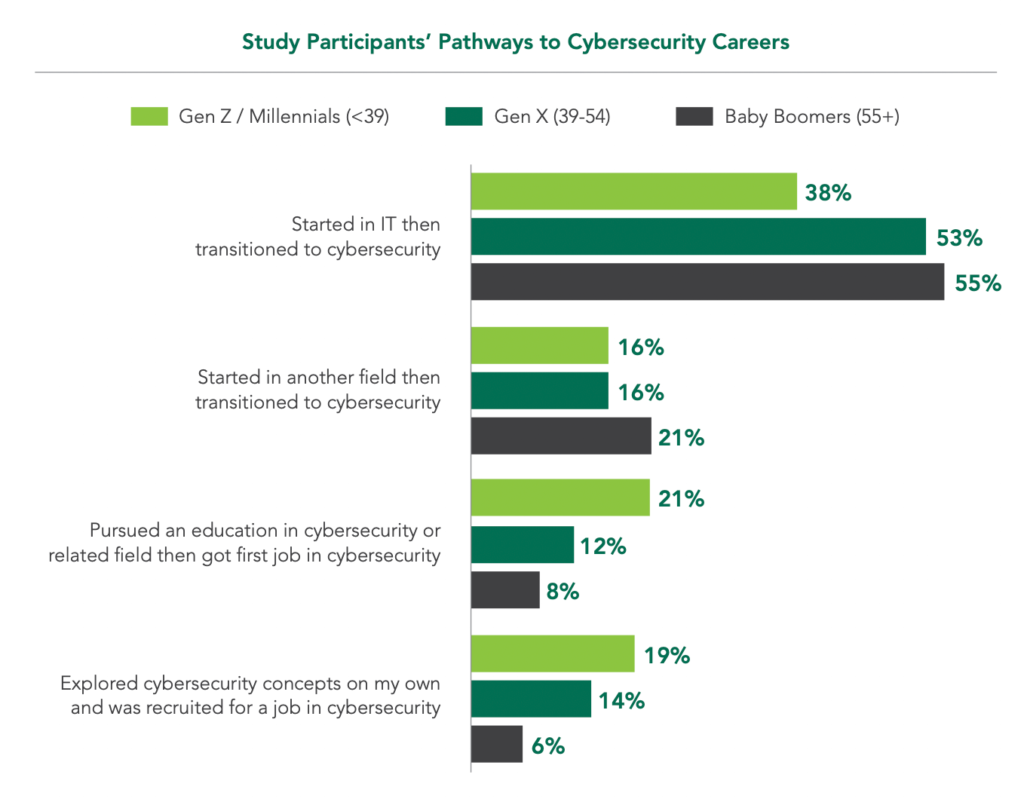
Within the study they conducted, they analyzed the way the pathways to cybersecurity careers are evolving. Now, more than half of current cybersecurity professionals actually got their career start in something other than IT.
What if These Hires Don’t Want Typical Corporate Jobs?
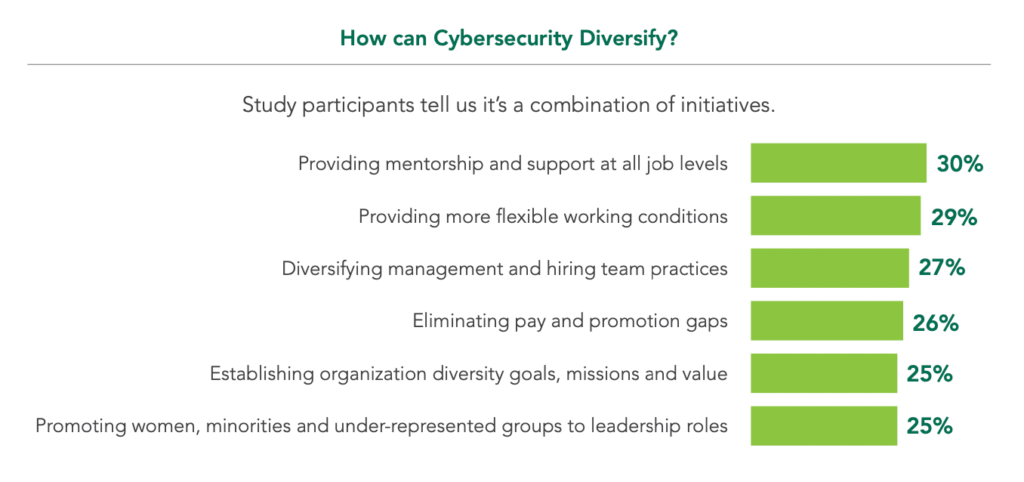
After attending a handful of the technical security events, such as Black Hat, RSA, or Defcon we sometimes hear that the strongest hires aren’t looking for a traditional corporate security job. While that may be true, there are ways to flex to make the jobs more enticing to the up and coming security professionals.
- Allow flexibility. No one wants to be doing repetitive work day in and day out. Allow these hires to be experimental with their practices, trying new things and expanding the status quo of what it means to implement security protocols. While the environment may be corporate, the job itself can hold some flexibility and freedom.
- Encourage continuous education. At some larger tech companies, employees are encouraged to dedicate a small % of their work week to a personal project or professional development learnings. While this may or may not turn into something tangible or fruitful for the company itself, it provides job enrichment which can in turn create a happier, more productive employee.
“I’ve Done All These Things and Still Can’t Hire the Right People – What’s Next?”
When efforts have been exhausted to hire enough people, one solution to turn to is automation within risk management. For example, if a team was to manually review every single questionnaire for thousands of partners, odds are the questionnaires aren’t getting reviewed in a timely manner – if at all.
Using automation to take the burden off of a small team allows that team to focus on projects and issues that do require manual attention, rather than wasting time on tasks that can be easily automated.
For example, Black Kite’s Unique Parser can parse through reports and policies in minutes, mapping to well known standards and frameworks. Additionally, manually completing risk assessments can take a month’s time, but when automated, a platform such as Black Kite can produce a vendor risk assessment in several minutes, tapping open source data on millions of companies worldwide.
Could an automated third party risk management program be right for you? We invite you to try a demo with a member of the Black Kite team.
Schedule a Demo Today
